
FileMaker
®
Pro 14
User’s Guide
© 2007–2015 FileMaker, Inc. All Rights Reserved.
FileMaker, Inc.
5201 Patrick Henry Drive
Santa Clara, California 95054
FileMaker and FileMaker Go are trademarks of FileMaker, Inc. registered in the U.S. and other countries. The file folder logo
and FileMaker WebDirect are trademarks of FileMaker, Inc. All other trademarks are the property of their respective owners.
FileMaker documentation is copyrighted. You are not authorized to make additional copies or distribute this documentation
without written permission from FileMaker. You may use this documentation solely with a valid licensed copy of FileMaker
software.
All persons, companies, email addresses, and URLs listed in the examples are purely fictitious and any resemblance to
existing persons, companies, email addresses, or URLs is purely coincidental. Credits are listed in the Acknowledgements
documents provided with this software. Mention of third-party products and URLs is for informational purposes only and
constitutes neither an endorsement nor a recommendation. FileMaker, Inc. assumes no responsibility with regard to the
performance of these products.
For more information, visit our website at http://www.filemaker.com.
Edition: 01
Contents
Chapter 1
Introducing FileMaker Pro 7
About this guide 7
Working with FileMaker Pro 7
FileMaker Pro documentation 7
FileMaker Pro Help 7
Getting Started tour 8
Starter Solutions 8
Suggested reading 8
FileMaker Pro overview 8
Using layouts to display, enter, and print data 9
Finding, sorting, and replacing data 10
Protecting files 11
Automating tasks with scripts 11
Sharing and exchanging data 12
Saving and sending data in other formats 12
Chapter 2
Using FileMaker Pro 13
About fields and records 13
Opening and closing files 15
Opening multiple windows per file 16
Saving files 17
About modes 18
Using the status toolbar 18
Viewing records 19
Selecting the current record 21
Moving through records 21
Adding and duplicating records 22
Adding and duplicating related records 23
Deleting records 24
Entering data 24
Selecting a field 24
Entering and changing data in fields 25
Working with data in Table View 26
Displaying data in Table View 26
Working with records in Table View 27
4
Finding records 28
Performing quick finds in Browse mode 28
Making find requests in Find mode 29
Finding data in related fields 31
Viewing, repeating, or changing the last find 31
Saving find requests 32
Deleting and reverting requests 32
Hiding records from a found set and viewing hidden records 32
Finding and replacing data 32
Sorting records 32
Previewing and printing files 33
Previewing data on a layout 34
Printing records 35
Printing table and field information 35
Printing the relationships graph 35
Backing up files 36
Setting preferences 36
Chapter 3
Designing and creating solutions 37
Planning a solution 37
Creating a FileMaker Pro file 41
Creating a file using a Starter Solution 41
Creating a new file 42
Creating and changing fields 43
About naming fields 43
About choosing a field type 44
Creating and changing fields in the Field Picker dialog box 46
Creating and changing fields in Table View 47
Creating calculation fields 48
Creating summary fields 49
Using supplemental fields 50
Setting options for fields 50
About indexing and storage options 52
Creating database tables 53
Creating layouts and reports 54
About layout types 56
Creating Labels and Envelopes layouts 58
Working with layout themes 60
Working with layout object, part, and background styles 61
Setting up a layout to print records in columns 63
Setting up columns in a layout 64
Changing the width of columns 65
Working with objects on a layout 66
Organizing data with panel controls and popovers 66
Using the Inspector to format objects 68
Using tools to precisely position objects 69
Selecting objects 71
5
Working with fields on a layout 72
Placing and removing fields on a layout 72
Setting up fields to display checkbox sets and other controls on a layout 74
Deciding where to place related fields 75
About merge fields 75
Formatting field data on a layout 76
Allowing or preventing entry into fields 78
Working with layout parts 78
About layout part types 80
Creating and editing charts 81
Creating a chart 82
Editing a chart 83
Chapter 4
Working with related tables and files 84
About relationships 85
Relational database terminology 87
About the relationships graph 88
About match fields for relationships 88
Types of relationships 88
Working with the relationships graph 93
Creating relationships 94
Changing relationships 94
About lookups 96
Creating lookups 96
Editing lookups 97
Chapter 5
Sharing data 98
Sharing databases on a network 98
Enabling file sharing and hosting files 99
Opening shared files as a client 101
Opening shared databases remotely using a URL 102
Closing a hosted file 102
Sharing files with FileMaker Go clients 103
Uploading files to FileMaker Server 103
Importing and exporting data 103
Supported import/export file formats 103
Setting up recurring imports 103
ODBC and JDBC 104
Methods of importing data into an existing file 104
About adding records 104
About updating existing records 104
About updating matching records 105
About the importing process 105
Converting a data file to a new FileMaker Pro file 106
About the exporting process 107
6
Working with external data sources 108
Saving and sending data in other formats 109
Sending email messages based on record data 109
Publishing solutions on the web 109
Chapter 6
Protecting files 110
Protecting databases with accounts and privilege sets 110
Accounts, privilege sets, and extended privileges 111
About the predefined accounts 112
About the predefined privilege sets 113
Planning security for a file 114
Password-protecting a file 116
Creating accounts and privilege sets 116
Viewing accounts 117
Creating and editing accounts 117
Creating accounts that authenticate via an external server 118
Creating and editing privilege sets 118
About enabling record-level access 119
Viewing extended privileges 120
Authorizing access to files 120
Security measures 121
Enhancing physical security 121
Enhancing operating system security 121
Establishing network security 122
Backing up databases and other important files 122
Installing, running, and upgrading antivirus software 123
Chapter 7
Using FileMaker Pro Advanced 125
FileMaker Pro Advanced features 125
Developer Utilities 125
Runtime solutions 125
Binding the solution 126
Converting and upgrading previous solutions 126
Distributing runtime solutions 126
Kiosk mode 129
Custom functions 129
Custom menus, menu items, and menu sets 130
About custom menus 131
About custom menu items 131
About custom menu sets 132
Debugging scripts 132
Monitoring expressions 133
Documenting database schemas 134
Index 136

Chapter 1
Introducing FileMaker Pro
FileMaker
®
Pro
is the leading workgroup software for quickly creating and sharing solutions adapted
to your business needs. Powerful features, broad platform support, and an easy-to-use interface
make FileMaker
Pro indispensable for anyone in business, government, and education who needs
to effortlessly manage all their information on iPad, iPhone, Windows, OS
X, and the web.
About this guide
This User’s Guide contains an introduction to FileMaker Pro features and provides step-by-step
instructions on the most common FileMaker
Pro tasks. You will need to refer to FileMaker Pro
Help for details and for information on more advanced product features.
To send your feedback on this guide, see
http://www.filemaker.com/company/documentation_feedback.html.
Working with FileMaker Pro
FileMaker provides several ways to help you use FileMaker Pro.
FileMaker Pro documentation
To find documentation for FileMaker Pro and other FileMaker products:
1 In FileMaker Pro, choose Help menu > Product Documentation.
1 To learn about, view, or download additional FileMaker documentation, visit
http://www.filemaker.com/documentation.
FileMaker Pro Help
FileMaker Pro Help provides comprehensive step-by-step instructions on FileMaker Pro features.
You can open Help from the Help menu in FileMaker
Pro.
There are three ways to access Help:
1 Browse the Help table of contents to locate topics by subject.
1 Search for particular topics by entering keywords.
1 Get information about the currently displayed dialog box by pressing F1 (Windows) or
Command-? (OS
X). Some dialog boxes display a (Windows) or (OS X) button or a
Learn More link, which you can also use for getting information about the dialog box.
To print a Help topic:
1 Windows: In the FileMaker Pro Help window, click Print.
1 OS X: In the FileMaker Pro Help window, click or , then choose Print.

Chapter 1 | Introducing FileMaker Pro 8
Getting Started tour
You can explore FileMaker Pro through the interactive Getting Started tour. Practice creating,
modifying, and deleting records; and learn about searching for data values and sorting records,
displaying data in charts and reports, and importing and exporting data between files. You'll also
get to know the rich features FileMaker
Pro provides for creating your own custom solutions.
To access the tour, choose Help menu > Product Documentation > Getting Started Tour.
Starter Solutions
FileMaker Pro includes Starter Solutions—pre-designed, customizable solution files for business,
education, and personal purposes—that you can use to quickly get started designing your
FileMaker
Pro solutions. Starter Solutions take advantage of the best new FileMaker Pro features.
Whenever you start creating solutions, check the list of Starter Solutions to see if one is available
that suits your needs.
You can access Starter Solutions when you open files (see “Creating a file using a Starter Solution”
on page 41).
You can find more information, tips, and solution ideas on the FileMaker website at
http://www.filemaker.com.
Suggested reading
Here are some suggestions for using the documentation to help you learn how to do specific tasks
in FileMaker
Pro.
FileMaker Pro overview
With FileMaker Pro you create solutions—one or more files containing database tables, layouts,
scripts, and associated data that together solve one or more specific problems, such as tracking
customers or invoices.
You can create a simple solution consisting of just one table, such as for customer information, or
you can create a complex solution with relationships and multiple tables. For example, a complex
solution relates two tables based on a single common value, such as a serial number or an ID
number.
Type of user Suggested reading
Data entry person Chapter 2, “Using FileMaker Pro,” in this guide
Small business owner or educator
who creates a basic solution to
start, then improves it over time
Chapter 3, “Designing and creating solutions,” in this guide.
As features are added to the solution, refer to Help.
Database administrator 1 All chapters in this guide
1 Help, for information on advanced topics
1 FileMaker ODBC and JDBC Guide and FileMaker SQL Reference
New FileMaker Pro user 1 Installation and New Features Guide for FileMaker Pro and FileMaker Pro
Advanced
1 All chapters in this guide
User upgrading from a previous
version
1 Installation and New Features Guide for FileMaker Pro and FileMaker Pro
Advanced
1 Help, for information on converting files from FileMaker Pro 11 and earlier

Chapter 1 | Introducing FileMaker Pro 9
You can organize your solutions as a single table in a single file, as multiple tables in a single file,
or as multiple tables in multiple files.
You create solutions using FileMaker Pro on a Windows or Mac computer. Or use FileMaker Pro
Advanced for additional development and customization tools. You can then work with your
solution on a computer using FileMaker
Pro, or run the solution on iPad or iPhone using the
FileMaker
Go app. To access your solution from a web browser, use FileMaker Server with
FileMaker
WebDirect™.
For more information, see chapter 3, “Designing and creating solutions.”
Note If your solution was developed using FileMaker Pro Advanced, you may see customized
menus or tooltips for layout objects. For an overview of these features, see
chapter 7, “Using
FileMaker Pro Advanced.”
Using layouts to display, enter, and print data
FileMaker Pro layouts determine how information is organized for viewing, printing, reporting,
finding, and entering data. Layouts do not store your data—they just display it.
FileMaker Pro files can have many different layouts, which display data in a variety of ways. Within
one file you can design separate layouts for entering data, reporting summaries, printing mailing
labels, displaying data graphically in charts, working with a file in a web browser or on a touch
device, and so on. You can change a layout’s design without affecting the data or other layouts in
the file. When you change the data in a field, the changes are reflected in the same field on all the
layouts in the file.
In a layout, you choose, arrange, and modify fields and field labels; create reports; add buttons to
initiate scripts; add graphics and text; and specify printing options.
A solution consisting of one table
A solution consisting of multiple tables, with a
portal to display records from a related table
Portal

Chapter 1 | Introducing FileMaker Pro 10
Not all information needs to be stored in your FileMaker Pro file. For example, you can add a web
viewer to display a web page on a layout, or use data that’s stored externally in a container field
on a layout. There are some restrictions for displaying web content in FileMaker
Pro.
Choose different layout types in the New Layout/Report assistant. Use these different layout types
for various purposes, like displaying a data entry screen on a computer or an iPad, or printing a
totaled sales report or formatting data as mailing labels. You can customize each layout further by
using the design tools that are available in Layout mode.
For more information, see “Creating layouts and reports” on page 54.
Finding, sorting, and replacing data
Features for finding, sorting, and replacing data allow you to manipulate your data in many ways.
You can find records that meet criteria you specify, such as records entered on a certain date or
addresses in a particular city. You can open another window in order to perform different searches
on the same data.
You can rearrange records in order to view or print them in a different sequence. For example, you
can sort fields alphabetically, numerically, by date, or by a custom sort order.
Steve Williams
789 Ninth Avenue
New York, NY 10001
The same data can be arranged differently with multiple layouts
Juanita Alvarez 555-1234
Michelle Cannon 555-1234
Andre Common 555-1234
Marie Durand 555-1234
Jean Durand 555-1234
William Johnson 555-1234
John Lee 555-1234
Patrick Murphy 555-1234
Le Nguyen 555-1234
Kentaro Ogawa 555-1234
Mary Smith 555-1234
John Smith 555-1234
Sophie Tang 555-1234
Steve Williams 555-1234
Betty Wilson 555-1234
Contacts
Dear Sophie,
Thank you for ordering with us. We value
your business and appreciate the
opportunity to serve you.
If you have any questions about your order,
please call us—we want you to be satisfied
with your purchase.
Sincerely,
John Lee
Customer records sorted by last name
Chapter 1 | Introducing FileMaker Pro 11
You can search for and replace data across multiple fields, similar to the way you find and replace
data in word processing applications. You can also save a found set of records as a snapshot link
and send the link to another person.
For more information, see “Finding records” on page 28, “Sorting records” on page 32, and
“Finding and replacing data” on page 32.
Protecting files
You can restrict what users see and do in a file by defining accounts and privilege sets. Accounts
authenticate users who are attempting to open a protected file. Each account specifies an account
name and (usually) a password. Any user that cannot specify valid account information won’t be
able to open a protected file. A privilege set specifies a level of access to a file. Each account is
assigned a privilege set, which determines the level of access when someone opens a file using
that account.
Extended privileges determine the data sharing options that are permitted by a privilege set, such
as whether a privilege set permits users to open a shared file or view a solution in a web browser.
For more information about FileMaker Pro file security, see chapter 6, “Protecting files.”
Automating tasks with scripts
You can create scripts that simplify common tasks in FileMaker Pro. A script is a series of steps
that FileMaker
Pro performs to complete a task. These tasks can be simple (setting page
orientation so that reports print properly) or complex (preparing a customized mailing to targeted
customers).
As an example, a script can create a thank you email for customers who have made a purchase
during the past week. The script uses data stored in the solution to create an email message,
customizing the message based on each customer’s purchase history and contact information.
The script then switches to Preview mode and pauses so you can preview the message. After you
confirm that the message content is accurate, the script sends the message to customers. The
whole task is started by clicking a button that you defined on the layout.
For example, you can use a script to:
1 navigate a solution, by switching to another layout or mode when necessary
1 work with data, by finding and sorting data based on criteria that you specified in the script
1 access data, by importing required data from another table or data source
Scripts can incorporate conditional decisions (if-else statements) and perform repetitive tasks
(loop statements). And, you can use script triggers to run scripts when particular events occur
(such as when users enter a field, press a key, or add a new record to the file).
You create scripts in the Script Workspace window by selecting from a list of FileMaker Pro
commands—called script steps—and then specifying options and arranging the steps in the order
to perform the task. You can also view, edit, and manage all your scripts in this window.
Procedures for creating and managing scripts and a reference of all FileMaker Pro script steps,
script triggers, and functions (which are used in calculations) are available in Help.
Chapter 1 | Introducing FileMaker Pro 12
Sharing and exchanging data
A benefit of storing data in FileMaker Pro is sharing your data with others. You can share your data
with other FileMaker
Pro or FileMaker Go users on a network and import or export data from
another file. In addition, you can use ODBC (Open Database Connectivity) and JDBC (Java
Database Connectivity) to share FileMaker
Pro files with ODBC- and JDBC-compliant
applications, or you can access data from external data sources. If you have FileMaker
Server,
you can use FileMaker
WebDirect to publish solutions hosted by FileMaker Server to share data
over the web.
If your computer is connected to a network, you and other FileMaker Pro or FileMaker Go users
can use the same FileMaker
Pro file simultaneously. FileMaker Pro Network sharing supports the
sharing of files with up to 5 concurrent users.
Note To support more users and web publishing technologies such as XML, PHP, and
FileMaker
WebDirect, you must use FileMaker Server.
You can set up a FileMaker Pro file to automatically update data imported from another
application, such as Microsoft Excel. When you open a FileMaker
Pro file, this recurring import
occurs automatically the first time you view the layout containing the data from the external file.
As you continue to work in the file, you can run a script to update data on the layout.
For more information about sharing and exchanging data, see chapter 5, “Sharing data.”
Saving and sending data in other formats
FileMaker Pro lets you save data in different file formats, such as Microsoft Excel worksheets and
PDF files, so you can give the files to users who do not have FileMaker
Pro. You can automatically
email the files after saving them. For more information, see
“Saving and sending data in other
formats” on page 109.
Chapter 2
Using FileMaker Pro
This chapter explains the basics of how to:
1 open, close, and save files
1 create records in a file
1 add and edit data in fields
1 find records using different criteria
1 omit records from the found set
1 find and replace data
1 sort data
1 print data, scripts, table and field information, and the relationships graph
1 use scripts
See Help for detailed, comprehensive information and step-by-step procedures about using
FileMaker
Pro.
Note Some procedures refer to using a shortcut menu. To display a shortcut menu (context
menu), right-click or Control-click an object or area to see a list of commands.
About fields and records
A FileMaker Pro solution is made up of one or more database files. Unlike an electronic
spreadsheet, which is used to tabulate and calculate data stored in the cells of a rectangular table,
a database file ties together the information (data) by a schema that describes the organization of
database tables, their fields, and the relationships between the fields and tables. With
FileMaker
Pro, you can organize, update, sort, search through, calculate, and print the data in the
fields and tables as needed.
While spreadsheets are best used for tasks such as maintaining a business ledger, where data
needs to be recorded and calculated, databases are best for tasks such as inventory control,
where you need to track consumption and losses and generate reports on inventory status over
time. An inventory database can sort and report on inventory information in many ways, allowing
you to analyze data by item type, by sales figures, by monthly consumption, and so on.
Your own address book or filing cabinet is an example of a simple database. With the address
book and filing cabinet, you store similar pieces of information organized for easy retrieval. With
a filing cabinet, you must choose a way to sort your data, for example, alphabetically by last name
or by region. By storing contacts and addresses in FileMaker
Pro, you can organize your
information in many ways. You can sort your information by country, city, last name, or even sort
by all three of these fields.

Chapter 2 | Using FileMaker Pro 14
An invoicing system is an example of a more complex database, with multiple related tables,
multiple layouts, and calculated fields.
You can also view a subset of your data; for example, view only invoices for a particular month. A
database doesn’t just hold information—you use a database to organize and analyze information
so that you understand its significance.
Fields are the basis of a database table. Fields are used to store, calculate, and display the data
you enter into a record. Each piece of information in a record—like name, ID number, and
telephone number—is stored in a field.
A database table contains one or more fields that hold similar information about one subject or
activity. For example, the fields on a record in the Customers table contain address information for
one customer. Tables also define the organization of records based on that table.
A database can consist of one file with one table, which might hold the names, addresses, and
telephone and fax numbers of all your customers. A database can also consist of several files,
each of which can contain one or more tables that, together, contain all the information about
related topics (sometimes called a database system). Using the relational capabilities of
FileMaker
Pro, you can join information between files and tables to create a relational database.
For example, one table can show you which customers bought a particular item and a related table
can show how much they paid.
BC
Michelle Cannon
123 4th St. SW
Edmonton
(717) 555-0011
CAN
N4V 1LN
Records
Fields
Your address book is like a database
Invoices table
002
Customer ID
Andre Common
Customer Name
818-555-1234
Phone
Product ID
Product
FB3
Price
Baguette $3.95
FB14 Croissants $9.95
12345
Invoice ID
FB3Product ID
BaguetteProduct
$3.95Price
002Customer ID
Andre CommonName
818-555-1234Phone
Products table
Customers table
34Stock

Chapter 2 | Using FileMaker Pro 15
To enter data in a database table, you make a new record and enter values into the fields that
belong to that record. Values can be typed into a field, imported from another application, or
entered in many other ways.
FileMaker Pro also allows you to access and view data that is stored in non-FileMaker Pro files.
For example, if you have access to data stored in an SQL database, you can display information
from the external database and work with that data in your FileMaker
Pro file.
Opening and closing files
To open a file if FileMaker Pro isn’t running
Choose one of the following methods:
1 Double-click the FileMaker Pro file.
1 Drag the file to the FileMaker Pro application icon.
1 Double-click the FileMaker Pro application icon and choose the file to open.
To open a file located on your computer if FileMaker Pro is already running
1. Choose File menu > Open.
Or, choose File menu > Open Recent or File menu > Open Favorite.
The Launch Center window opens. The My Solutions tab displays any files you’ve marked as
favorites and those you’ve opened recently.
2. If you don’t see the file you want, do any of the following.
Note You can also double-click a file, or select multiple files and click Open. If the file was
created using a version of FileMaker
Pro earlier than 12, see Help.
3. If you’re asked to enter an account name and password when the file opens, type them in the
Open <filename> dialog box, then click OK.
To Do this
Open a file marked as a favorite Select a file under Favorites, then click Open.
Open a file that was recently
opened
Select a file under Recent, then click Open. If Recent is not displayed, click
in the Launch Center window toolbar.
If no recent files are displayed, choose Edit menu (Windows) or
FileMaker
Pro menu (OS X) > Preferences, select Show recently opened
files, enter a value, then click OK. (To remove the display of recent files,
choose File menu
> Open Recent > Clear Recent Files.)
Open a local file that is not
displayed in the Launch Center
window
Click Browse. In the Open File dialog box, choose the location, select the
filename, then click Open.
Switch between displaying only
favorite files and displaying all
files
Click in the Launch Center window toolbar.
View files in a list or as tiles To view in a list, click . To view as tiles, click .
Search for a file Type a few letters of the filename in the search box.

Chapter 2 | Using FileMaker Pro 16
To open a file that is being shared over a network
1. Choose File menu > Open Remote.
The Launch Center window opens to the Hosts tab. If hosts aren’t displayed, click .
Favorite hosts appear first in the list.
2. To see the files available from a host, click the host name.
To view files in a list, click . To view files as tiles, click .
To add or edit hosts, see Help.
3. Select the file you want to open, then click Open (or double-click the filename).
Note Alternatively, you can open remote files using the IP address of the host machine or the
host machine’s DNS name, if one has been defined.
To close a file or window
1 Choose File menu > Close.
Opening multiple windows per file
You can open more than one window per file. This allows you to view the same layout in separate
windows, or simultaneously view different layouts in the same file. You can perform find or sort
operations independently in the different windows.
To open an additional window, choose Window menu > New Window. The new window initially
displays the same layout, sort order, and found set as the previously active window.

Chapter 2 | Using FileMaker Pro 17
To view a different layout in the new window, choose a layout from the Layout pop-up menu in the
layout bar, or choose View menu
> Go to Layout. For information on finding records, see “Finding
records” on page 28. For information on sorting records, see “Sorting records” on page 32.
Saving files
By default, FileMaker Pro automatically saves changes to your data as you work, so there is no
Save command. For more control over when record data is saved, you can clear the Save record
changes automatically option (in the Layout Setup dialog box) individually for each layout.
To save a copy of your file (for example, as a backup) or save a clone of your file with no data, see
Help. To save a copy of your file in a non-FileMaker format, see
“Saving and sending data in other
formats” on page 109.
FileMaker Pro doesn't save changes to the state of a file if they are the only changes you make
while the file is open.
The original window, in
Browse mode, in which
you can view the records
A second window, in
Find mode, in which you
can perform a different
search on the same
found set
Layout pop-up menu

Chapter 2 | Using FileMaker Pro 18
About modes
You work with data in FileMaker Pro in Browse, Find, Layout, or Preview mode. You can choose a
mode from the View menu or from the mode pop-up menu at the bottom of the document window.
Using the status toolbar
The status toolbar provides quick access to many FileMaker Pro menu commands. In all modes,
it includes navigation tools, customizable buttons, and a layout bar for working with layouts. In
Layout mode, the status toolbar includes layout tools. Move the pointer over a button to see its
description. You can also switch modes by clicking buttons in the status toolbar. The buttons in the
status toolbar vary depending on which mode you’re in.
In Layout mode, you can also use the Inspector when you format and edit objects on a layout. For
more information, see
“Using the Inspector to format objects” on page 68.
Use this mode To
Browse mode Work with the data in a file. You can add, view, change, sort, omit (hide), and delete records.
Browse mode is where you’ll do most of your work, such as data entry.
Find mode Search for particular records that match a set of criteria. You can then work with this subset
of your records, called the found set. After you find a group of records, FileMaker
Pro returns
to Browse mode so you can begin working with them.
Layout mode Determine how information is presented on your screen or in printed reports, labels, and
forms. Design layouts for specific tasks, like data entry or printing invoices or envelopes.
Select and arrange fields and other objects to modify an existing layout or create new layouts.
Preview mode See how data in forms or reports will look before you print. Preview mode is especially useful
for viewing layouts with multiple columns (like mailing labels) and reports with
summaries.
Mode pop-up menu
Status
toolbar
Layout bar
Formatting bar
Status toolbar in Browse mode (Windows)
Status
toolbar
Layout bar
Formatting bar
Status toolbar in Browse mode (OS X)

Chapter 2 | Using FileMaker Pro 19
Viewing records
FileMaker Pro provides three views of each layout: form, list, and table. When you change views,
you temporarily change the way records display or print.
To view records Do this in Browse mode or Find mode
Individually Choose View menu > View as Form, or click Form View in the layout bar.
In a list Choose View menu > View as List, or click List View in the layout bar.
In a spreadsheet-like table Choose View menu > View as Table, or click Table View in the layout bar.
Each row displays a record, and each column displays a field.
For information about working with data in a spreadsheet-like table, see “Working
with data in Table View” on page 26.

Chapter 2 | Using FileMaker Pro 20
The following illustration shows the same layout in three views.
Form View
List View
Table View
Current record
A row is one record
Field labels
Field labels
Field labels
Current record
Current record

Chapter 2 | Using FileMaker Pro 21
Selecting the current record
In Browse mode, a table has one current (active or selected) record at a time for each window. For
more information about moving through records, see
“Moving through records” on page 21.
To select a related record in a portal, select the portal row (click inside the row but outside any
fields in the row).
For information about related records and portals, see chapter 4, “Working with related
tables and files.”
Moving through records
To move from one record to another, use the forward and backward buttons in the status toolbar.
In this view The current record is
Form View The record that you’re displaying. To select another record and make it the current record,
move to the other record.
List View The record that has a different fill from the other records. To select another record and
make it the current record, click that record or use controls in the status toolbar.
The current record can also be indicated by a solid vertical bar along the left side.
Table View The record that’s highlighted in the record margin at the left of the record. To select
another record and make it the current record, click that record or use controls in the
status toolbar.
Click inside the portal row to
select a related record
Portal
Slider
Records in the table
Move backward
and forward
Type search words
for quick finds
Records in the found set
Current record
number

Chapter 2 | Using FileMaker Pro 22
Note If your device supports gestures, you can use gestures to move through records, zoom in
and out, scroll inside portals and web viewers, and move through slide panels. See Help.
Adding and duplicating records
When you add or duplicate records, FileMaker Pro stores new records at the end of the current
table. In Browse mode, you see the new record after the current record, or after the last record in
the found set (the set of records made active by a find request).
1 If records are sorted, by default the new record appears in the correct position in the sort order
when you commit the record.
1 If records are unsorted, the new record appears after the last record in the found set. For more
information, see
“Sorting records” on page 32.
Note If a file is locked or write-protected, or if you don’t have access privileges to create records,
FileMaker
Pro will not add or duplicate records.
If the field is defined to automatically enter field values, you see those values entered in the new
record. See
“Setting options for fields” on page 50.
To enter or change values in the new record, see “Entering and changing data in fields” on page 25.
To move Do this
To the next record in the current
table
Click or choose Records menu > Go to Record > Next.
To the previous record in the
current table
Click or choose Records menu > Go to Record > Previous.
Quickly to a specific record 1 Click the current record number, type the record number, then press Enter (or
Return.
1 With the current record selected, press Esc, type the record number, then
press Enter or Return.
1 Choose Records menu > Go to Record > Go To, then type the number of
the record.
Quickly through records Drag the slider right or left to move forward or backward.
Through records in List View or
Table View
Use the scroll bar on the right side of the window.
To a record with a unique value
that you know
See “Finding records” on page 28.
To Do this in Browse mode
Add a new blank record Click New Record in the status toolbar. You see a blank record with one
field selected.
Quickly add a record with the same or
similar data as an existing record
Select the record to duplicate. Then, choose Records menu > Duplicate
Record.
Add or duplicate related records See “Adding and duplicating related records” on page 23.

Chapter 2 | Using FileMaker Pro 23
Adding and duplicating related records
If you’re working with records in related tables, you can add records to a related table when you
enter data in a record in the current table.
Note You can only add related records from the current table if the relationship is defined to allow
the creation of related records. If a related table is in a write-protected file, or if you don’t have
access privileges to create records, FileMaker
Pro will not add or duplicate records. See “Creating
relationships” on page 94.
To Do this in Browse mode
Create a record in the current
table
Click New Record in the status toolbar.
Add a record to a related table 1 If the related field is in a portal, type data into the field in the last (empty) row
of the portal, then commit the record (for example, by clicking anywhere
outside the record or selecting another record).
1 If the related field isn’t in a portal, type data into the field, then commit the
record (for example, by clicking anywhere outside the record or selecting
another record).
Duplicate a record that is
displaying related data
Be sure no records in a portal are selected, then choose Records menu >
Duplicate Record.
Note Records in related tables are not duplicated.
Duplicate a related record in a
portal
Select the record in the portal, then choose Records menu > Duplicate
Record.
Portal with related
records from the Line
Items table
Type in the last row of
the portal to add a
related record to the
Line Items table

Chapter 2 | Using FileMaker Pro 24
Deleting records
When you delete a record, you permanently discard the data in all the fields in that record.
Important You can’t retrieve deleted data, and you can’t undo the action of deleting records.
Before you delete records, consider making a backup copy of your file.
If you’re working in a relational database and the option to delete related records is selected in the
Edit Relationship dialog box, FileMaker
Pro deletes related records when you delete a record.
Entering data
Note If a file is locked or write-protected, or if you don’t have privileges to edit certain records or
fields, you may not be able to modify data.
Selecting a field
To delete Do this in Browse mode
One record Select the record to delete. In the status toolbar, click Delete Record, then click Delete.
A related record Select a portal row in the current table by clicking inside the row but outside any fields in
the row. In the status toolbar, click Delete
Record, then click Delete.
Note To delete related records, Allow deletion of portal records must be selected in
the Portal Setup dialog box.
A group of records Make sure the found set contains only the records you want to delete. (See “Finding records”
on page 28.) Choose Records menu > Delete Found Records, then click Delete All.
All records in a table Click Show All in the status toolbar, or choose Records menu > Show All Records.
Choose Records menu > Delete All Records, then click Delete All.
All records in a file Create a clone of the file with no records. See “Saving files” on page 17.
To Do this in Browse or Find mode
Select a field Click in the field.
Select the contents of a field Select the field, then choose Edit menu > Select All.
Move to the next field in the tab
order
Press Tab.
Note To set the Return or Enter key(s) to move to the next field, in Layout mode,
select the fields. Click Inspector in the layout bar, then click Data. In the
Behavior area, for Go to next object using, select the keys to use for exiting
fields.
Buttons, popover buttons, tab controls, and slide controls can be included in the
tab order. Fields on tab panels or slide panels that are not on the front-most panel
are skipped.
Move to the previous field in the
tab order
Press Shift-Tab (or Shift-Return or Shift-Enter, if enabled).
Move to items in a value list Press the arrow keys.

Chapter 2 | Using FileMaker Pro 25
Entering and changing data in fields
You can enter or import data up to the character limit for the field type. You can view and print only
the data that fits within the field boundaries.
Note For information about how FileMaker Pro uses system formats to display and sort dates,
times, and numbers, see Help.
To Click in the field in Browse mode, then
Enter data in a text field Type the text.
Note In a field set up to auto-complete, you see suggestions based on what you
type.
Enter data in a number field Type the values (from 10
400
to 10
-400
).
Enter data in a date field Type one date on one line in the field. Type the day, month, and year as numbers
(for example, 3/3/2014), separated by a nonnumeric character like – (minus) or /
(forward slash).
Note You cannot use a : (colon) as a date separator.
Important If you enter dates with two-digit years, FileMaker Pro converts them
to four-digit year dates using a conversion method described in Help. To avoid
misinterpretations during conversion, always enter dates with four-digit years.
Enter the current date in a date,
number, or text field
Choose Insert menu > Current Date.
Select the date using the drop-down calendar, if available.
Enter data in a time field Type the time of day (or time duration) as:
1 hours
1 hours and minutes
1 hours, minutes, and seconds
1 hours, minutes, seconds, and fractional seconds
Separate hours, minutes, and seconds by a nonnumeric character like : (colon).
Separate fractional seconds by a . (period).
Type the time of day in 24- or 12-hour format, with or without AM or PM. (AM is
assumed for a time less than 12:00.)
Enter the current time in a time,
number, or text field
Choose Insert menu > Current Time.
Enter data in a timestamp field Type the date and time (for example, 10/10/2014 3:15:05 PM). Type the day,
month, and four-digit year as numbers, separated by a nonnumeric character like
– (minus) or / (forward slash).
Note You cannot use a : (colon) as a date separator.
Then type the time of day as:
1 hours and minutes
1 hours, minutes, and seconds
1 hours, minutes, seconds, and fractional seconds
1 Type AM or PM if the time is not in 24-hour format
Separate hours, minutes, and seconds by a nonnumeric character like : (colon).
Enter the current date and time
in a timestamp field
Choose Insert menu > Current Time.
Select the date using the drop-down calendar, if available.
Insert a tab character in a field Click where to insert the tab. Press Ctrl+Tab (Windows) or Option-Tab (OS X).
Delete data from a field Select the data, then press Backspace or Delete.
Insert an audio, video, image,
PDF, or other type of file in a
container field
See Help.

Chapter 2 | Using FileMaker Pro 26
Working with data in Table View
You can work with data in Table View to quickly create and change field definitions; add, modify,
and delete records; sort records; create dynamic reports; and create quick charts. FileMaker
Pro
displays each record in a separate row, and each field in a separate column.
To work with data in Table View, click Table View in the layout bar when you’re working in
Browse mode.
Displaying data in Table View
You can change the display settings in Table View.
Add data to value lists (fields
formatted as radio or option
buttons, checkboxes, lists, or
menus)
For information, see “Setting up fields to display checkbox sets and other controls
on a layout” on page 74.
Edit, format, or check the
spelling of text in a field or edit
dictionaries
See Help.
To Click in the field in Browse mode, then
To Do this
Reorder columns Click a column heading and drag it to a new location.
Resize a column Move the pointer to the edge of the column heading. When the pointer changes to a
double arrow (
), drag it to the desired size.
Set a precise column width Select one or more columns, then right-click and choose Table View > Set Column
Width from the shortcut menu. In the dialog box, type a width, choose units from the
list, then click OK.
Change the color of the
background
Right-click the left or right margin of a record, choose Part Color from the shortcut
menu, then choose a color. The color of the row for adding new records and the
column for adding new fields will be slightly darker than the main background color.
Display a different
background color for
alternating records
Right-click the left or right margin of a record, then choose a color from the Alternate
Color shortcut menu.
Restore the default display
settings
Right-click a column heading and choose Table View > Reset from the shortcut menu.
Note Resetting Table View doesn’t delete the fields and records.
Column headings:
each column displays
one field from the
current layout
Active
record
Record margin

Chapter 2 | Using FileMaker Pro 27
Working with records in Table View
When you view records in a table, FileMaker Pro displays data in rows and columns. Each row
displays a record, and each column displays a field.
Note You can set field options such as validation or indexing when you define a field, or at a later
time. See
“Setting options for fields” on page 50.
To Do this in Browse mode
Add a new record Click + in the left margin at the bottom of the table. A new row is added to
the end of the table if the records have not been sorted or if Keep records
in sorted order is cleared in the Sort Records dialog box.
Enter data in fields Click in the field, then enter data in the field. See “Entering and changing
data in fields” on page 25.
Note FileMaker Pro saves changes to your data as you work. To see how
your data looks in other views, click Form View or List View in the
layout bar.
Duplicate a record Right-click the left or right margin of the record to duplicate, then choose
Duplicate Record from the shortcut menu.
Delete a record Right-click the left or right margin of the record to delete, then choose
Delete Record from the shortcut menu.
Copy the data in a record Right-click the left or right margin of the record to copy, then choose Copy
Record from the shortcut menu. You can paste the copied, tab-separated
data into a field or into Microsoft Excel.
Sort records by one or more fields Select a column heading and optionally Shift-click additional headings.
Right-click one of the selected column headings and choose Sort
Ascending or Sort Descending. A sort icon appears on the column
headings indicating the sort setting (ascending or descending). If you
selected multiple columns, the order in which columns were selected
determines the sort order.
You can also choose Sort By Value List and then select a value list from
the submenu.
For more information, see “Sorting records” on page 32.
Create a dynamic report See Help. For example, you can create a quick report to group your data
by a field, display subtotals for a field, or create subtotals for each group of
data.
Create a quick chart See Help. For example, you can quickly create a chart from Table View
based on the data in the current field.
Save data as a Microsoft Excel file or
Adobe PDF file, or save the current
found set of records as a snapshot link
Right-click the left or right margin, then choose an option from the
Save/Send Records As shortcut menu.
Send email messages based on
record data
Right-click the left or right margin of the record, then choose Send Mail
from the shortcut menu.

Chapter 2 | Using FileMaker Pro 28
Finding records
To find particular records in your file, you can:
1 perform a quick find in Browse mode
1 make a find request in Find mode
Performing quick finds in Browse mode
If a layout is enabled for quick find in Browse mode, you can use the search box in Browse mode
to search for data across multiple fields on the layout. Quick find is helpful if the data you are
looking for might be in multiple fields or if you don’t know which field contains the data.
When a layout is enabled for quick find, all fields that are supported for quick find (including merge
fields) are set to be included in the search. Quick find does not search summary, container, or
global fields. (To enable a layout for quick find, see
“To configure and enable quick find” on
page 29.)
Note While quick finds are an easy way to search for data, they can work slowly depending on
the type of data in the file. For example, unstored calculations or related or remote data can slow
progress, compared with data that's local or stored.
To perform a quick find
1. In Browse mode, type one or more words in the search box in the upper-right corner of the
status toolbar.
2. Press Enter or Return.
The search includes all the fields that are enabled for quick find on the layout. Your find request
returns a found set of records. The highlighted area of the pie chart
in the status toolbar
indicates the portion of the total records displayed.
Keep the following points in mind:
1 The only find operator supported by quick find is the match phrase operator, which is double
quotation marks ("
").
1 If you type more than one word in the search box, FileMaker Pro searches for records that have
all of the words you typed.
To view a list of recent quick finds
1. In Browse mode, click the down arrow in the search box.
2. Do one of the following:
1 Choose a search term from the search history list to perform a quick find for the term.
1 Choose Clear Recent Searches to remove the search history.
Note The list of recent quick finds is available only until you close the file.

Chapter 2 | Using FileMaker Pro 29
To configure and enable quick find
If the selected layout doesn’t show the quick find badges for supported fields in Layout mode, use
the following steps.
1. In Layout mode, choose View menu > Show > Quick Find.
A small badge next to each field shows if the field has been enabled for quick find. If there is no
quick find badge next to a field, the field is not searchable, either because it is not supported for
quick find or because it is not set to be included in the search. A gray badge
indicates that
the layout is disabled for quick find. A green badge indicates that the field is searchable. A
yellow badge indicates that the field is searchable, but the search might take longer than
fields with the green badge.
2. Select one or more fields.
3. Click Inspector in the layout bar, then click Data.
4. In the Behavior area, select Include field for Quick Find.
5. To enable quick find, click Layout Setup in the layout bar. In the Layout Setup dialog box,
select Enable Quick Find, then click OK.
Making find requests in Find mode
When you perform a find in Find mode, you type criteria (the value or values to find) into fields in
a find request, which looks like a blank record. FileMaker
Pro searches through all the records in
a table, comparing the criteria you specify with the data in the table.
Records with data matching the criteria become the found set, which is the subset of records being
browsed. Records that don’t match are omitted. You can constrain (narrow) or extend (broaden)
the found set in Find mode.
You can work with just the records in the found set. For example, you can view, edit, calculate
summaries for, sort, print, delete, export, or replace data in these records. You can also open a
new window in order to perform different find requests on the same data.
You can save the found set of records and email it as a snapshot link.
You cannot perform a find in summary fields, container fields, or fields defined with the global
storage option.
Note In Find mode, a badge indicates a searchable field.

Chapter 2 | Using FileMaker Pro 30
To make a find request
1. In Find mode, from the Layout pop-up menu, select a layout that includes the fields that contain
the data to search.
If necessary, you can change layouts and enter criteria on more than one layout.
2. In the find request, select a text, number, date, time, timestamp, or calculation field to use for
finding, and then type a value in the field.
You can use the Insert Operators list in the layout bar to help you enter criteria. You can click
Omit to exclude records matching a specific set of criteria.
3. Click Perform Find.
Your find request returns a found set of records. The highlighted area of the pie chart in the
status toolbar indicates the portion of the total records displayed.
Choose a layout
with fields to
search on
Type find criteria in fields
Click to see
operators
A badge indicates you
can search on the field

Chapter 2 | Using FileMaker Pro 31
You can do the following during or after performing a find request:
Finding data in related fields
You can enter find criteria in related fields that are displayed in a portal or directly on a layout.
When you perform a find in a related field, FileMaker Pro displays all the records that have a
related record matching the criteria you enter. For example, you have an invoice file that displays
line items as related records in a portal. To find all invoices listing a computer, type Computer in
the Item field in the portal. For information about related fields, see
chapter 4, “Working with
related tables and files.”
Viewing, repeating, or changing the last find
To view the most recent find criteria, choose Records menu > Modify Last Find. Then, to return
to the found set, switch to Browse mode. To repeat the find, click Find. Or you can modify the find
criteria, then click Perform Find.
To Do this
Cancel a find operation before it is finished and
leave the previous found set unchanged
Press Esc (Windows) or 2-period (OS X).
Show all records again In Browse mode, choose Records menu > Show All Records.
In Find mode, choose Requests menu > Show All Records.
You don’t need to choose Show All Records before performing
finds. FileMaker Pro always searches all records in the tables you
specify unless you have narrowed the existing found set.
Omit (hide) one or more found records See “Hiding records from a found set and viewing hidden records”
on page 32.
Open another window in order to perform
different find requests on the same data
Choose Window menu > New Window.
E154Invoice ID
AlvarezName
Item ID Item
I100
Computer
I202 Desk
I153 Lamp
I229 Bookcase
I448 Chair
Find request
E153Invoice ID
TangName
Item ID Item
I202
Desk
I443 Long table
I153 Lamp
I288 Round table
I100 Computer
Invoice ID
Name
Item ID Item
Computer
E152Invoice ID
DurandName
Item ID Item
I384
Swivel chair
I554 Panels
I288 Round table
I100 Computer
I448 Chair
Records in table

Chapter 2 | Using FileMaker Pro 32
Saving find requests
When you have a complex find request that you want to use regularly, you can save the request
and retrieve it when you need it later. You can save and retrieve find requests without having to
go to Find mode. FileMaker
Pro automatically saves the last five finds you have performed so you
can access them again. Once a find is saved, the saved find is also available to any network clients
that share the account.
Deleting and reverting requests
To delete a request, go to the request, then click Delete Request.
To restore a request to the way it was when you last committed it, choose Requests menu >
Revert Request. Requests are committed, for example, when you click out of all fields, go to a
different layout or request, or perform a find.
Hiding records from a found set and viewing hidden records
All records that are not in the found set are omitted, or hidden. You can omit additional records
from the found set without doing a new find.
Important Omitted records are temporarily excluded from the found set. They still exist in the file.
Finding and replacing data
As in a word processing application, you can find and replace data across multiple fields (including
related fields) in a record or in a find request, across a found set of records or find requests, or
across text objects in a layout. You can search for data in any type of field except container fields
and fields that are not modifiable.
To find and replace data, in Browse, Find, or Layout mode, choose Edit menu > Find/Replace >
Find/Replace.
Sorting records
FileMaker Pro stores records in the order they were added to the file. Sorting temporarily
rearranges records, so you can view, update, or print them in a different sequence.
You choose the fields whose contents you want to sort by. The first sort field arranges the records
based on the field’s contents. The second sort field arranges records when two or more records
have the same value in the first sort field, and so on. You can sort records in ascending order,
descending order, or in a custom order.
By default, the records remain sorted until you perform a find or sort records by different criteria.
When you add or change a record in a sorted found set, the record appears in the correct position
in the sort order after you commit the record.
To Do this
Omit a specific record Display or select the record to omit, then choose Records menu > Omit.
Omit a series of records Display or select the first record in a number of consecutive records to omit, then
choose Records menu > Omit Multiple. In the Omit Multiple dialog box, type the
number of records to omit, then click Omit.
View the omitted set Choose Records menu > Show Omitted Only.
Bring back all the records in
the file
Choose Records menu (Browse mode) or Requests menu (Find mode) > Show
All Records.
Chapter 2 | Using FileMaker Pro 33
To sort the records in the current found set:
1. In Browse mode, click Sort in the status toolbar.
Note To sort records in Table View in Browse mode, see “Working with records in Table View”
on page 27.
2. In the Sort Records dialog box, choose fields for sorting, in the order you want them sorted, and
sort options.
To choose a sort field visible on the current layout, no matter what table it is in, choose Current
Layout (LayoutName) from the table list, then double-click a field in the list.
To choose a sort field that is in the current layout’s table, whether or not it is on the current layout,
choose Current Table (TableName) from the table list, then double-click a field in the list.
3. Click Sort.
To cancel before sorting is finished, press Esc (Windows) or 2-period (OS X).
Note You can sort records on one field without opening the Sort dialog box by using the field’s
shortcut menu.
Previewing and printing files
With FileMaker Pro, you can print:
1 all the records in the file, a subset of the records, or only the current record
1 a blank record to create a paper form
1 definitions of scripts, fields, tables, and relationships to see the structure of your database
1 data saved as a PDF file
FileMaker Pro prints records using the current layout. You can create layouts to print the same
data in different ways. For example, print records one by one, in a columnar list, or in a complex
sorted report with totals, headers, and footers. You can control page margins, remove blank
space, and keep specified objects from printing.

Chapter 2 | Using FileMaker Pro 34
Previewing data on a layout
When you switch to Preview mode, you see the layout as it appears on the printed page. You can’t
enter or edit information in fields in Preview mode.
In Preview mode, you see:
1 how many records fit on a printed page
1 how the pagination settings you choose affect page breaks
1 subsummary parts with calculated summary fields
1 variable information supplied by FileMaker Pro, like page numbers, the current date, and so on
1 the page margins you define
1 how fields set with sliding options close up blank space
1 records arranged in columns if the Layout Setup dialog box is defined to print in columns
1 the front-most tab panel or slide panel if the page contains panel controls
1 popover buttons, but not their associated popovers or the contents of popovers
To preview data on a layout, you follow the same preliminary steps that you perform when you
print, including specifying a printer and printing options and verifying that the found set contains
the records you want to preview (see steps 1 through 4 in the next section,
“Printing records”).
Then, switch to Preview mode.
Print Phone List
Go to Layout [Contacts]
Sort [Sort Order: Last name (Ascending) ]
[Restore sort order, No Dialog]
Enter Preview Mode
[Pause]
Print
[no dialog]
Enter Browse Mode
Name Phone
Juanita Alvarez 408-555-1234
Michelle Cannon 213-555-2345
Andre Common 714-555-3456
Marie Durand 619-555-4567
Jean Durand 408-555-5678
William Johnson 408-555-6789
Contacts
Records being browsed
Field Name Field Type
Formula/Entry Options
First Name Text
Last Name Text
Address1 Text
Name Phone
Juanita Alvarez 408-555-1234
Contacts
Current record
Script
Table and field
definitions
Blank record
You can print data based on the current layout or print information about the
structure of the database
Relationships graph
Name Phone
Contacts

Chapter 2 | Using FileMaker Pro 35
Printing records
You can print information from your file, or you can print a blank record in order to print a blank
“form.”
1. Specify printer and confirm printing options by choosing File menu > Print Setup (Windows) or
File menu
> Page Setup (OS X), then click OK.
In Preview mode, you can also click Print Setup (Windows) or Page Setup (OS X) in the status
toolbar.
For information about printer options, refer to your printer and system documentation.
2. Switch to the layout to use.
3. Make sure the found set is the way you want it, by:
1 using Find mode and commands on the Records menu to change the found set
1 sorting the records
4. Switch to Preview mode to see how your paper copy will look.
If a record contains tab controls or slide controls, only the front-most panel is printed.
5. Choose File menu > Print.
6. In the Print dialog box:
1 Windows: For Print, choose an option.
1 OS X: Choose FileMaker Pro from the list. For Print, choose an option. If you don’t see the
options, click Show Details.
Note To print a blank “form” of the layout, choose Blank record, showing fields.
7. Select the print range, number of copies and other printing settings, then click OK (Windows)
or Print (OS
X).
Printing table and field information
1. Choose File menu > Manage > Database, then click the Tables or Fields tab.
2. Select the table(s) or field(s).
3. Click Print.
4. Click OK (Windows) or Print (OS X).
Printing the relationships graph
1. Choose File menu > Manage > Database, then click the Relationships tab.
2. Click to display page breaks in the relationships graph.
3. Click to display the Print Setup (Windows) or Page Setup (OS X) dialog box.
4. Change or accept the settings, then click OK.
5. Click Print.
Chapter 2 | Using FileMaker Pro 36
6. In the Printing Options dialog box, choose to print on one page or multiple pages, then click
Continue.
7. Click OK (Windows) or Print (OS X).
Backing up files
Routine backups are strongly recommended for any document stored on a computer. It is easier
to restore a backed-up file than it is to re-create it. How often you should back up depends on the
amount of data you are adding to your files, and how difficult it would be to re-create your files if
they become corrupt.
For very important files, it’s a good idea to routinely store backups at an offsite location.
For file backup recommendations, see “Backing up databases and other important files” on
page 122. For an example of a backup script, see Help.
Setting preferences
You can customize the appearance and behavior of FileMaker Pro to suit the way you work by
changing standard settings called preferences. Preferences affect the behavior of the application
and are not specific to any file.
To set application preferences:
1. Windows: Choose Edit menu > Preferences.
OS X: Choose FileMaker Pro menu > Preferences.
2. In the Preferences dialog box, click a tab, then set options.
You can also set preferences that affect an individual file’s default login information, layout,
representative icon, spell checking, text handling, and scripts for opening and closing the file.
To set file preferences for the current file:
1. Choose File menu > File Options.
2. In the File Options dialog box, click a tab, then set options.
Chapter 3
Designing and creating solutions
This chapter explains the basics of how to:
1 plan a FileMaker Pro solution
1 define and modify fields
1 define tables
1 create layouts
1 work with fields, objects, and parts on a layout
Note See Help for detailed, comprehensive information and step-by-step procedures about
using FileMaker
Pro.
Planning a solution
The first step in creating a solution is to plan the content, structure, and design. Then, you create
a FileMaker
Pro database file and define tables and fields.
A well-designed solution promotes consistent data entry and retrieval, and reduces the existence
of duplicate data among the database tables. Relational database tables work together to ensure
that the correct data is available when you need it. It’s a good idea to plan a solution on paper first.
Follow these general steps:
1. Determine the purpose for your solution, or the problem you want to solve. For example, “to
keep a list of my customers,” “to manage my inventory,” “to grade my students,” or “to work with
data on my desktop computer, on my iPad, and in a web browser."
If other people will use the solution, be sure to talk with them about the data they will need.
2. Consider the information you will store in your database. Typically, information falls into broad
categories. Accurately identifying these categories is critical to designing an efficient database,
because you will store different types and amounts of data in each category. For example, a
solution intended to track sales has categories such as “customers,” “products,” and “invoices.”
A database that records student grades has categories such as “students,” “classes,” and
“assignments.”
3. After you’ve determined the broad categories, consider how these categories are related. This
can be done by writing simple sentences that describe how the categories interact, such as,
“customers order products” and “invoices record customers’ orders.” Each of these pairs
suggests a relationship between the data in one category and the data in the other category.
Chapter 3 | Designing and creating solutions 38
4. After you’ve identified your categories of information, you are ready to organize your database.
In database terminology, these categories of information are referred to as tables. Tables are
used to group data containing a common element or purpose. For example, you might use one
table to store names and addresses, while you use another table to store transaction details,
such as date of sale, item number, unit price, and so on.
Typically, databases are organized in one of three ways:
1 A single table in a single file. Use a single table if you need to track data in one category only,
such as names and addresses.
1 Multiple tables in a single file. Use multiple tables if your data is more complex, such as
students, classes, and grades.
1 Multiple tables in multiple files. Use multiple files if you need to share the same data among
several different database solutions. For example, you can store your tax rates or shipping
information in a separate file if you plan to use that information in more than one solution.
Note Use relationships to share data between tables in the same file or with tables in external
files. Other database elements, such as scripts and access privileges, are stored at the file
level; therefore, some complex solutions will benefit from using multiple files.
5. Determine the database tables and the data they will include, and, in turn, which fields you will need.
Tip To make it easy to search and sort records, create separate fields for first and last name,
titles (like Mr. or Dr.), and items in addresses (city, state or province, country, and postal code).
Separating your data into multiple fields at the time of data entry can make it easier to generate
future reports. For example, using separate fields to capture transaction details such as the
date, item number, quantity, and unit price of each transaction makes it easier to compile
summary and subsummary reports at the end of a week, month, or year.
6. Decide which fields will contain common data among the tables.
For example, a database for a bakery business might include these tables: a Customers table,
which stores customer information; a Products table, which stores product information; and an
Invoices table, which stores order information.
Each table has only one subject, and all fields in a table describe only that subject. For example,
the fields in one record of the Customers table together store all the information about one
customer. For the same reason, you might assign each customer a unique, identifying number.
You wouldn’t enter a customer identification number into the table unless you had a new
customer to add, so the existence of a customer number determines the existence of a record.
A Customers table might also have fields for the customer’s name, address, and phone
number.

Chapter 3 | Designing and creating solutions 39
A Products table might have fields for a product identification number, the unit price for each
product, and the quantity in stock. A Line Items table might have fields for product and invoice
identification numbers, the name, unit price, quantity, and total price of each product sold. An
Invoices table might have fields for an invoice identification number, order date, and salesperson.
7. Determine the match fields for each table, and circle each one in your plan.
For more information, see “About match fields for relationships” on page 88.
Customer ID
Address
Phone
Customer Name
Country
Salesperson
Customers table
Products table
Line Items table
Order Date
Customer ID
Order Date
Invoice ID
Invoice ID
Unit Price
Product ID
Qty
Subtotal
Discount
Extended Price
Product Name
Total
Total in Stock
Order Date
Product ID
Unit Price
Product Name
Stock
Category
Invoices table
Region
Region
Salesperson
Discount
Total in Stock
Customer ID
Address
Phone
Customer Name
Country
Salesperson
Customers table
Products table
Line Items table
Order Date
Customer ID
Order Date
Invoice ID
Invoice ID
Unit Price
Product ID
Qty
Subtotal
Discount
Extended Price
Product Name
Total
Total in Stock
Order Date
Product ID
Unit Price
Product Name
Stock
Category
Invoices table
Region
Region
Salesperson
Discount
Total in Stock

Chapter 3 | Designing and creating solutions 40
8. For each table, decide which fields will store data and which ones will be used from other
(related) tables.
Based on a table’s subject, you can see where it makes sense to store the data and where to
use data from a related table. Other than match fields, all fields should appear only once in your
database. Cross out occurrences of fields that don’t pertain to the table’s subject.
9. Determine the relationships between the tables. In your plan, draw a line from each match field
in a table to the corresponding match field in the related table.
What establishes a relationship between tables is that their match fields contain matching data.
Relationships also make it possible to group your data to resolve complex queries. For
example, relationships can be used to determine current inventory levels, sales projections,
and other tasks where it is necessary to query data across multiple tables. For more information
about relationships, see
chapter 4, “Working with related tables and files.”
10. Determine whether you need to share your database with other users and how they will access
the file.
For more information about sharing databases, see “Sharing databases on a network” on
page 98.
11. If you’re designing the database for other people to use, show them your paper plan and ask
them to review it and suggest any changes.
Customer ID
Address
Phone
Customer Name
Country
Salesperson
Customers table
Products table
Line Items table
Order Date
Customer ID
Order Date
Invoice ID
Invoice ID
Unit Price
Product ID
Qty
Subtotal
Discount
Extended Price
Product Name
Total
Total in Stock
Order Date
Product ID
Unit Price
Product Name
Stock
Category
Invoices table
Region
Region
Salesperson
Discount
Total in Stock
Customer ID
Address
Phone
Customer Name
Country
Salesperson
Customers table
Products table
Line Items table
Order Date
Customer ID
Order Date
Invoice ID
Invoice ID
Unit Price
Product ID
Qty
Subtotal
Discount
Extended Price
Product Name
Total
Total in Stock
Order Date
Product ID
Unit Price
Product Name
Stock
Category
Invoices table
Region
Region
Salesperson
Discount
Total in Stock

Chapter 3 | Designing and creating solutions 41
12. Consider who will use the database and whether you want to restrict access to it. When you
create the database, assign access privileges as needed.
For more information about accounts and privilege sets, see chapter 6, “Protecting files.”
13. Decide what layouts you need, and plan a separate layout for each task.
For example, create separate layouts for printing labels or envelopes, and for working on an
iOS device (such as iPad or iPhone) or in a web browser.
For more information about creating layouts, see “Creating layouts and reports” on page 54.
14. Create a form, such as the one shown below, to list the files and tables you need and the fields
for each table. Also list the forms and reports you will generate from each table.
15. Create your database.
16. If you’ve designed the database for others to use, ask a few people to test it. Fix any problems
before making it available for general use.
Creating a FileMaker Pro file
You can create a file from a FileMaker Pro Starter Solution—a pre-designed solution file that you
can modify to suit your needs. Or, you can create a file without using a Starter Solution.
You can also create a file by making a copy of an existing FileMaker Pro file. See “Saving files” on
page 17.
Creating a file using a Starter Solution
1. Choose File menu > New from Starter Solution.
Or, in the My Solutions tab of the Launch Center window, click New and choose New from
Starter Solution.
2. Select a solution, then click Choose.
If no solutions are displayed, Starter Solutions may not have been installed.
Sample Solution Design Form
Project name
Purpose of this solution
Filename for this solution
Table name
Field name Field type Comments
Layouts
Table name
Field name Field type Comments
Name Purpose Screen Print iOS Web
Chapter 3 | Designing and creating solutions 42
3. Type a name for the file (choose a different folder, if needed), then click Save.
Windows: For Save as type, select FileMaker Files.
4. Click Save.
FileMaker Pro creates the file on your disk and opens the file.The pre-designed solution
contains fields and buttons set up for tasks that are commonly performed, but it contains no
data. You can modify fields and layouts in Starter Solutions. For more information, see the
remaining sections in this chapter.
5. Click New Record in the status toolbar to add data to the file.
Creating a new file
1. Choose File menu > New Solution.
Or, to create a new file in the Launch Center window, click the My Solutions tab, click New, and
choose New Solution.
2. Type a name for the file (choose a different folder, if needed), then click Save.
Windows: For Save as type, select FileMaker Files. If you don't type a file extension,
FileMaker Pro adds .fmp12 to the filename. (For information about viewing file extensions in
Windows, see Windows Help and Support.)
FileMaker Pro creates the file, displays a blank, empty file in Layout mode, and displays the
Field Picker dialog box, which you use to define fields for the database and add them to the
layout.
To have fields automatically placed on the layout, select Add newly defined fields to current
layout in the Layout tab of the Preferences dialog box before you define the fields.
3. Define the fields, drag them to the layout, then close the Field Picker dialog box.
For details about defining fields using the Field Picker dialog box, see “Creating and changing
fields in the Field Picker dialog box” on page 46.
You can set field options such as validation or indexing when you define a field, or at a later
time. For more information, see
“Setting options for fields” on page 50.
4. Add objects and other embellishments to the layout.
For more information, see “Working with objects on a layout” on page 66.
5. Save the layout by pressing Ctrl+S (Windows) or Command-S (OS X), then exit the layout (click
Exit Layout in the layout bar).
Keep the following points in mind:
1 For information about entering data in fields in Browse mode, see “Adding and duplicating
records” on page 22.
1 To change the layout theme, see “Working with layout themes” on page 60.
1 You can change the width of a layout to accommodate more (or fewer) objects. Making a layout
wider helps you see the edge of the layout without resizing the window. To change the width of
a layout, drag the gray line on the right side of the layout.

Chapter 3 | Designing and creating solutions 43
Creating and changing fields
To define a new field in the database, you give it a name and select a field type. Then you select
options that determine how the field interprets, enters, calculates, stores, and displays data. These
characteristics make up the field definition.
See “Formatting field data on a layout” on page 76 for information about setting options for field
formats, which control how data appears on a layout.
About naming fields
Follow these guidelines when naming fields:
1 Field names must be unique. They can contain up to 100 characters.
1 Use descriptive names that clearly identify the contents of the field. Avoid abbreviations,
acronyms, or other terms that may cause confusion.
1 Don’t use any of the following symbols or words in the field name:
1 , (comma) + – * / ^ & = ≠ > < ≥ ≤ ( ) [ ] } " ; (semicolon) : (colon) :: (relational indicator)
$
(variable indicator)
1 AND, OR, XOR, NOT, or the name of any FileMaker Pro function
1 Don’t begin a field name to be used in a calculation formula with a space, period (.), or number.
1 Use _ (underscore) in place of a space to avoid restrictions in ODBC (Open Database
Connectivity) or JDBC (Java Database Connectivity), exporting, web publishing, and other
operations.
1 If you’re exchanging data with another application, check the field naming restrictions in the file
formats supported by the other application.
1 If you’re using ODBC or JDBC to share FileMaker Pro data, avoid using SQL keywords in field
names.
This field stores only numbers
This field calculates a value based on
another value in the record
(“Discount” is 20% of “Unit Price”)
This field stores multiple values
FB11Product ID
Focaccia
Product Name
BreadsCategory
PlainFlavor
$6.95Unit Price
$1.39Discount
Herb
These fields store text
Chapter 3 | Designing and creating solutions 44
About choosing a field type
When you define a field, you select a field type based on the kind of information the field will
contain. The field type determines what kind of data can be entered and what kinds of operations
FileMaker
Pro can perform with the data. FileMaker Pro uses the field type to interpret the data for
tasks like sorting records and performing calculations.
Select this
field type
If the field data will be
Text Letters, symbols, and/or numbers used as text per field repetition, limited by available RAM and
disk space. Indexes are nominally based on the first 100 characters of each word or value. Text
fields may contain carriage returns.
Number Values up to 800 digits or other characters, and the negative values of the same range. Number
fields can also contain Boolean values (0 or 1), to indicate, for example, true, false, yes, and no.
Number fields can’t contain carriage returns.
Date Dates only. Uses the Gregorian calendar with a range of 1/1/0001...12/31/4000. Month, day,
and year order is based on system settings when the file is created.
Time Times only. A time field can contain the hours, minutes, and seconds portion of a time. A time
field can contain a negative time duration, for example, -08:40:00.
Timestamp Dates and times to reference a fixed point in calendar time. For example, 10/25/2014 2:39:46 AM
Container A file of any type, such as a picture, a PDF, or a multimedia file. You can set up storage and
display options for the field. You can reference container fields in calculations and summary
fields. You can't find or sort records based on container fields, but you can define text fields to
describe or identify them. Then, you can find or sort records based on the description or
identifying number in the text field. Files in container fields can be embedded, stored as a
reference, or stored externally.
Calculation The result of a calculation formula that uses field values from the current record or related
records. The formula can use values of all field types. The result can be one of these types of
data: text, number, date, time, timestamp, or container.
Summary A value that’s produced by summarizing field values from more than one record in the same table.

Chapter 3 | Designing and creating solutions 45
Keep the following points in mind:
1 Any field type except summary can store a global value. For more information, see “About
indexing and storage options” on page 52.
1 Be sure to use a date field (instead of a text or number field) to store dates. To avoid confusion
when using dates, always use four-digit years.
1 Use text fields instead of number fields to store postal codes, phone numbers, and other values
with leading zeroes or characters like hyphens or parentheses.
1 Although you can’t find or sort records based on a container field, you can define a text field to
describe or identify the contents of the container. Then, you can find or sort records based on
the data in that text field.
To change the way data is displayed in text, number, date, time, and timestamp fields, see
“Formatting field data on a layout” on page 76.
Summary fields produce results
from values in multiple records
Salesperson Item Qty Extended Price
David Michaels FB3 1 $3.95
David Michaels FB4 1 $17.50
David Michaels FB1 2 $19.90
David Michaels FB5 3 $52.50
Total $93.85
Sophie Tang FB6 2 $39.00
Sophie Tang FB7 5 $77.50
Sophie Tang FB2 2 $45.00
Total $161.50
Grand Total $255.35
Sales Report
Calculation fields produce results from values in
the current record or related records
Favorite Bakery Confidential June 2014

Chapter 3 | Designing and creating solutions 46
Creating and changing fields in the Field Picker dialog box
When you create a new file, FileMaker Pro opens the file in Layout mode, and displays a blank
layout and the Field Picker dialog box. Use the Field Picker dialog box to define fields for the file,
and to add or change fields for an existing layout.
Note Fields are not automatically added to the layout when you define them in the Field Picker
dialog box. To have fields placed on a layout when you define them, select Add newly defined
fields to current layout in the Layout tab of the Preferences dialog box before you define the
fields.
1. If the Field Picker dialog box is not open, in Layout mode, click in the layout bar.
2. In the Field Picker dialog box, add, delete, or change fields.
To Do this
Add a field Click New Field. A placeholder Field is created in the fields list, with a field
type assigned. With the field selected, type a new name for the field. See
“About naming fields” on page 43.
Change the field type Click the field type and choose a new field type from the list. See “About
choosing a field type” on page 44.
Important Changing the field type can permanently and irretrievably
erase data.
Set options for the field Right-click the field and choose Field Options. See “Setting options for
fields” on page 50.
Delete a field Right-click the field and choose Delete Field.
To delete multiple fields at a time, select the fields, then right-click and
choose Delete Field.
Important Before you delete a field, confirm that you don’t need any of
the data it contains.
Change a field’s name Windows: Double-click the field, then type a new field name.
OS X: Select the field, then click the field name and type a new field name.
Display the Manage
Database dialog box
Click to add a field to
the database
Fields appear here
as you add them
Specify settings for position
and labels of fields dragged
to the layout
Search for fields
Sort fields
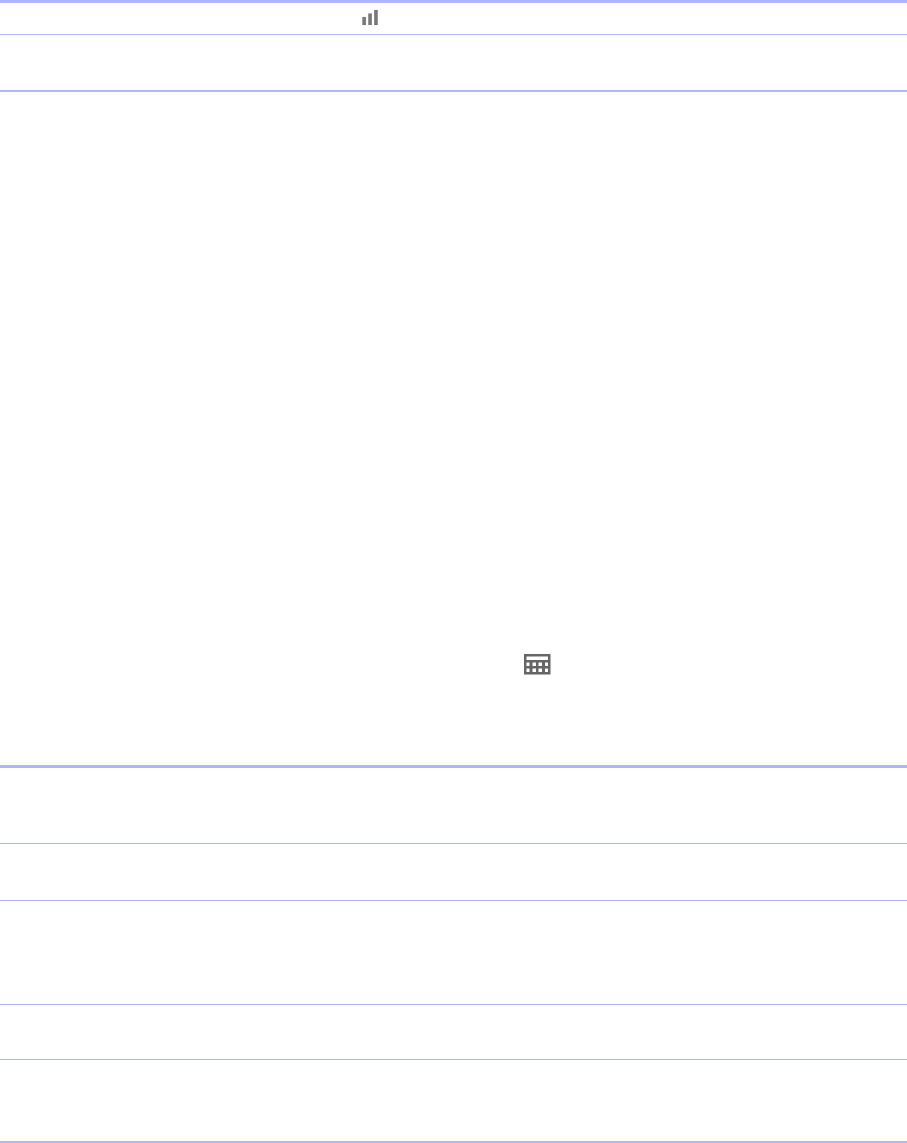
Chapter 3 | Designing and creating solutions 47
3. Repeat step 2 to continue defining fields.
4. When you drag fields to the layout, by default the fields are placed vertically on the layout, with
field labels to the left of the fields. To change these settings, click Drag Options before you
drag the fields to the layout.
1 To change the position (horizontal or vertical) in which fields are placed on the layout, for
Field Placement, click a choice.
1 To specify the position of field labels, for Labels, click a choice.
Subsequent fields that are added to the Field Picker dialog box use the current drag settings.
Note Changes to the drag settings have no effect on fields that are already on the layout.
5. Select the fields to place on the layout, then drag them to the layout.
6. Close the Field Picker dialog box by clicking the close button or pressing Esc.
Note To create and change fields in the Manage Database dialog box, see Help.
Creating and changing fields in Table View
1. With the file open, in Browse mode, click Table View in the layout bar.
2. Create new fields or change existing fields.
For information about working with data in Table View (for example, adding, deleting, and sorting
records), see
“Working with data in Table View” on page 26.
Sort fields in the list Click , then choose how to sort the fields.
Locate a field in a long list Type the field name in the search box near the top of the Field Picker
dialog box.
To Do this
Create a field To create the first field, click Create Field in the first column heading. To
create additional fields, click + in the column heading, or click in the right
margin.
Change a field name Double-click the column heading for the field, then type the new name.
See
“About naming fields” on page 43.
Choose a field type Right-click the column heading, choose Field > Field Type, and choose a
field type. See
“About choosing a field type” on page 44.
Important Changing the field type can permanently and irretrievably
erase data.
Set field options Right-click the column heading, then choose Field > Field Options. See
“Setting options for fields” on page 50.
Delete a field Right-click the column heading, then choose Field > Delete Field.
Important Before you delete a field, confirm that you don’t need any of
the data it contains.
To Do this

Chapter 3 | Designing and creating solutions 48
Creating calculation fields
1. In Layout mode, click .
2. In the Field Picker dialog box, click New Field and type a name for the calculation field.
3. Click the field type and choose Calculation.
4. In the Specify Calculation dialog box, if necessary, for Evaluate this calculation from the
context of, choose a table from the list.
Setting the context for a calculation is only necessary when you’re creating a calculation field in
a source table that has two or more occurrences in the relationships graph. The source table is
the table defined in the Tables tab of the Manage Database dialog box. The choice you make
may affect the calculation results, particularly if your calculation will include fields in related tables.
5. Build a formula for your calculation.
In the calculation pane, click where you want the item to appear, then do the following. You can
also type the formula into the box.
Procedures for working with formulas and a reference to all FileMaker Pro functions (organized
alphabetically or by category) are available in Help.
6. Select calculation options for the field.
To add a Do this
Reference to a field In the fields pane, double-click a field name.
To display field names from another table, choose a table from the table list.
Mathematical or text operator In the list to the right of the calculation pane, click an operator. (Quotation
marks and parentheses are copied to the formula as a pair, with the insertion
point blinking in the middle).
Comparison or logical operator,
or an exponent
For Operators, choose an operator from the list.
Constant value Type the value.
A constant can be text, number, date, or time. Use date constants with the
functions Date and GetAsDate, time constants with the functions Time and
GetAsTime, and timestamp constants with the functions Timestamp and
GetAsTimestamp.
Function In the functions pane, double-click a function (a predefined, named formula
that performs a specific calculation and returns a single, specific value). In the
calculation pane, replace the placeholder parameter with a value or
expression.

Chapter 3 | Designing and creating solutions 49
7. To select indexing and global storage options for the field, click Storage Options, select
options in the Storage Options dialog box, then click OK.
See “Setting options for fields” on page 50.
8. Click OK to close the Specify Calculation dialog box.
9. Drag the field to the layout.
Note If your FileMaker Pro file accesses data from external ODBC data sources, you can add
supplemental fields to specify calculations using external data. For more information, see
“Using
supplemental fields” on page 50.
Creating summary fields
Use summary fields to calculate values such as subtotals, averages, and grand totals across
multiple records. For example, a summary field can display in a report the grand total of all sales
in the month of May.
Use the New Layout/Report assistant to create a report with grouped data (data in a summary
field). See
“Creating layouts and reports” on page 54.
Tip You can use Table View in Browse mode to quickly create a dynamic report that groups your
data by a field, displays subtotals for a field, or creates subtotals for each group of data.
To Do this
Set the field type of the result Choose a data type for Calculation result is <value>. Choose the correct
type for the result. See “About choosing a field type” on page 44.
Make a calculated field
repeating
Select Number of repetitions, then type the number of repetitions (up to
32,000).
Prevent calculation if all
referenced fields are empty
Select Do not evaluate if all referenced fields are empty.
When enabled, FileMaker Pro does not evaluate a calculation if all fields used
by the calculation are empty.
Choose field references
Formula box
Choose operators
Choose
functions
Choose a formula
result type
Choose indexing and
storage options
Make the calculated field repeating
Choose a table
Calculate only if at least one field in
the formula has a value
Choose the table from which the
calculation will be evaluated
Search for a function

Chapter 3 | Designing and creating solutions 50
The value in a summary field can change depending on where you place the field on a layout, how
many records are in the found set, whether the records are sorted, and which mode you’re using.
If you’re modifying a layout that contains a summary field, you must know about layout parts to get
the results you want (see
“Working with layout parts” on page 78).
1. In Layout mode, click .
2. In the Field Picker dialog box, click New Field and type a name for the field.
3. Click the field type and choose Summary, then specify options for the summary field.
Using supplemental fields
If your FileMaker Pro file accesses data from external ODBC data sources, you can use
supplemental fields to display unstored calculation and summary results using ODBC data.
Because you can’t use FileMaker
Pro to change the schema of an external ODBC database,
supplemental fields are the only fields you can add to external tables.
For information about how to access and work with SQL data interactively, see “Working with external
data sources” on page 108.
Setting options for fields
You can set field options when you define a field or at a later time. You use the Options for Field
dialog box to set the following options for all field types except summary:
1 entering default data into a field
1 checking data against validation requirements
1 making a repeating field
1 creating an index
1 storing container data externally
1 storing a global value
1 setting Furigana input options (Japanese language fields only)
Some field options help ensure the accuracy and consistency of your data. For example, if you
type Frnc instead of France into the Country field, you won’t find that record when you later search
for all customers from France. To be sure that all country names are entered correctly, you can
define a value list containing the names, then select the Member of value list validation option
for the Country field. When you enter data into the field, the data must match a value in the list.
Keep the following points in mind:
1 To set options for summary fields, see “Creating summary fields” on page 49.
1 For calculation fields, you can set only indexing and storage options.
1 You can set field options while you’re working in Table View, Form View, or List View.
To define options for fields:
1. With the file open, in Layout mode, click .
2. In the Field Picker dialog box, right-click the field and choose Field Options.

Chapter 3 | Designing and creating solutions 51
3. In the Options for Field dialog box, click a tab.
To Click
Automatically enter a default value into a field
for each record
Auto-Enter
Define field validation options to ensure that
data is entered into the field correctly.
FileMaker
Pro displays a message if you
enter data incorrectly
Validation
Important To avoid confusion when using dates in
FileMaker Pro, set date field validation options to make sure
dates are always entered with four-digit years.
Set options for indexing fields and for storing
the results of calculations, and set data
storage options for container fields
Storage
See “About indexing and storage options” on page 52 and
“Creating calculation fields” on page 48.
Set options for Furigana fields Furigana
Select options for
entering default
data in the field
Click Auto-Enter
Auto-Enter options for fields
Select validation
options for the field
Click Validation
Validation options for fields

Chapter 3 | Designing and creating solutions 52
.
For information on value lists, see “Setting up fields to display checkbox sets and other controls
on a layout” on page 74.
About indexing and storage options
FileMaker Pro provides options for indexing fields and for storing the results of calculations. You
can:
1 Create an index, which is a list of the values stored in a field. An index greatly speeds searches,
but takes up space on your disk. You can index text, number, date, time, and timestamp fields.
You can also index calculation fields if the results are text, numbers, dates, times, or timestamps.
1 Store the result of a calculation field in your database, or you can have FileMaker Pro perform
the calculation only when needed (unstored). Storing the result is faster but takes up more
space on the disk. You can specify storage options for text, number, date, time, timestamp, and
calculation fields.
Click Storage
Select the
storage option for
the field
Storage options for all field types except container fields
Select storage
options for a
container field
Storage options for container fields

Chapter 3 | Designing and creating solutions 53
1 Set any field (except summary fields) to share one value across all records in a file if you select
Use global storage in the Storage tab of the Options for Field dialog box. Fields defined with
global storage are also referred to as global fields.
1 Store data for a container field in a location that’s external to the file, such as in a different folder
or directory on the local or a host computer.
Creating database tables
Use database tables to organize and group your data by a common characteristic or principle.
Your database can contain as many tables as you need to organize your data.
In addition to storing data, FileMaker Pro uses tables to describe relationships in the relationships
graph, and establish the context for layouts and some calculations. In FileMaker
Pro, context is
the starting point from which calculations and scripts are begun and from which a relationship is
evaluated in the relationships graph.
When you create a new file, FileMaker Pro automatically creates the first table and the first layout.
The table and the layout are given the same name as the file.
You create additional tables in the Manage Database dialog box.
1. With the database open, choose File menu > Manage > Database.
2. In the Manage Database dialog box, click the Tables tab.
3. In the Table Name box, type a name for the table, then click Create.
The table can be renamed or deleted. Tables you add to a file are automatically displayed in
the relationships graph.
4. Continue to define tables, or click the Fields tab to define fields.
For information about relationships, tables, and the relationships graph, see chapter 4, “Working
with related tables and files.”
Type a name
for the table
Click Tables

Chapter 3 | Designing and creating solutions 54
Creating layouts and reports
FileMaker Pro layouts determine how information is organized for viewing, printing, reporting,
finding, and entering data. Layouts don’t store your data—they just display it. Layouts are
sometimes called reports, especially when printed.
You can create as many layouts as you need for a file (for example, layouts for entering data,
reporting summaries, or printing mailing labels). You can change a layout’s design without
affecting the data or other layouts for the file. Layouts can include certain fields and exclude
others. When you change the data in a field (in Browse mode), the changes are reflected in the
same field for the same record on all the layouts in the file.
When you create a file (without using a Starter Solution), FileMaker Pro automatically creates a
layout for the initial table in the file, and for each newly added table that contains fields.
You create additional layouts by switching to Layout mode and using the New Layout/Report
assistant, which guides you through creating a layout according to options you choose. Use the
different layout types for various purposes, like displaying a data entry screen or printing a totaled
sales report or mailing labels. You can then customize each layout by using the design tools that
are available in Layout mode.
Important FileMaker Pro considers the selected device, printer, and print or page setup
information when it calculates margins and other measurements on the layout. Printer and print
settings depend on the printer and system software you’re using. Refer to your printer and system
documentation for more information
.
Fields: use for entering
and displaying data
Layout pop-up menu
Mode pop-up menu
Buttons: use to automate
frequent tasks
Layout text: use for titles,
column headings, field
labels, instructions, and
form letters
Parts: use navigation
parts, headers, footers, the
body, and summaries to
divide a layout into
special-purpose areas

Chapter 3 | Designing and creating solutions 55
Keep the following points in mind:
1 If you are designing solutions for use with FileMaker Go or FileMaker WebDirect, see the
design guidelines in FileMaker
Go Development Guide or FileMaker WebDirect Guide.
1 If you intend to print the new layout in landscape orientation or on a special paper size, in
Browse or Layout mode, choose File menu
> Print Setup (Windows) or File menu >
Page
Setup (OS X), confirm the orientation and paper settings, then click OK. Modified Print
Setup and Page Setup settings affect all other layouts in the current file, so you may need to
change these settings later to print other layouts properly.
1 You can easily manage the layouts and layout folders in your file using the Manage Layouts
dialog box. For example, add, delete, and duplicate layouts and folders, open multiple layouts,
and change the order in which layouts and folders appear in the Layout pop-up menu.
To create a layout:
1. In Layout mode, click New Layout/Report in the status toolbar.
Or, in Browse mode, choose File menu > Manage > Layouts, and click New.
You see the New Layout/Report assistant, which helps you create a layout. As you make your
choices, additional options are presented to you. For example, if you choose Custom Device,
you can specify a width and height for the device. For some types of layouts, such as labels,
envelopes, and reports, you see additional panels.
2. If the file has multiple tables, for Show records from, choose a table.
3. For Layout Name, give the layout a name.
4. Choose the type of layout to create.
For a description of each layout type, see “About layout types,” below.
5. Depending on the layout type you choose, additional options may become available.
6. When you have finished making your choices, click Finish to create the layout.
7. For layouts designed for computers or touch devices, add fields to the layout.
See “Creating and changing fields” on page 43.
To Do this
See an onscreen Help topic that explains the
choices in the current panel
Windows: Press F1 (Windows) or Command-? OS X).
If the layout you’re creating has additional panels (such as
for labels, envelopes, or reports), you can also click
(Windows) or (OS X) to get information about those
panels.
Accept the settings in the panel and continue to the
next panel (available for labels, envelopes, and
reports layouts)
Click Continue or Next.
Accept the settings in the panel but go back to the
previous panel (available for labels, envelopes,
and reports layouts)
Click Back.
Close the assistant without saving any of your
choices
Click Cancel.
Chapter 3 | Designing and creating solutions 56
Keep the following points in mind:
1 You can use the tools and commands in Layout mode to further customize the layout. See
“Working with objects on a layout” on page 66 and “Working with fields on a layout” on page 72.
1 If you click Finish in the first panel of the New Layout/Report assistant without choosing a
layout type, FileMaker
Pro creates a blank layout. A blank layout contains no fields; you add the
fields in Layout mode. A blank layout is a good starting point for complex layouts (for example,
a data entry screen or form letter).
1 Each layout that you create is assigned a layout theme. If the new layout is the same type
(Computer, Touch Device, or Printer) as the current layout, the same theme is assigned to the
new layout; if the new layout is a different type, the appropriate default theme is assigned. See
“Working with layout themes” on page 60.
About layout types
You can use the New Layout/Report assistant to create several types of layouts, which are
described below.
Computer
Computer layouts are designed to display within the dimensions of most laptop and desktop
computer screens. After you choose Computer, you choose the view in which to display the layout
(Form View, List View, or Table View), or you can create a report (see “Report,” below). After you
finish the assistant, you add the fields and any layout objects and embellishments to the layout.
The default theme for Computer layouts is Enlightened.
Touch Device
Touch Device layouts are designed to display on touch-compatible input devices, including iPad,
iPad mini, or iPhone, or on a device with dimensions that you can customize in the assistant. After
you choose Touch Device, you choose the view in which to display the layout. You can also
choose the orientation—portrait or landscape—for the layout. For custom devices, you can specify
the layout's width and height. After you finish the assistant, you add the fields and any layout
objects and embellishments to the layout.
The default theme for Touch Device layouts is Enlightened Touch.
Printer
Printer layouts are designed for printing data on labels (horizontal or vertical), envelopes, and in
reports. The Printer layout choices are described below.
The default theme for Printer layouts is Enlightened Print.

Chapter 3 | Designing and creating solutions 57
Labels
Use a Labels layout to arrange fields you select to print on one of the predefined standard label
sizes. (FileMaker
Pro includes the dimensions of a large number of standard label types.) If the
label type isn't available, you can specify custom label dimensions.
You can only print (or preview) data; you cannot add information. (Use another layout type for data
entry or finding data.)
For more information about creating a Labels layout and printing labels, see “Printing the labels
or envelope” on page 59.
Vertical Labels
With the Vertical Labels layout, Asian and full-width characters are rotated so that labels can be
used vertically.
For more information about vertical writing, see “Formatting fields and text for vertical writing” on
page 77.
Labels in Layout mode
Labels in Preview mode
Chapter 3 | Designing and creating solutions 58
Envelopes
Use an Envelopes layout to print the fields you select, arranged to print on a standard “Number
10” business envelope. You can only print (or preview) data; you can't add information. (Use
another layout type for data entry or finding data.)
For more information about creating an Envelopes layout and printing on envelopes, see “Printing
the labels or envelope” on page 59.
Report
The New Layout/Report assistant lets you define varied report formats. You can create a Report
layout with simple rows and columns of data (formerly a predefined layout type known as the List
view layout), or a complex report with data grouped by specified values and including subtotals
and grand totals.
You can also group records by sorting data by selected fields. You can then subtotal, or
subsummarize, data in these groups (for example, group sales data by region, then subtotal sales
for each region).
When you create a Report layout in the assistant, you can then choose to:
1 include subtotals and grand totals in the report
1 add header and footer parts with static text (like your company's name), dynamic text (like
the page number or current date), or a graphic (like your company logo)
1 group records by sorting; you can then subtotal or subsummarize data in the groups (for
example, group sales data by region, then subtotal sales for each region)
1 save information in a script to rerun the report (for example, switch to the report layout and
sort the data)
You can modify any of these options after you finish the assistant.
Creating Labels and Envelopes layouts
When you create a Labels or Vertical Labels layout, FileMaker Pro provides the dimensions of
numerous standard label types and their codes (for example, Avery 4014). If the label type isn't
available, you can specify custom label dimensions.
Chapter 3 | Designing and creating solutions 59
Labels layouts and Envelopes layouts use merge fields, which are placeholder fields for displaying
and printing only; you can’t enter data into merge fields. Merge fields expand and contract to fit
the data in the field as needed, and close up space if the field is empty. (See
“About merge fields”
on page 75.)
Setting up the layout
1. In Layout mode, click New Layout/Report.
The New Layout/Report assistant appears. For onscreen help as you use the assistant, press
F1 (Windows) or Command-? (OS
X) in each panel.
2. Choose a table, and type a name for the layout.
3. Choose Printer, then choose either Labels (for data that reads top to bottom horizontally) or
Vertical Labels (for data that reads right to left vertically).
For an Envelopes layout, choose Printer, choose Envelopes, and click Continue. Then skip
to “Choosing and formatting the merge fields,” below.
4. Click Continue.
5. In the Specify Label Layout panel, specify the measurements of your mailing labels:
1 To choose a predefined measurement based on common label types, for Use label
measurements for, choose the code that matches your labels. (This information is on the
package your labels came in.)
1 To specify a custom measurement, choose Use custom measurements, and enter values
for Labels across the page, Width, and Height. Measure the unused margins on the label
stock. Then select Fixed page margins and enter values for Top, Bottom, Left, and Right.
6. Click Next.
Choosing and formatting the merge fields
1. In the next panel, for the Available fields list, double-click the first field whose data you want
on the labels or envelope.
<<field name>> appears in the Label contents or the Envelope contents area. Angle
brackets indicate that this is a merge field, and field data will display in and print on the labels
or envelope.
To include fields from related tables, choose the table from Available fields.
2. Continue selecting fields.
3. Include all punctuation, blank spaces, and line breaks (to place a merge field on the next line)
that you want printed.
4. Click Finish.
Printing the labels or envelope
1. Load the labels or the envelope into your printer.
2. Choose File menu > Print, specify options, and click Print.

Chapter 3 | Designing and creating solutions 60
Keep the following points in mind:
1 To specify how labels will print on the page, choose Layouts menu > Layout Setup, and click
the Printing tab. Then choose the number of columns (labels) across and the direction in which
you want the labels printed, and set custom page margins, if needed.
1 You may need to adjust your printer settings to print the labels correctly. Choose File menu >
Print Setup (Windows) or Page Setup (OS
X).
Working with layout themes
Use FileMaker Pro themes to enhance the appearance of a layout or report and to give all your
layouts a consistent look. A theme affects characteristics of the layout, including the background
color, field borders and fill, and text attributes in and outside of fields. A theme does not control the
placement or behavior of fields or objects. You can change the theme of an existing layout in
Layout mode.
To change the theme of a layout:
1. Display the layout.
2. In Layout mode, choose Layouts menu > Change Theme, or click in the layout bar.
3. Select a theme from the current file in the Layout themes list, or import a theme from another
FileMaker
Pro file.
To import a theme, click Import Themes, choose the file containing the theme(s) to import and
click Open. Select themes in the Import Themes dialog box and click OK. Then select a theme
in the Layout themes list.
4. Click OK to apply the selected theme to the current layout.
Select a theme
from a category
Import a theme
from another
FileMaker Pro file
You see a preview of
the selected theme

Chapter 3 | Designing and creating solutions 61
Keep the following points in mind:
1 When you change a layout’s theme, FileMaker Pro applies the attributes of the new theme to
all objects on the layout except the following:
1 The font and font size remain from the original layout or theme.
1 Buttons created using versions of FileMaker Pro earlier than version 12 retain their original
formatting.
1 Objects on the layout background that are filled with an image, or a layout background that
is filled with an image, retain the image.
1 You may need to resize layout parts and layout objects after a theme is applied for the layout
to display properly.
1 If you’re creating a layout to be used with FileMaker Go, choose one of the Touch themes.
1 If you’re creating a layout to be printed, choose one of the Print themes.
1 If you're making many changes to styles and intend to save them as a custom theme, start with
the Minimalist theme or Minimalist Touch theme, which has no custom styles.
1 The styles of layout objects, layout parts, and the layout background are controlled by the
layout’s theme. If the pre-designed themes do not display the styles you want, you can create
and apply a custom theme. See the next section,
“Working with layout object, part, and
background styles.”
1 To see which themes are in use in a file, or to import themes from other files, choose File
menu
>Manage >Themes.
Working with layout object, part, and background styles
Each layout theme includes default styles for the objects and layout parts that you create while
using that theme. Styles give objects and parts on a layout a consistent appearance. They also
save you the time of reassigning formatting attributes each time you create a new object or part.
A theme also includes a default style for the layout background.
Some themes include additional default styles for some objects. For objects that have multiple
components, each component has a separate style. For example, portals have a Portal style,
which formats the entire object, and a Portal: Rows style, which formats only the rows of the portal.
Select an action to
perform on the
selected theme
Themes used in the
current file
Number of layouts that
use each theme

Chapter 3 | Designing and creating solutions 62
You can modify default styles or design new styles and save them for use on the current layout.
When you edit and save formatting attributes for styles that are applied to multiple objects or layout
parts, your changes are applied to all objects and parts that use those styles on the current layout.
You can also create new styles with custom names, which you can then apply to objects, layout
parts, or the layout background on the current layout. Any styles you modify and save, or any
custom styles that you create, apply only to the current layout.
To use your custom styles on other layouts, save your styles to a theme. You can save custom
styles to FileMaker
Pro themes or you can create new custom themes.
Use the Styles tab in the Inspector to view and apply defined styles.
Name of the current theme
Styles saved to the
current theme
Object type
Click to create or
change styles

Chapter 3 | Designing and creating solutions 63
Use the Appearance tab in the Inspector to create and modify styles and themes.
For details about working with styles for layout objects, layout parts, and the layout background,
and about saving styles to themes, see Help.
Setting up a layout to print records in columns
You can set up a layout to print (or preview) records in columns, for example, for a directory of
names and addresses. When you set up records to print in columns, all the field values (and
labels, if specified) for one record are printed together in a block (much like on a label), then all
the values for the next record are printed together, and so on. You only see multiple columns in
Layout and Preview modes and when you print (not in Browse mode or Find mode).
A gray arrow indicates all styles have
been saved to the theme
Set the fill, line, and corner
radius style
Set effects for shadows and
object padding
A red arrow indicates that style
changes have been made but
not yet saved at the layout level
Object type
Object state

Chapter 3 | Designing and creating solutions 64
You can choose to arrange columns across the page or down the page.
Setting up columns in a layout
1. Choose a printer, and print setup or page setup options.
FileMaker Pro considers the selected printer, and print or page setup information when it
calculates margins and other measurements on the layout.
2. In Layout mode, create a layout or choose a layout from the Layout pop-up menu.
It’s easiest to start with a Blank layout or a layout with no objects in the body part.
3. Choose Layouts menu > Layout Setup.
4. In the Layout Setup dialog box, click the Printing tab, select Print in <value> columns, select
options for the columns, then click OK.
5. On the layout, you see vertical lines indicating columns.
To Do this
Specify the number of columns For Print in <value> columns, type a number between 1 and 99.
Arrange records to flow across the page first
(left to right, a row at a time)
Select Across first.
Use this option for reports like labels, to use the fewest number
of rows and preserve label stock.
Arrange records to flow down the page first
(top to bottom, a column at a time)
Select Down first.
Use this option for reports like directories, where you read from
top to bottom, column by column.
Down first
1
2
3
4
5
6
7
8
1
3
5
7
2
4
6
8
Across first

Chapter 3 | Designing and creating solutions 65
6. Place or arrange fields and other layout objects so they are contained within the sample column
on the left.
Use merge fields or fields or objects with sliding enabled to fit more data into the width of a
column. With either of these two features, fields can extend into the gray area of the second
column, and blank space in fields is eliminated when you view or print data.
Changing the width of columns
The initial width of each column is calculated based on the paper size, orientation, and any
margins you have set. To change the width of columns, do one of the following:
If you change the number of columns, FileMaker Pro adjusts the width of the columns to fit within
the width of the paper size you have defined, not including fixed margins. You may need to
readjust fields to fit within the sample column.
To Do this
Interactively adjust the width of
the columns
Drag the right column boundary (the vertical dashed line at the right edge of the
sample column). If you widen the column, you see a medium-gray area that
indicates a “gutter” area that won’t print.
Precisely measure and adjust the
width of the columns
Click Inspector in the layout bar. Click Position. Position the pointer over
the right column boundary, hold down the mouse button (be careful not to drag
the column width), and read the column Width value in the Size area.
Sample column
Manually resize column
widths by dragging

Chapter 3 | Designing and creating solutions 66
Working with objects on a layout
An object is a discrete element—a field, text, a graphic object (such as an oval or imported
picture), a button, a button bar, a portal (for displaying rows of related records), a tab control or
slide control, a popover button and its popover, a chart, or a web viewer—that you can select,
move, resize, delete, copy, format, or otherwise change. Place objects on a layout to enhance its
design.
For each type of object you work with, you use specific tools from the status toolbar.
Note If you don’t see the status toolbar at the top of the document window, the status toolbar might
be hidden. Make sure you’re in Layout mode, then click the status toolbar control button
at the
bottom-left corner of the document window (or choose View menu > Status Toolbar).
Organizing data with panel controls and popovers
Tab controls, slide controls, and popovers are useful ways of organizing data. For example, you
could create tab panels for various categories of products.
1 To create a tab control, in Layout mode, choose Insert menu > Tab Control or click the Tab
Control tool
.
Status toolbar in Layout mode (Windows)
Status toolbar in Layout mode (OS X)
Tab control
Click a tab to display another tab panel
Tab panel
Tab control in Browse mode

Chapter 3 | Designing and creating solutions 67
1 To create a slide control, in Layout mode, choose Insert menu > Slide Control or click the
Slide Control tool
.
1 To create a popover, in Layout mode, choose Insert menu > Popover Button or click the
Popover Button tool
.
Slide control
Click a dot to display another slide panel
Slide panel
Slide control in Browse mode
Popover
Popover button—click
to open the popover
Popover button and popover in Browse mode

Chapter 3 | Designing and creating solutions 68
Using the Inspector to format objects
In Layout mode, you can use the Inspector to view and modify the settings for objects. Each tab
focuses on a different aspect of formatting. Hold your pointer over options in each tab to see a
description of what they do.
To open the Inspector:
1 Click Inspector in the layout bar.
1 Choose View menu > Inspector.
You can open multiple Inspector windows to make it easier to work on a layout. For example,
display the Data tab of an Inspector window and the Appearance tab of another Inspector window
to have access to the options on each tab. To open another Inspector window, choose View
menu
> New Inspector.
Click the tabs to format
different aspects of an object
Enter settings for an object’s
position on the layout
Anchor the object to the top,
bottom, left, or right side of the
window (in Browse or Find mode)
or the left or right (in Preview mode
or when printing)
Select settings for an object’s
relative position, and for
resizing an object
Select settings for
printing and previewing
objects
Select settings for working with
the grid
Chapter 3 | Designing and creating solutions 69
Using tools to precisely position objects
FileMaker Pro provides several tools to help you precisely create, size, reshape, move, and
position objects in Layout mode.
To show or hide page breaks in Layout mode, choose View menu > Page Breaks.
Note To use the Inspector to position objects, see Help.
Rulers
Showing the rulers displays a horizontal and vertical ruler along the edge of a layout. Guide lines
on each ruler track the position of the pointer as you move the pointer on the layout.
1 To show the rulers, in Layout mode, choose View menu > Rulers.
1 To hide the rulers, choose View menu > Rulers again.
Grid
Showing the grid displays a series of nonprinting intersecting horizontal and vertical lines. The grid
aligns objects you create, resize, move, or position. Objects “snap to” the grid to help you create
and edit objects more precisely. Gridlines adjust when you change the unit of measure.
To show or hide the grid, do one of these:
1 In the Inspector, click the Position tab. In the Grid area, select or deselect Show grid.
1 Choose View menu > Grid > Show Grid. To hide the grid, choose Show Grid again.
Guides
Guides help you align objects within the same layout and across multiple layouts.
1 To create a vertical guide, drag out from the vertical ruler.
1 To create a horizontal guide, drag down from the horizontal ruler.
If the ruler isn’t displayed, choose View menu > Rulers.

Chapter 3 | Designing and creating solutions 70
Dynamic guides
When you drag objects to move, resize, or position them on a layout, dynamic guides appear near
or on the objects to help you create and edit them more precisely. Dynamic guides also “snap to”
the upper and lower boundaries and the centers of objects as you move, resize, or position them.
Dynamic guides also appear when you use the keyboard to move objects, but they do not “snap
to” objects when you move them this way.
To use dynamic guides:
1 To turn on dynamic guides, in Layout mode, choose View menu > Dynamic Guides.
1 To turn off dynamic guides, choose View menu > Dynamic Guides again.
Screen stencils
You can display guides that help you design layouts optimally for iPad, iPhone, and common
desktop resolutions. You can also create screen stencils with custom dimensions.
To display a screen stencil, click the arrow on Screen Stencil in the layout bar, then choose
a size from the list. You can display more than one screen stencil at a time on the same layout. To
create a screen stencil, choose Custom Size from the menu.
Dynamic guides
Guides
Screen
stencil
Rulers

Chapter 3 | Designing and creating solutions 71
Selecting objects
To work with an object on a layout, select it in Layout mode. You see small squares, or handles,
surrounding the selected object.
Note If an object’s selection handles display as , the object is locked and can’t be changed.
To select an object, click the Selection tool in the status toolbar. The pointer becomes an
arrow pointer. Then do one of the following.
To deselect selected objects, click a blank area of the layout or any tool in the status toolbar. Or,
press Shift and click selected objects.
To select In Layout mode, do this
One object With the arrow pointer, click the object. (If the object is transparent, click its border.)
Several objects at once Drag the arrow pointer to make a selection box that includes the objects. The selection
box does not have to completely surround the objects. To avoid including partially selected
objects, press Ctrl (Windows) or 2 (OS
X) as you drag.
Or, press Shift as you click each object individually.
All objects on the layout Choose Edit menu > Select All.
All objects of the same
type (for example, all
text objects or all
rectangles)
Click the tool for the type of object to select, then choose Edit menu > Select All. This
method does not select buttons.
Or, with the arrow pointer, click a field, press Shift (Windows) or Option (OS X), and
choose Edit menu
> Select All (Windows) or Select Same (OS X).
All fields With the arrow pointer, click a field, press Shift (Windows) or Option (OS X), and choose
Edit menu > Select All (Windows) or Select Same (OS X).
A portal With the arrow pointer, click the border of the portal, or any other area within the portal that
doesn’t contain a field or object.
Other types of objects See Help.
Handles surround a selected
object

Chapter 3 | Designing and creating solutions 72
Working with fields on a layout
After you’ve added fields to a file, you can place the fields on a layout, remove fields, determine
control settings for data entered in fields, and determine a display format for data.
Fields on a layout are objects, which you can select, move, resize, and reshape. In Layout mode,
each field displays its field name, formatted with its attributes for font, size, style, alignment, line
spacing, and color. All fields except container fields display text baselines to indicate where the
data appears in Browse mode and to help you align fields with each other.
Note As long as you haven’t deleted a field from the database, even if the field doesn’t appear
on a layout, it still exists in the database and its data can be used in calculations and summaries.
Placing and removing fields on a layout
You can place a field anywhere on any layout, as many times as you want. (You can place only
fields that you’ve defined. See
“Creating and changing fields” on page 43.)
You get different results by placing the same field in different locations on the layout. For example:
1 Add the same summary field to a subsummary part to calculate totals for each group of sorted
records, and to a grand summary part to get totals for all the records in a table.
1 Add a field to the header or footer part to repeat data from the first record or the last record on the
page as a header or footer. (For example, add a Last Name field to the header in a directory.)
1 Add the same related field directly on a layout to see the field’s value in the first related record,
or inside a portal to see values from more than one related record. (A portal is a layout object
that displays records from related tables.)
Fields display
field names
Text baseline
Field label

Chapter 3 | Designing and creating solutions 73
Placing a field on a layout
1. In Layout mode, choose the layout from the Layout pop-up menu.
2. Do one of the following:
1 Drag a field from the Field tool in the status toolbar to the layout. As you drag the field
to the layout, you see a border and text baselines to help you align the field with other objects
on the layout. Release the mouse button when the field is where you want it.
1 To display field data in an edit box or a drop-down list, pop-up menu, checkbox set, radio
button set, or drop-down calendar, click the arrow next to the Field/Control tool
(Windows) or click and hold the Field/Control tool (OS X), then select the type of field
or control to add to the layout. Drag the crosshair to draw the field. To format and choose a
value list for the field, see
“Setting up fields to display checkbox sets and other controls on a
layout” on page 74.
1 Click in the layout bar. Then see “Creating and changing fields in the Field
Picker dialog box” on page 46.
Note If you're placing a related field in a portal, position it in the first row of the portal. Make
sure each field in the portal is from the same related table from which the portal is set up to
display records.
3. In the Specify Field dialog box, select the field to place.
To choose a field in another table, choose the table from the table list above the list of fields.
Then select a field from the fields list. Or choose Manage Database in the table list, or click
to create a relationship or table (see “Creating relationships” on page 94).
4. To include the field name as text on the layout, select Create label.
5. Click OK.
You see the field name in the field on the layout unless you have chosen to display sample data
from the current record (by choosing View menu
> Show > Sample Data). Fields from related
tables appear as ::Field Name (preceded by two colons).
Replacing a field with another field
In Layout mode, double-click the field, then select another field name in the Specify Field dialog
box and click OK.
Select the
field to add
Select to use the field
name as the field label
To place a field from
another table, choose
the table
Click to display the
Manage Database
dialog box

Chapter 3 | Designing and creating solutions 74
Removing a field from a layout
In Layout mode, click the field to select it, then press Backspace or Delete, or choose Edit menu >
Clear. Removing a field from a layout does not delete the field or its data from your database.
Setting up fields to display checkbox sets and other controls on a layout
You can format fields to display as edit boxes, drop-down lists, pop-up menus, checkbox sets,
radio button sets, and drop-down calendars. You can also format fields to auto-complete by
suggesting possible matches as the user types data in the field. All of these options aid in data
entry.
For example, use a radio button set to display a value list of frequently used text, number, date,
or time values. During data entry, users can choose from the defined values rather than type the
values.
To set up a field to display a pop-up menu, checkbox set, or other control:
1. In Layout mode, select the field.
1 If the field isn’t already on the layout, see “Placing and removing fields on a layout” on page 72.
1 If the field hasn’t been defined yet, choose File menu > Manage > Database to define a new
field.
2. Click Inspector in the layout bar, then click Data.
3. In the Field area, choose from Control Style.
When you choose different control styles, you see different options in the Inspector. For
example, you can choose the icon that indicates that a checkbox is selected.
4. Choose a value list from the Values from list.
To create a value list, click next to the Values from list.
5. Choose options for the value list, if desired.
6. To display data from a different field, click next to Display data from.
In the Specify Field dialog box, select the field to display data from. To include the field name
as text on the layout, select Create label. Click OK.
7. Save the layout.
Value list attached to Category field
Choose from a list of
values during data entry

Chapter 3 | Designing and creating solutions 75
Deciding where to place related fields
You can place related fields directly on layouts or in portals.
1 Directly on layouts: Place related fields directly on a layout to display data from the first related
record, even when there are multiple related records that match the criteria of the relationship.
(The first related record that’s displayed is determined by whether the relationship specifies a
sort order. For more information, see
“Creating relationships” on page 94.)
1 In portals: Place related fields within a portal on a layout to display data from all related records
that match the criteria of the relationship.
Note Before placing related fields on a layout, you should understand the concepts presented in
chapter 4, “Working with related tables and files.”
About merge fields
Use merge fields to combine field data and text in documents like form letters, labels, envelopes,
or contracts. You create merge fields in text blocks, which allows you to use static text and field
data together.
Merge fields shrink or expand to fit the amount of text in the field for each record. For example:
1 When the merge field <<First Name>> is between the text Dear and a colon, (as in Dear
<<First Name>>:), FileMaker
Pro displays Dear Charles: in Browse mode or Preview mode if
the First Name field contains
Charles.
1 When a merge field is on a line by itself (such as an empty Address Line 2 field in a mailing
label), FileMaker
Pro removes the blank line from the text block.
FileMaker Pro uses merge fields to create Labels and Envelopes layouts. See “Creating Labels
and Envelopes layouts” on page 58.
Note You can also use a merge variable to display data.
Each form letter will include a different address and salutation
Chapter 3 | Designing and creating solutions 76
Formatting field data on a layout
Use FileMaker Pro field formats to control how text, numeric, date, time, and timestamp data
appears on a layout, how results are displayed in calculation and summary fields, and how images
and file icons are displayed in container fields. The formats you specify don’t change the data as
it’s stored in the database, and you can specify different formats each time you place a field on a
layout (whether it’s on the same layout or a different layout). For example, if you enter
–5123 into
a number field, you can format it in one place to display as –$5,123.00 and in another place as
<5123>.
To specify formats for text, see the next section. To specify formats for number, date, time,
timestamp, and container fields, see Help.
Specifying text formats for fields
You can specify a set of text character attributes for each field. All the characters in that instance
of the field (including all repetitions of repeating fields) share the same font, size, style, color, line
spacing, tab, and paragraph settings.
You can also format characters in text fields in Browse mode (for example, italicize or underline a
word for emphasis). Unlike text formatting specified in Layout mode, this formatting is stored with
the data, and you see it in any layout that displays that field.

Chapter 3 | Designing and creating solutions 77
1. In Layout mode, select one or more fields.
2. Click Inspector in the layout bar, click Appearance, then specify formats for the field.
3. Click outside the Inspector to apply the changes.
Formatting fields and text for vertical writing
If your operating system is configured to support Japanese text entry, you can format field objects
and text objects that display Japanese text in vertical writing format. In vertical writing, characters
are displayed and read from top to bottom, with successive columns displayed vertically from right
to left. This is useful when printing addresses on labels.
When you select one or more fields, then choose Format menu > Orientation > Sideways
(Asian text only), the characters are rotated 90
degrees counter-clockwise within the field. The
field itself is not rotated. To rotate the selected fields, choose Arrange menu
> Rotate.
Depending on how you want the text to print, you can change the page orientation of the layout.
To do so, choose File menu
> Print Setup (Windows) or Page Setup (OS X), and change the
page orientation to landscape or portrait.
Specify font, style, size,
and color
Highlight text
Set vertical and
horizontal alignment,
line spacing, and
paragraph indents
Set tab position
and alignment
Type a character to fill
across to the tab
Specify options for
text baselines
Align text with radio
buttons and checkboxes
Inspector options for text in Windows

Chapter 3 | Designing and creating solutions 78
Allowing or preventing entry into fields
You can allow or prevent entry into a field. For example, you can restrict entry into a field
containing a serialized number, so the field can’t be modified. You can set separate Browse mode
and Find mode data entry options, which would allow finding serialized numbers even though they
can’t be entered.
If you allow entry into a field, you can also control whether the entire contents of the field is
selected when you click or tab into the field in Browse mode or Find mode. Otherwise,
FileMaker
Pro places the insertion point after the last character in the field.
1. In Layout mode, select one or more fields.
2. Click Inspector in the layout bar, then click Data.
3. In the Behavior area, for Field entry, select the following options:
Working with layout parts
FileMaker Pro layouts are divided into layout parts, sections of the layout that determine how data
in a field is treated and displayed. By using parts, you can control how FileMaker
Pro prints data,
for example:
1 once for each record
1 only at the top of each page
1 only before or after groups of sorted records (for example, to include a subtotal for each group
of records)
Each layout must have at least one part. Layout parts can contain fields, portals, buttons, text,
charts, and other objects. In Layout mode, gray horizontal lines mark the division between layout
parts (part boundaries), and the part labels appear in the left margin of the layout or directly in the
part above the part boundary.
Parts are assigned styles that are defined by the theme of the layout. You can use the Inspector
to customize part styles.
The New Layout/Report assistant automatically creates the appropriate layout parts depending on
the choices you make. You can add, change, or delete layout parts after you finish the assistant
as needed. (See
“Creating layouts and reports” on page 54.)
To Do this
Prevent entry into a field in Browse mode Clear Browse mode.
Prevent entry into a field in Find mode Clear Find mode.
Select the entire field's contents when the field is entered Choose Select entire contents on entry.

Chapter 3 | Designing and creating solutions 79
Body
Header
Subsummary
Trailing grand
summary
Footer
Sales Report
A subsummary below the body summarizes
data for each group of records sorted on the
break field (Salesperson)
Trailing grand summary
Footer
Favorite Bakery Confidential June 2014
Salesperson Item Qty Extended Price
David Michaels FB3 1 $3.95
David Michaels FB4 1 $17.50
David Michaels FB1 2 $19.90
David Michaels FB5 3 $52.50
Total $93.85
Sophie Tang FB6 2 $39.00
Sophie Tang FB7 5 $77.50
Sophie Tang FB2 2 $45.00
Total $161.50
Grand Total $255.35
Display part
labels vertically
or horizontally

Chapter 3 | Designing and creating solutions 80
About layout part types
The following table describes layout part types.
To include summary data on a layout (for example, subtotals, grand totals, averages, counts, and
so on), the assistant places summary fields in summary layout parts. If you want to modify a report
to add summary data, you can place summary fields in summary layout parts (see
“Creating
summary fields” on page 49).
Summary parts include grand summary and subsummary parts.
1 A grand summary part usually contains one or more summary fields that display summary
information (like totals) about all records being browsed.
1 A subsummary part usually contains one or more summary fields that display “subsummary”
information (like subtotals) for a subset of records. The records are grouped (sorted) by values
in another field—the break field. Whenever the value in the break field changes, FileMaker Pro
summarizes the values in that field across all records and displays the summarized data in
Browse and Preview modes or data is printed as a report. For example, to display the number
of items in stock by product, place the Product Name field in a subsummary part, and place the
Product Name and Stock fields in the body part.
Layout part Description
Top
navigation
Appears at the top of every screen and can contain buttons or other controls. This part cannot be
scrolled or zoomed in or out, and it does not print or display in Preview mode. Fields added to a top
navigation part use data from the current record. You can have only one top navigation part on a
layout.
Title header Appears only once at the top of the first screen or page and replaces the normal header (if one is
specified). In reports, can be used to print a separate title page. You can have only one title header
in a layout.
Header Appears at the top of every screen or page (unless you add a title header, which supersedes the
header on the first page). Use for titles or column headings (in columnar reports). You can have only
one header in a layout.
Body Each object you put in the body, including fields, text objects, and graphics, appears once for each
record in the found set. You can have only one body in a layout.
Footer Appears at the bottom of every screen or page (unless you add a title footer). You can have only one
footer in a layout.
Title footer Appears only once at the bottom of the first screen or page and replaces the normal footer (if one is
specified). You can have only one title footer in a layout.
Bottom
navigation
Appears at the bottom of every screen and can contain buttons or other controls. This part cannot
be scrolled or zoomed in or out, and it does not print or display in Preview mode. Fields added to a
bottom navigation part use data from the current record. You can have only one bottom navigation
part on a layout.

Chapter 3 | Designing and creating solutions 81
Subsummary parts appear in Table View and List View when sorted by break fields, and update
dynamically whenever data in the file is changed.
Creating and editing charts
You can create various types of charts in FileMaker Pro to compare data graphically. Before you
create a chart, think about the data comparison that you want to emphasize, then choose the
FileMaker
Pro chart type that will show the comparison clearly.
Place the Product Name break field in a
subsummary part in Layout mode
The number of items for
each product in stock is
displayed in Browse and
Preview modes or when
data is printed as a
report
Use To
Column chart (vertical)
or bar chart (horizontal)
Compare increases to decreases, highest with lowest, how many, or how often. For
example, show monthly sales for several products.
Stacked column chart
(vertical) or stacked bar
chart (horizontal)
Compare parts to the whole. For example, compare annual sales figures over several
years.
Positive/negative
column chart
Compare positive and negative values. For example, compare earnings to losses.
Pie chart Compare percentages of individual parts within the whole. For example, show the
percentage of each product sold within total sales.
Line chart Show data that changes continuously over time, such as historical financial data.

Chapter 3 | Designing and creating solutions 82
Creating a chart
The following steps describe how to create a quick chart, which FileMaker Pro sets up for you
based on the field(s) you’ve selected in Browse mode. When you create a quick chart,
FileMaker
Pro sets up the chart based on the selected fields, field type, the contents of the active
field, and the sort order you specified.
Note You can also create charts in Layout mode.
The following example describes how to create a chart that counts and compares the number of
customers in each company that has an account with your business.
1. Open the file in which to add the chart, then switch to Table View.
2. Sort the column containing the data to emphasize.
For example, to emphasize your customers’ companies, right-click the Company column and
choose Sort Ascending.
3. Choose the column containing the data to compare.
For example, to compare the number of customers in each company, right-click the Last Name
column and choose Chart
> Chart Last Name by Company.
The Chart Setup dialog box appears with a preview of a column chart that shows the number
of customers in each company.
Area chart Compare data that trends over time while emphasizing highs, lows, and movement
between data points. For example, show sales totals or averages.
Scatter chart Plot x and y coordinates as individual values to reveal correlation patterns. For example,
compare target wait time to actual wait time at a call center.
Bubble chart Compare individual data points in terms of size. For example, compare market share by
charting the number of products sold, sales figures per product, and percentage of total
sales in each data point.
Use To
Chart preview
Specify the chart type
and data series
Specify the records
to chart
The preview updates as
you change settings in the
Chart inspector
Change the chart’s
appearance

Chapter 3 | Designing and creating solutions 83
4. You can choose settings in the Chart inspector on the right to modify the chart, and preview the
result of your changes in the Chart Setup dialog box.
5. Choose Layouts menu > Save Layout, then click Exit Layout in the layout bar.
Editing a chart
1. Choose the layout containing the chart from the Layout pop-up menu.
2. Switch to Layout mode and double-click the chart.
3. In the Chart Setup dialog box, change settings in the Chart inspector.
4. Click Done to close the Chart Setup dialog box.
5. Choose Layouts menu > Save Layout, then click Exit Layout in the layout bar.
To Do this
Add a title to the chart With the Chart options displayed, for Title, type or change
the chart title, or click to specify a title. For example,
“Accounts by Company.”
Choose a chart type and specify the data series For Type, choose a chart type. For example, choose Pie.
Change data labels, show or hide tick marks and
set tick mark scale (if applicable), and format data
Select additional chart options. For example, select Show
Legend, Show values on chart, and Percentages.
Change the color scheme, legend, or fonts in the
chart
Click Styles, then make your changes. For example,
choose Shaded-3D for the chart style, Earth for the color
scheme, and Arial boldface black for the font settings.
Specify the type of data the chart uses (records in
the found set, delimited records, or related records)
Click Data Source, then choose a data source. For
example, choose Current Found Set.
Chart in a layout in Browse mode
Chapter 4
Working with related tables and files
This chapter explains the basics of how to:
1 plan a relational database
1 create and edit relationships
1 create and edit lookups
FileMaker Pro uses related tables as the basis for relational databases and lookups. Relational
databases allow you to work with data from other tables dynamically, so that when you change
data in one place, your changes are reflected in all places where the related data appears.
Lookups let you copy and paste data from one table to another; once looked-up data has been
inserted, it does not change unless you edit it or tell FileMaker
Pro to look it up again.
Use relational databases to:
1 See and work with data from another (or the current) table in its most up-to-date state. For
example, display data in related fields when you need current data from a related table, such
as the current price of an item. As data changes in the related records, you see those changes
in the current table.
1 Set up and manage data efficiently and with flexibility. Instead of creating many database tables
or files with duplicate values, you store single occurrences of values and use relationships to
make those values available. You can then make changes to data in only one place, which
eliminates data duplication and promotes data accuracy.
1 Save disk space, because data is stored in only one place.
Use lookups to copy data from a related table and keep it as copied, even when the related data
changes. For example, use a lookup to copy the price of an item at the time of purchase into an
Invoices table. Even if the price in the related table changes, the price in the Invoices table stays
the same.
FileMaker Pro can also access data stored in other FileMaker Pro files and external ODBC data
sources, which allows you to combine data stored in your FileMaker
Pro file with data from these
external sources. You can work with data in SQL databases that share information through ODBC.
You can also use supplemental fields in FileMaker
Pro to perform calculation and summary
operations on data stored in ODBC data sources. For more information about using FileMaker
Pro
with external data sources, see
“Working with external data sources” on page 108.
For information about solution, see “Planning a solution” on page 37.
Note See Help for detailed, comprehensive information and step-by-step procedures about
using FileMaker
Pro.

Chapter 4 | Working with related tables and files 85
About relationships
A relationship is a powerful method for organizing your data. Using a relationship, you can join
data in one or more tables based on common field values, different field values, or a comparison
of values in two or more fields.
After you create a relationship, you can do either of the following to display the data from the
related table:
1 Design a relational database, which is one or more tables that, when used together, contain all
the data you need for your work. Each occurrence of data is stored in only one table at a time,
but can be accessed and displayed from any related table. You can change any occurrence of
your related data, and the changes appear in all places where that related data is used.
1 Define a lookup to copy data from a related table into a field in the target table. The copied data
is now stored in two places, just as if it were copied and pasted into a target field. Looked up
data is current at the time it is copied, but once copied it remains static unless it is re-looked up
or the lookup is triggered again.
12Customer ID
TangLast Name
12Customer ID
TangLast Name
12Customer ID
TangLast Name
Lookups copy data from the related table into the current table
In relational databases, data from the related table is only
displayed in the current table, not copied
12Customer ID
TangLast Name
Current table Related table
Current table Related table

Chapter 4 | Working with related tables and files 86
For example, a database for a bakery might have these tables: a Products table, which stores
information about bakery products and their current prices; a Customers table, which stores
customer information such as customer names and contact information; an Invoices table, which
keeps a record of each order; and a LineItems table, which stores sales data for each line of the
invoice, including the item being sold and the price at which it is sold. Because invoices are a mix
of dynamic and static data, you use both relational databases and lookups to display your data.
Records from the LineItems table are displayed dynamically, in a portal on the Invoices layout, but
the actual sales price of each line item is entered using a lookup, so the invoice totals remain
historically accurate, even if prices change at some future date.
You create a relational database by defining a relationship between two fields, called match fields.
These fields can be in different tables or they can be in the same table (a self-join). You are able
to access related data when the value in the match field(s) on one side of the relationship
compares successfully with a value in the match field(s) on the other side of the relationship,
according to the criteria you establish in the relationship.
After you have created a relationship, you can use fields from the related table just as you would use
any fields in the current table: to display data on a layout, as part of a calculation formula, in a script,
as a match field for another relationship, and so on. You can work with the data in the related fields
in all modes (if you have access privileges) when you work with records in the current table.
When you display related data in a portal, values from all related records are displayed. When the
related field isn’t in a portal, the value from the first related record is displayed.
Invoices table
003Invoice ID
16-Oct-2012
Date
3
Customer ID
FB7
Unit Price$
Fruitcake $15.50
FB2 Chocolate Cake $22.50
Williams
$38.00Total
Customers table
3
Williams
Last Name
408-555-3456
Phone
Product ID
Product Name
FB7
Fruitcake
FB2
Chocolate Cake
Products table
FB7Product ID
FruitcakeProduct Name
Bakery
ID Location
B20
Ships From
France Paris
B46 Italy Roma
Records from the
LineItems table
displayed in a portal
Customer ID
Last Name
Product ID
Product Name
Chapter 4 | Working with related tables and files 87
Relational database terminology
Before you begin working with relational databases and lookups, you should understand the
following terms. These terms are explained in the sections that follow.
Term Description
Current table For relational databases, the table that you are currently working in.
For lookups, the table that the data is copied to.
External table A table outside of the current file, in another file.
Lookup target field
(for lookups only)
The field in a table that you want data copied to during a lookup.
Lookup source field
(for lookups only)
The field in the related table that contains the data you want copied during a lookup.
Match field A field in the current table and a field in a related table that each contains values used to
access matching records. (A match field is sometimes called a key field.) For each
relationship, you select one or more match fields in each table.
For relational databases, values in match fields must match each other in some way for a
relationship to be established between the files. See
“About match fields for relationships” on
page 88.
For lookups, values in match fields do not have to be equal to match.
Portal A layout object that displays records from related tables. Portals display data from related
fields in rows, one record in each row.
Related field A field in one table that is related to a field in another table (or to a different field within the
same table). If a relationship has been created between two tables (even through another
table), data in fields in one table can be accessed from the other table.
Related record A record in the related table whose match field (according to the relationship used) contains
a value that matches the value in the match field of another table.
Related table For relational databases, the table that contains the data you want to access and work with in
the current table.
For lookups, the table that contains the data to copy.
A table can be related to itself. This is called a self-join.
Relational
operators
In the relationships graph, the symbols that define the match criteria between one or more pairs
of fields in two tables. These include: equal (=), not equal (≠), greater than (>), greater than or
equal to (≥), less than (<), less than or equal to (≤), and all rows, or cartesian product (X).
Relationship Relationships provide access to data from one table to another. Relationships can join one
record in one table to one record in another table, one record to many other records, or all
records in one table to all records in another table, depending on the criteria you specify when
you create the relationship in the relationships graph. (A relationship is sometimes called a
link or a join expression.)
Relationships
graph
In the Relationships tab of the Manage Database dialog box, you can see the occurrences of
tables both in the current file and from any external, related database files. In this relationships
graph, you join tables and change relationships between fields in different tables.
When you create a new table, a visual representation, or occurrence, of the table appears in
the relationships graph. You can specify multiple occurrences (with unique names) of the
same table in order to work with complex relationships in the graph.
Source file The file from which you add a table to the relationships graph.
Source table The table upon which one or more tables in the relationships graph are based. The source
table is the table defined in the Tables tab of the Manage Database dialog box.
Chapter 4 | Working with related tables and files 88
About the relationships graph
When you work with tables in the relationships graph, you organize your view of your data. Tables
shown in the relationships graph can be located in the current FileMaker
Pro file, in an external
FileMaker
Pro file, or in an external ODBC data source.
Each table occurrence in the relationships graph represents a separate view into your data. When
you join two tables, you are leveraging the two existing views to create a third view. As you add
tables to your relationships, each successive table represents an additional set of criteria that must
be met before related data can be accessed in that relationship.
You can create a relationship between any two tables in the relationships graph, but the relationship
must not create a cycle, or closed loop between tables. That is, each series of relationships must
have a starting table and an ending table, and those tables must be different tables.
Because each relationship represents an additional set of criteria, you must be aware of your
context within the relationships graph. Context is the point in the graph from which a relationship
is evaluated. Because the graph is never a cycle, each point along the graph offers a different
perspective into your data.
Because FileMaker Pro does not permit you to create cycles within the relationships graph, any
attempt to create a cycle causes FileMaker
Pro to generate a new, uniquely named table
occurrence. A new occurrence functions like any other occurrence in the graph and allows you to
continue with your new relationship.
About match fields for relationships
When you create a relationship between tables, you choose one or more fields in each table as
match fields. Match fields usually have common values. In a typical relationship, a record in one
table will be related to records in another table that share a common match field value.
For example, a Customers table and an Invoices table can each use the field Customer ID to
uniquely identify each customer and purchase. If the two tables are related using Customer ID as
the match field, a record in the Customers table can display a portal showing each invoice with a
matching Customer ID, and in the Invoices table, each invoice with the same Customer ID can
display consistent customer data.
The match fields used in a relationship can have different names. Match fields can be any field
type except container or summary.
Types of relationships
When you join two tables using a relationship, you establish criteria that FileMaker Pro uses to
display or access related records.
Your criteria can be simple, such as matching a field in Table A with a field in Table B, or more
complex. A more complex relationship definition will usually return a narrower set of related
records. Examples of complex relationships include using multiple match fields on one or both
sides of the relationship, comparing match fields using non-equal relational operators, or using
calculated match fields.

Chapter 4 | Working with related tables and files 89
Single-criteria relationships
In a single-criteria relationship, data in one field is matched to data in another field.
For example, a record in either table is related to any record in the other table when the values
TextFieldA and TextFieldB are the same.
Use a single-criteria relationship to relate two tables based on a single common value, such as a
serial number or an ID number. For example, a database has two tables: Customers, which stores
names and addresses, and Contacts, which stores phone numbers, types of phone numbers
(such as work, home, fax, and so on), and email addresses. The data is split between two tables
because a single customer can have multiple phone numbers and email addresses.
The tables have the following fields:
The Customer ID field is the match field in the relationship between the two tables. In the
Customers table, the Customer ID field is set to auto-enter a serial number, giving each record in
the Customers table a unique ID number. In the Contacts table, the Customer ID is a simple
number field.
Table Field name Comment
Customers Customer ID Number field, auto-enter serial number; this will be the match
field in the Customers table
First Name Text field
Last Name Text field
Address1 Text field
City Text field
State Text field
Country Text field
Contacts Phone Number Text field
Phone Type Text field
Email Address Text field
Email Type Text field
Customer ID Number field; this will be the match field in the Contacts table
Match field
Match field
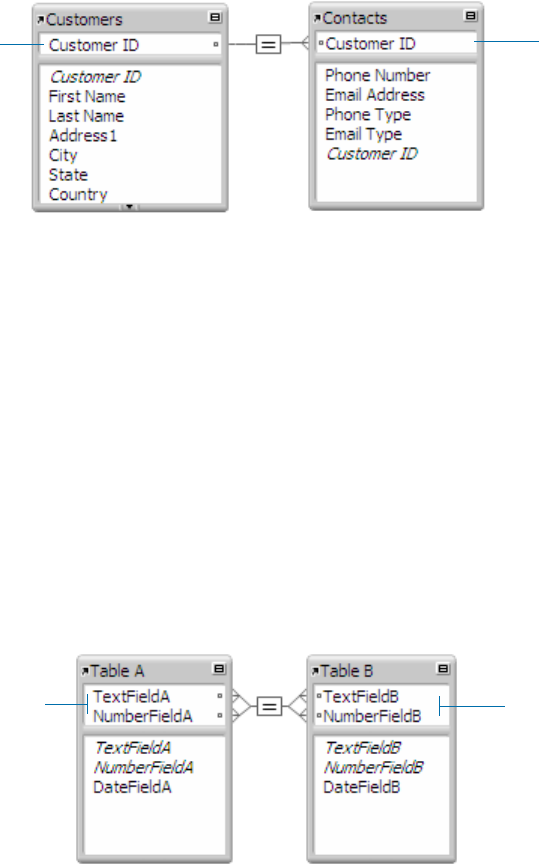
Chapter 4 | Working with related tables and files 90
Because the relationship is defined to allow the creation of related records in the Contacts table,
the Customer ID number from a Customers record will be automatically inserted in the Customer
ID field in the Contacts table in each new related record. This allows many records in the Contacts
table to be related to a single record in the Customers table.
You can then add a portal to the Contacts table on the Customer layout. When you enter a phone
number or an email address in an empty portal row in the Customers table, FileMaker
Pro creates
a related record for that phone number or email address in the Contacts table.
Multi-criteria relationships
In a multi-criteria relationship, you increase the number of match fields, which increases the
criteria that FileMaker
Pro evaluates before successfully joining related records. In a multi-criteria
relationship, FileMaker
Pro compares the values from each match field on each side of the
relationship in the order in which the fields appear. This is called an AND comparison; to match
successfully, every match field must find a corresponding value in the other table.
In this relationship, both TextFieldA and NumberFieldA are match fields to TableB. A record in
TableA with a TextFieldA value of Blue and a NumberFieldA value of 123 will only match those
records in TableB where both TextFieldB and NumberFieldB have values of Blue and 123,
respectively. If TextFieldA and TextFieldB have matching values, but NumberFieldA and
NumberFieldB do not, no related records are returned by the relationship.
Use a multi-criteria relationship to relate two tables based on more than one common value, such
as a customer ID and a date.
For example, a catering equipment rental database has three tables: Equipment, a static table that
stores equipment rental inventory; Customers, which stores customer names and addresses; and
Catering Line Items, which stores a record of each equipment rental, including the equipment ID,
the customer ID, and the event date. The purpose of this database is to track equipment rentals
and display all rentals by a selected customer on a selected date.
Match field
Match field
Match fields
Match fields

Chapter 4 | Working with related tables and files 91
In this relationship, both Customer ID and Event Date are match fields to the Catering Line Items
table. A record in the Customers table with a Customer ID value of 1000 and a Event Date value
of 10/10/2014 will only match those records in the Catering Line Items table where both fields
Customer ID and Event Date have values of 1000 and 10/10/2014, respectively. If Customer ID
fields in both tables have matching values, but Event Date fields in both tables do not, no related
records are returned by the relationship.
Although the database uses three tables, the multi-criteria relationship is between the Customers
and Catering Line Items tables. These tables have the following fields:
Because the relationship is defined to allow the creation of related records in the Catering Line
Items table, you will be able to enter catering information in an empty portal row, and
FileMaker
Pro will automatically create a related record for that catered event.
Relationships using comparative operators
In a comparative relationship, you use one or more of the following operators to compare match
field values in the two related tables. The relationship returns related records when the
comparison evaluates successfully, according to the criteria you establish.
Table Field name Comment
Customers Customer ID Number field, auto-enter serial number; one of the match fields to the
Catering Line Items table
Event Date Date field; the other match field to the Catering Line Items table
Catering Line Items Customer ID Number field; one of the match fields to the Customers table
Event Date Date field; the other match field to the Customers table
Equipment ID Number field
Relational
operator Matches these records
= Values in match fields are equal
≠ Values in match fields are unequal
< Values in the left match field are less than values in the right match field
≤ Values in the left match field are less than or equal to values in the right match field
> Values in the left match field are greater than values in the right match field
Match fields
Match fields
Select to allow creation of related
records in Catering Line Items table

Chapter 4 | Working with related tables and files 92
In this example, the Promotion Date fields in the Sales Promotions table and the Customers table
are match fields. If a record in the Sales Promotions table has a Promotion Date value of
12/11/2014, all the records in the Customers table with a Promotion Date value of 12/10/2014 or
earlier are related to it. In the Customers table, if a record has a Promotion Date value of
12/11/2014, all records in the Sales Promotions table with Promotion Date values of 12/12/2014
or later are related to it.
Relationships that return a range of records
A relationship that returns a range of records is similar to a multi-criteria relationship, except that
you use comparative operators to find records that are greater than one of your criteria and less
than your other criteria. This type of relationship is commonly used to return records that fall
between a range of dates or serial numbers.
For example, from within Table E you want to view all the records in Table F that have Date Field
F values that are greater than Starting Date E values and less than Ending Date E.
This relationship returns those records from Table F that have a Date Field F value that is later
than Starting Date
E and earlier than Ending Date E.
≥ Values in the left match field are greater than or equal to values in the right match field
x All records in the left table are matched to all records in the right table, regardless of the values
in the match fields
Relational
operator Matches these records
Greater than relational operator
Match field
Match field
Indicates that several different
relational operators are used in
this relationship
Match fields
Match field
This relationship uses the
greater than and less than
relational operators

Chapter 4 | Working with related tables and files 93
For example:
Another example:
Self-joining relationships
A self-join is a relationship in which both match fields are defined in the same table. Define a self-
join to create relationships between records in the same table. Use a self-join in a portal on a
layout of the current table to display a subset of data that is in the current table, such as all the
employees of each manager.
When you define a self-joining relationship in the relationships graph, FileMaker Pro generates a
second occurrence of the table upon which you are basing the self-join. FileMaker
Pro does this
to prevent the relationships graph from forming a cycle, which would make it impossible to
evaluate the relationship.
This relationship returns related records in Table G when the value in Text Field G1 is the same
as the value in Text Field G2.
Working with the relationships graph
Use the relationships graph to create, change, and view the relationships in your database file.
The relationships graph lets you duplicate tables and relationships, resize and align tables, and
add text notes. You can highlight tables that are connected to the selected table via a 1-away
relationship, and you can highlight tables that have the same source table as the currently
selected table.
By default, the relationships graph displays all of the tables in your current database file. You can
add tables from other FileMaker
Pro files or external ODBC data sources, add more than one
occurrence of the same table to the graph, or remove tables from the graph using the buttons at
the bottom of the graph.
Note When the table is from an external ODBC data source, the name of the table is typeset in
italics in the relationships graph. To display information about the external data source, move the
pointer over the arrow to the left of the table name.
If fields Contain values These related records are returned from Table F
Starting Date E 11/01/2014 11/14/2014
11/27/2014
Ending Date E 12/01/2014
If fields Contain values These related records are returned from Table F
Starting Date E 12/01/2014 12/02/2014
12/15/2014
12/17/2014
12/26/2014
Ending Date E 01/01/2015
Self-joining relationship
Match field
Match field

Chapter 4 | Working with related tables and files 94
Creating relationships
To create a relationship:
1. With the database open, choose File menu > Manage > Database.
2. In the Manage Database dialog box, click the Relationships tab.
3. In the relationships graph, locate the two tables you will be using for this relationship.
They can appear anywhere on the graph but they must be present on the graph in order to
create the relationship. For self-joining relationships, locate the single table; FileMaker
Pro will
create the second table occurrence for you.
4. Drag a field in one of the tables to the corresponding match field in the other table.
Or, you can click to open the Edit Relationship dialog box and create a relationship.
5. Repeat step 4 for each match field you intend to use in this relationship.
For more information about match fields, see “About match fields for relationships” on page 88.
6. Click OK to save your changes and close the relationships graph.
Changing relationships
After you have created a relationship, you can add or change match fields, change relational
operators, and set options for creating, deleting, and sorting related records.
To change a relationship:
1. With the database open, choose File menu > Manage > Database.
2. In the Manage Database dialog box, click the Relationships tab.
Add a table
Create a relationship
Edit a selected object
Delete selected
objects
Enlarge or reduce the
view of the graph
Change the alignment
of selected objects
Move the pointer to the
arrow icon to display
the names of the
source table and
source file
Click once to collapse all
but the match fields.
Click again to collapse
all but the table name.
Click again to return the
table to its original size
Show page breaks
Display the Print Setup
(Windows) or Page
Setup (OS X) dialog box
Change the color of
selected objects
Add a text note to the
graph
Duplicate selected
objects
Show 1-away tables or tables
with the same source
Click to display or
collapse a text note
Match fields are
shown in
italics in their tables
The relationships graph

Chapter 4 | Working with related tables and files 95
3. In the relationships graph, locate the relationship to edit, and double-click the indicator line
between the related tables to open the Edit Relationship dialog box.
Or, you can select the relationship in the graph and click to open the Edit Relationship dialog
box.
4. Edit tables and match fields for the relationship.
5. Select options for the relationship.
6. Click OK.
To Do this
Change a match field Select the new match field and click Change.
Add a match field Select the new match field and click Add.
Change the relational
operator
Select a new relational operator from the list and click Change.
See “Relationships using comparative operators” on page 91.
Duplicate a pair of
relationship criteria
Select the paired criteria from the list in the middle part of the dialog box and click
Duplicate.
Delete a pair of relationship
criteria
Select the paired criteria from the list in the middle part of the dialog box and click
Delete or click the relationships graph and click Delete.
To Select
Add a related record (to the related table)
whenever you enter data into a related field
in a record of the current table. (See
“Adding and duplicating records” on
page 22.)
Allow creation of related records in this table via this
relationship.
When this option is selected, entering data in a related field that has
no corresponding related record creates a related record based on
the match field in the current table.
Delete matching records (in the related
table) whenever you delete a matching
record in the current table. (See “Deleting
records” on page 24.)
Delete related records in this table when a record is deleted in
the other table.
This option deletes related records even when you’re browsing a
layout that doesn’t display the related records.
Sort related records. Sort records. Then, in the left list in the Sort Records dialog box,
double-click the fields to sort. To change the order in which fields are
sorted, drag fields in the right list into the order you want. Select
other options, then click OK.
Selecting this option does not affect the sort order in the related file.
Select options for the
tables in the relationship
Select the relational
operator

Chapter 4 | Working with related tables and files 96
About lookups
A lookup copies data from another table into a field in the current table. After data is copied, it
becomes part of the current table (and remains in the table from which it was copied). Data copied
to the current table does not change automatically when the data in the other table changes,
unless the data in the match field of the current table changes.
To establish a connection between tables for a lookup, you create a relationship. Then you define
a lookup to copy data from a field in the related table into a field in the current table.
When you type a value in the match field of the current table, FileMaker Pro uses the relationship to
access the first record in the related table whose match field contains a matching value. Next, it
copies the value from the lookup source field into the lookup target field, where the value is stored.
After a value is copied into the lookup target field, you can edit, replace, or delete it like any other
value (because the lookup value belongs to the current table). You can also update data in the
current table to match data that changes in the related table.
Creating lookups
To create a lookup:
1. Create a relationship for the lookup between the match field of the current table and the match
field of the related table. See
“Creating relationships” on page 94.
2. With the database open, choose File menu > Manage > Database.
3. In the Manage Database dialog box, click the Fields tab.
4. If your database contains more than one table, select the appropriate table from the Table list.
5. Select a text, number, date, time, timestamp, or container field from the list of existing fields, or
define a new one.
6. Click Options (or double-click the field name).
7. In the Options for Field dialog box, click the Auto-Enter tab, then select Looked-up value.
8. In the Lookup for Field dialog box, choose the table the lookup will start with, and the table from
which the value will be copied.
9. Select the field from which the lookup value will be copied.
Select To specify
Starting with table The table the lookup will use as its starting point in the relationships graph
Lookup from related table The related table from which the related data will be looked up
C235
Name
42.83.91.04Phone
ParisCity
C100
Name
555-3849Phone
VancouverCity
Current table
C200Customer ID
SmithName
Records in related table
Relationship
Lookup target field Lookup source field
C200Customer ID
SmithName
555-1234Phone
New YorkCity
Customer ID
Customer ID

Chapter 4 | Working with related tables and files 97
10. Select options for the lookup.
11. Click OK.
12. Repeat steps 5–11 for each additional field for which you want to define a lookup.
Editing lookups
To edit a lookup:
1. With the database open, choose File menu > Manage > Database.
2. Click the Fields tab.
3. If your database contains more than one table, select the appropriate table from the Table list.
4. Double-click the lookup target field.
5. In the Options for Field dialog box, click the Auto-Enter tab.
6. Be sure Looked-up value is selected and click Specify.
To stop or suspend using a lookup, clear Looked-up value.
7. Make your changes.
8. Click OK.
To Do this
Specify an action when values in the
match fields do not match exactly
For If no exact match, then, select an option to copy no value, copy
the next lower or next higher value that’s in the lookup source field, or
enter a fixed value to be used instead
Prevent null (empty) data in the lookup
source field from being copied to the
lookup target field
Select Don’t copy contents if empty. (Clear this option to allow empty
data to be copied.)
Select an option for
non-equal data in
match fields
Select the lookup
source field
Select the lookup’s
starting point
When selected, prevents null data
from being copied
Choose the related
table for the lookup
Chapter 5
Sharing data
This chapter explains the basics of how you can share FileMaker Pro databases:
1 FileMaker Network sharing: You can share FileMaker Pro databases on your network, which
allows up to 5 FileMaker
Pro and FileMaker Go users to access and use the same database
file simultaneously. If you want to share a database with more than 5 users, host the database
using FileMaker
Server.
1 Importing and exporting data: You can exchange information between FileMaker Pro and
other applications by importing and exporting data. For example, you can import data that is in
another database or spreadsheet program, or export address data in order to create
personalized form letters with a word processing program.
1 Recurring import: You can set up a FileMaker Pro file to automatically update data imported
from another application, such as Microsoft Excel.
1 Accessing data from external data sources: You can access information stored in other
FileMaker
Pro files and external SQL databases that use ODBC technology to share data. This
allows you to work with information stored in external databases and combine external data with
information stored in your file. When you access data from an ODBC database, you can use
supplemental fields in your FileMaker
Pro file to perform calculations and summary operations
on the data without changing the schema of the external file.
1 Publishing FileMaker Pro layouts: If you have FileMaker Server, you can use
FileMaker
WebDirect to quickly and easily publish layouts from your FileMaker Pro solutions in
a web browser.
Note See Help for detailed, comprehensive information and step-by-step procedures about
using FileMaker
Pro. See FileMaker WebDirect Guide for information about publishing databases
on the web.
Sharing databases on a network
If your computer is connected to a network, you and other Windows and OS X FileMaker Pro and
FileMaker
Go users can use the same database file simultaneously.
FileMaker Pro Network sharing supports the sharing of files with up to 5 concurrent users (not
including the host). FileMaker
Go clients are included in the limit of 5 users. To support more users
and web publishing technologies such as XML, PHP, and FileMaker
WebDirect, use
FileMaker
Server.
Important Your FileMaker Pro licensing agreement requires that you pay for a license for each
separate computer on which the FileMaker
Pro application is installed or run. The software license
may not be shared or used concurrently on different computers. Please read the software license
for complete terms and conditions.

Chapter 5 | Sharing data 99
The first person to open a shared file is the host. Any user who opens a shared file after the host
is a client.
Once a shared file is open, the host and clients have access to the same information, and all
changes to the file appear in each user’s window.
Modifications to the data made by any user are saved in the shared file. The shared file is saved
on the disk where the file resides.
Sort orders, find requests, import and export field orders, and print setups are specific to each user.
Enabling file sharing and hosting files
Because many FileMaker Pro commands are processed on the host machine, you will see better
performance if you host your shared files from the fastest available computer. The file you’re hosting
must be on the hard disk of your computer. Remotely hosting a file stored on another computer or
server is not supported, as it might compromise data integrity and will result in poor performance.
To turn on network file sharing for all open files:
1. Open the FileMaker Pro file(s) to share.
Note To enable or change a file’s sharing status, you must open it with an account that has
Manage Extended Privileges access privileges. For more information, see
“Accounts, privilege
sets, and extended privileges” on page 111.
2. Choose File menu > Sharing > Share with FileMaker Clients.
The host opens the file
Clients open connections to the shared file

Chapter 5 | Sharing data 100
3. In the FileMaker Network Settings dialog box, for Network Sharing, click On.
For TCP/IP Address, you see the TCP/IP address of your system.
4. Select the file(s) to be hosted from the list of Currently open files.
5. Set the level of network access for the file(s).
6. Click OK.
The open files are now hosted.
Important You must keep your shared file(s) open to make them available to clients.
To Select
Provide access to all FileMaker Pro and
FileMaker Go users on your network
All users.
Limit network access to users based on their
privilege set
Specify users by privilege set, then click Specify.
In the “Specify users by privilege set” dialog box, select
privilege sets.
Prevent any access via FileMaker networking No users.
Prevent a shared file from appearing in the Hosts
tab of the Launch Center Window
Don’t display in Launch Center.
Note To access the file through the Launch Center
window, in the Hosts tab, click , then choose Network
File Path.
Click to enable
network sharing
Choose the level of
network access for
the selected file(s)

Chapter 5 | Sharing data 101
Opening shared files as a client
FileMaker Pro databases shared via TCP/IP can be opened remotely using the list of local hosts, the
IP address of the host machine, or the DNS name of the host machine (if one has been defined).
Note You might be required to enter an account name, password, and domain name (Windows
only), depending on how file sharing is configured on the host.
To open a shared file using a local host:
1. Choose File menu > Open Remote.
The Launch Center window opens to the Hosts tab. If hosts aren’t displayed, click .
Favorite hosts appear first in the list.
2. To see the files available from a host, click the host name.
To view files in a list, click . To view files as tiles, click .
3. Select the file you want to open, then click Open (or double-click the filename).
To open a shared file using an IP address or a DNS name:
1. In the Launch Center window, click the Hosts tab, then click and choose Network File
Path.
2. For Network File Path, enter the address and filename of the shared file in this format:
fmnet:/address/filename
For example:
1 an IPv4 address: fmnet:/192.168.10.0/My Addresses
1 an IPv6 address: fmnet:/[2001:0DB8:85A3:08D3:1319:8A2E:0370:7334]/My
Addresses
1 a DNS name: fmnet:/host.domain.com/My Addresses
Note that fmnet:/ uses a single slash.
3. Click OK.
Note When a file you are opening is hosted, you may see an icon that indicates the security level
of the connection to the host. Secure connections are encrypted using SSL.
1 In the title bar of the Open Filename dialog box:
1 (Windows) or (OS X) means the connection is not encrypted.
1 (Windows) or (OS X) means the connection is encrypted, but the SSL certificate for
FileMaker Server cannot be verified. You may be connected to a server pretending to be
your actual destination, which could put your confidential information at risk.
1 (Windows) or (OS X) means the connection is encrypted with a verified SSL
certificate.

Chapter 5 | Sharing data 102
1 After the file is open, in the lower-left corner of the FileMaker Pro window:
1 No icon means the connection is not encrypted.
1 means the connection is encrypted, but the SSL certificate for FileMaker Server cannot
be verified. You may be connected to a server pretending to be your actual destination,
which could put your confidential information at risk.
1 means the connection is encrypted with a verified SSL certificate.
Limitations on changes to shared files
Although it is possible for multiple users to make changes in the same shared file at the same time,
there are limits to the types of simultaneous changes that are permitted. For example, two people
can't edit the same record at the same time, but they can edit different records at the same time.
Opening shared databases remotely using a URL
The FileMaker Pro installer registers FMP as an Internet protocol. This enables you to open a
shared database using a URL. You can also run a script in the shared file using a URL.
To identify the URL for the shared database on the host machine and send it to a client user:
1. In the shared file on the host machine, choose File menu > Send > Link to Database.
FileMaker Pro opens an email message in your default email application that contains the URL
for the current database, plus client connection requirements.
2. Address the email message to the client user, then send the message.
To open a shared database on a client machine:
1. Launch a web browser on the client machine.
2. Enter the URL of the host machine in the address bar using the following format:
fmp://{{account:password@}address/}filename
Optional parameters are indicated by brackets (“{ }”).
Examples
fmp://My%20Addresses
fmp://192.168.10.0/My%20Addresses.fmp12
fmp://[2001:0DB8:85A3:08D3:1319:8A2E:0370:7334]/My%20Addresses.fmp12
fmp://MyAccount:[email protected].0/My%20Addresses.fmp12
Closing a hosted file
Before a shared file can be closed by a host, all clients must close the file. FileMaker Pro allows
you to prompt networked clients to close the shared file when you do one of the following: close
the file, change the sharing conditions for the file, exit FileMaker
Pro, or perform a task that
requires all clients to close the file. If a client does not respond to your request to close a shared
file within 30 seconds, FileMaker
Pro will attempt to close the shared file on the client’s machine.
To close a hosted file:
1. On the computer hosting the file, choose File menu > Close.

Chapter 5 | Sharing data 103
2. If any clients have the shared file open, you see a dialog box listing those clients. Click Ask to
send a message to these clients requesting that they close the file.
Sharing files with FileMaker Go clients
FileMaker Go lets you work with FileMaker Pro files on iPad, iPhone, and iPod touch. You work
with data interactively: when you change data on an iOS device, the data is updated on the host
computer, and vice versa.
Build solutions using FileMaker Pro. Share them using FileMaker Pro or FileMaker Server. Then
use FileMaker
Go to work with the data on a device. To tailor databases for use with FileMaker Go,
see FileMaker
Go Development Guide, available at http://www.filemaker.com/documentation.
Uploading files to FileMaker Server
You can use FileMaker Pro to transfer database files to FileMaker Server. Before you can upload
files, you must have the account name and password for the server administrator or for a group
administrator that has the privilege to perform actions on databases. For more information about
uploading files to FileMaker
Server, see Help.
Importing and exporting data
You can exchange information between FileMaker Pro and other applications by importing and
exporting data. You can:
1 import data into an existing FileMaker Pro file, either into a new table or into an existing table
1 convert data from other applications to new FileMaker Pro files
1 export data for use in other applications
Supported import/export file formats
Every application stores its data files in its own file type or file format. Most applications can also
exchange information in certain other formats.
FileMaker Pro can import and/or export files in these formats, followed by their filename
extensions: Microsoft Excel (.xlsx), tab-separated text (.tab, .txt), comma-separated values (.csv,
.txt), FileMaker
Pro 12 (.fmp12), Merge (.mer), HTML table (.htm), and XML (.xml). If you’re
exchanging data with another program, check the documentation that came with that program to
determine a common intermediary file format that both FileMaker
Pro and the other program
support.
Most file formats support data conversion only and do not import or export formatting such as font,
size, style, and color.
Setting up recurring imports
You can set up a FileMaker Pro file to automatically update data imported from another
application, such as Microsoft Excel. A recurring import occurs automatically the first time you view
the layout containing the data from the external file. Later, you can run a script to update data.
If FileMaker Pro
Clients click Cancel Waits for those clients to close the file
Clients click Close Now Closes the shared file on the client’s computer
Clients do nothing Attempts to close the file after 30 seconds, if it can be closed safely

Chapter 5 | Sharing data 104
ODBC and JDBC
You can exchange FileMaker Pro data with ODBC- and JDBC-compliant applications. For
example, you can chart FileMaker
Pro data in Microsoft Excel.
Methods of importing data into an existing file
When you import data into an existing file, you can:
1 add new records to an existing table
1 create a new table from imported data
1 update existing records in an existing table
1 update matching records in an existing table
Important The import options that update existing records and update matching records both
overwrite existing data during the import process and cannot be undone. To safeguard your data,
choose File menu
> Save a Copy As to make a backup of the file before you perform an import
that updates records.
The file you import records from is the source. The file you import records to is the target.
About adding records
When you add records, you import all records from the source file to the target file or table. A new
record is created in the target file for each importable record in the source file.
About updating existing records
With this option, you replace data in your file with data from the source file. For each field you
import into, data from the first importable record (or row of data) in the source file overwrites fields
in the first record in the target file. Data from the second importable record (or row of data) in the
source file overwrites fields in the second record in the target file, and so on. When you replace
data, FileMaker
Pro doesn’t examine or compare the data in the files.
You can choose whether to replace or not replace data on a field-by-field basis.
Records in the target file are replaced with the same number of records from the source file. If
there are more importable records in the source file, data from the extra records in the source file
will not be imported unless you also choose Add remaining data as new records. If there are
more records in the target file, data in the extra records in the target file will not be replaced.
What do you want to do? How do you do it? See
Use FileMaker Pro as a data
source/share FileMaker
Pro data
1. ODBC and JDBC
2. SQL queries
FileMaker ODBC and JDBC
Guide and FileMaker SQL
Reference
Use FileMaker Pro as an ODBC
client/access ODBC data
1. Interactively via the relationships graph
2. One-time, static via ODBC import (or
File menu > Open), also Import Records
script step, Execute SQL script step
“Working with external data
sources” on page 108 and Help

Chapter 5 | Sharing data 105
About updating matching records
You can update matching records and fields in your target file with data from another file. For
example, you might have a copy of a database on your desktop computer and another copy on your
laptop computer. You can update the file in your office with the changes you make on the road.
You determine which records in the source file update which records in the target file by choosing
one or more match fields in each file. If data in the match field(s) of a record in the target file
matches data in the match field(s) of a record in the source file, the record in the target file will be
updated with data from the source file.
Match fields must uniquely identify each entity in your database. For example, in a database of
people, you could use one match field such as Employee Number, or multiple match fields such
as Last Name, First Name, and Phone Number. Using Last Name alone might identify more
than one person, so it isn’t a good match field to use by itself.
You also specify the fields to import. The contents of all fields you select to import, in all matching
records, will overwrite data in the target file, even if the field in the source file is blank.
When the target file contains a found set, only the found records are updated. (If the source file is
another FileMaker
Pro file, you can also import only from a found set.)
The following example shows how a record in a target file appears before and after being updated
by a matching record in a source file.
About the importing process
The basic steps for importing records are:
1. Make a backup copy of the target file you’re importing into.
2. If the source file is a FileMaker Pro file, perform a find so that the found set in the current window
contains only the records to import.
3. Open the target file, and if it has multiple tables, select a layout that shows records from the
table to import data into.
The layout doesn’t have to display all the fields in the table. You will be able to specify the fields
to import to in the Import Field Mapping dialog box.
4. If you’re updating existing or matching records, make sure the found set in the target file
contains only the records to change or update.
(OS X) or –> (Windows) indicates to import the field
–>
–
–>
–>
–>
–
–>
–
(OS X) or = (Windows) indicates a match field
123-456-7890
Source file
John
Q
Smith
456 New Rd.
Newtown
USA
123-456-7890
Target file
John
Smith
123 Main St.
Anytown
USA
3/3/2015
408-555-6789
123-456-7890
After updating
John
Q
Smith
456 New Rd.
Newtown
USA
3/3/2015
Before updating matching records
Target file
=
(OS X) or – (Windows) indicates not to import the field

Chapter 5 | Sharing data 106
5. Choose File menu > Import Records > File, and choose the name of the file that contains the
data to import (the source file).
6. In the Import Field Mapping dialog box, if necessary, select a table from the Source list.
7. Accept the table shown in the Target list, or select New Table to create a table with the same
schema as the source table.
8. Select the type of import to perform. See “Methods of importing data into an existing file” on
page 104.
9. Map the fields in the source file to the fields in the target file, and select an import option.
10. Click Import.
11. If the Import Options dialog box appears, choose one or more of the following options, then
click Import.
You can:
1 auto-enter data in fields defined with auto-enter options
1 specify how to import data from repeating fields
1 allow the target file to use existing external container field contents rather than import new
container data
Converting a data file to a new FileMaker Pro file
You can convert a data file from another application into a new FileMaker Pro file. The converted
file will contain:
1 The data from the file or source you convert
1 Two layouts for displaying the data
Fields in the
source file
Fields in the
target file
Arrows show that data will
import into the fields at right
Select an import action
Select a table to
import from
Import to the current
table or a new table

Chapter 5 | Sharing data 107
1 Converted field names if they are available in the file or source you convert. Otherwise, field
names are generic: f1, f2, f3, and so on.
1 Converted field types if they are available in the file or source you convert. Otherwise, all fields
are text fields.
To import data into a new file:
1. In the source application, save the data to import in a file type that FileMaker Pro supports. See
“Supported import/export file formats” on page 103.
2. In FileMaker Pro, choose File menu > Open.
3. In the My Solutions tab in the Launch Center window, click Browse.
4. In the Open File dialog box, for Files of type (Windows) or Show (OS X), specify the type of
file, choose the file to convert, then click Open.
5. If you see the First Row Option dialog box, choose whether the first row of data contains field
names or the first record of data, then click OK.
6. If you’re converting a Microsoft Excel spreadsheet and the Specify Excel Data dialog box
appears, choose a worksheet or named range from the workbook file, then click OK.
7. In the New File dialog box, type a name for the new file, choose a location, then click Save.
FileMaker Pro converts the data to a FileMaker Pro file and displays the file.
About the exporting process
You can export FileMaker Pro data to a new file, then open it in another application.
The basic steps for exporting records are:
1. Open the FileMaker Pro file and display a layout that shows the records to export.
2. Find and sort the records to export. See “Finding records” on page 28 and “Sorting records” on
page 32.
3. Choose File menu > Export Records.
4. In the Export Records to File dialog box, type a name and choose a location for the exported
file, and choose a file type.
5. In the Specify Field Order for Export dialog box, select how to export the data.
6. If necessary, choose a character set for the exported file to use.
To export Choose
A field on the current layout Current Layout (LayoutName) from the table list, then double-click a field in
the list
A field in the current layout’s
table
Current Table (TableName) from the table list, then double-click a field in the list

Chapter 5 | Sharing data 108
7. Select whether or not to apply the current layout’s formatting to the exported data.
Working with external data sources
You can define data sources in a FileMaker Pro file to access data from:
1 other FileMaker Pro files
1 SQL databases that use ODBC technology for sharing information
When you define data sources in FileMaker Pro files, current data from external databases is displayed
in your files. You can use FileMaker
Pro to add, edit, delete, search, and sort data in the external files.
The following procedures provide an overview of how to access data in external FileMaker Pro
files or external ODBC data sources.
Working with external FileMaker Pro files
To set up a file to access data from another FileMaker Pro file:
1 Add tables from other FileMaker Pro data sources to the relationships graph in the current
FileMaker
Pro file.
1 Add fields to layouts to display data from the other FileMaker Pro file.
Working with ODBC data sources
To set up a file to access data in supported ODBC data sources:
1 Install and configure an ODBC driver for the external data sources you want to access.
1 On the computer that hosts the current FileMaker Pro file, define a system Data Source Name
(DSN) for each ODBC data source you want to access.
1 Set options for the ODBC data sources you want to access (for example, whether users are
prompted for a user name and password).
1 Add one or more tables from the ODBC data source to the relationships graph in the current
FileMaker
Pro file.
1 Add fields to layouts in the FileMaker Pro file to display external data.
1 Optionally, add supplemental fields to external tables and layouts to display calculation and
summary results based on data stored in external ODBC data sources.
Select fields
from this list
Select to apply formatting
FileMaker Pro exports
these fields
To export related fields, select
the related table from the list
Chapter 5 | Sharing data 109
Saving and sending data in other formats
You can save FileMaker Pro data as a Microsoft Excel worksheet or a PDF file, allowing you to
give your record data to users who don’t have FileMaker
Pro.
FileMaker Pro lets you email the Excel worksheet or PDF file when you save it. You can also
create scripts to save records as Excel or PDF.
In order to save files as Excel, you need the Allow Exporting Access privilege. To save files as PDF,
you need the Allow Printing Access privilege.
Note The saved file will only include fields that are on the layout when you perform the save. To
include other fields (for example, fields on tab panels that are not in front), use the Export
Records command instead of Save/Send Records As.
Sending email messages based on record data
You can use FileMaker Pro to send one message, or multiple messages, to one or more
recipients. Generated email is sent using your default email application or directly through SMTP
(Simple Mail Transfer Protocol, a set of criteria for sending and receiving email). You can enter
values, or use values from fields or calculations. You can also create scripts to send email.
Publishing solutions on the web
If you have FileMaker Server, you can use FileMaker WebDirect to quickly and easily publish
layouts from your solutions on the web. You don’t need to install additional software—anyone with
compatible web browser software and access to the Internet or an intranet can connect to your
FileMaker
WebDirect solution to view, edit, sort, or search records, if you give them access
privileges. With FileMaker
WebDirect, data in the web browser updates automatically as
FileMaker
Server pushes data to the web browser.
For more information, see FileMaker WebDirect Guide.

Chapter 6
Protecting files
This chapter describes the basics of how to restrict what users can see and do in a FileMaker Pro
file. You’ll learn about:
1 planning security for a file
1 viewing and creating user accounts and passwords
1 viewing and creating privilege sets
1 viewing extended privileges
1 authorizing other files to access your files
1 taking measures to secure your database solution, and your operating system, network, and
hardware
1 backing up databases and other files
1 installing, running, and upgrading antivirus software
Note See Help for detailed, comprehensive information and step-by-step procedures about
using FileMaker
Pro.
For comprehensive information about securing FileMaker Pro files, see
http://www.filemaker.com/support/security.
Protecting databases with accounts and privilege sets
You can limit what users can see and do in a database file. You can restrict:
1 Data access: Make particular records or fields from individual tables view-only, or hide them
completely.
1 Layout access: Prevent users from modifying layouts in Layout mode.
1 Access to value lists and scripts: Prevent users from accessing and modifying value lists and
scripts, and from running scripts.
1 Access to file sharing: Individually enable file sharing via the FileMaker Network, ODBC and
JDBC, and FileMaker
WebDirect.
1 Outputting data: Prevent users from printing or exporting data.
1 Menu access: Make only a limited set of menu commands available.
You restrict what users do in a file by requiring them to enter an account name and password when
they attempt to open a file. The account name they enter determines which privilege set will be
used and the privilege set limits what they can do in a file. For more information about accounts
and privilege sets, see the following section.
You can define privileges in a shared file while clients are using it. Any privilege changes that affect
a current client do not take effect until the client closes and reopens the file.
Chapter 6 | Protecting files 111
The privileges that you set up apply to a single file only and all database tables within that file. If
your database solution consists of multiple files that you want to protect, you may want to combine
all of these files into one multi-table file. Then you can define privileges in only a single file to
manage access to the entire database solution. If you don’t want to combine the files into one file,
then you should define privileges in each file that contains items to protect.
Important If you create a relationship in one file that references a table in another file, you cannot
manage access privileges for the related table in the first file. The privileges defined in the other
file control access to that table.
Accounts, privilege sets, and extended privileges
Accounts
Accounts authenticate users who are attempting to open a protected file. Each account specifies
an account name and usually a password. Any user who cannot specify valid account information
won’t be able to open a protected file.
Each database file contains two predefined accounts: Admin and Guest. For more information,
see
“About the predefined accounts” on page 112.
You may want to create an account for every individual who accesses a file, or you may want to
create a small number of accounts that are shared among many individuals, such as a “Marketing”
account and a “Sales” account.
1 Create accounts for individuals when it is necessary to verify the identities of particular users
and you want to manage access at an individual level.
1 Create shared accounts when you want fewer accounts to maintain and you are less concerned
about managing individual access to the file.
If you host files on FileMaker Server, you can create External Server accounts that obtain
authentication information from an authentication server such as an Apple Open Directory or a
Windows domain. For more information, see
“Creating accounts that authenticate via an
external server” on page 118.
Privilege sets
A privilege set specifies a level of access to a database file. Each database file contains three
predefined privilege sets for common types of access levels: Full Access, Data Entry Only, and
Read-Only Access. When you create a privilege set, there are many options available that you
can use to limit database access, such as which layouts are viewable, which menus are available,
and whether printing is permitted. Privilege sets can also restrict access to records or fields from
particular tables within a file. Each account is assigned a privilege set, which determines the level
of access when someone opens a file using that account.
You can create as many privilege sets as you need to define the types of access you want to permit
to a file. For more information about privilege sets, see
“About the predefined privilege sets” on
page 113.
Extended privileges
Extended privileges determine the data sharing options that are permitted by a privilege set, such
as whether a privilege set permits users to open a shared file or view a database in a web browser.

Chapter 6 | Protecting files 112
The following table lists the default extended privileges that are available. (FileMaker and third-
party developers may define additional extended privileges to manage access for other software
products designed to work with FileMaker
Pro or FileMaker Server.)
When a user attempts to open or access a protected file using one of the above methods, he or
she will be prompted to provide account information. If the privilege set for the account does not
permit the type of extended privilege access the user is requesting, the user will get an error
indicating that he or she cannot access the file.
All extended privileges except fmreauthenticate10 are disabled by default, even in the Full Access
privilege set.
Enabling extended privileges only makes it allowable for certain privilege sets to access shared
data. To actually access the shared data, you must also set up sharing for the type of access that
you want. For more information on extended privileges, see
“Viewing extended privileges” on
page 120.
About the predefined accounts
Each database file contains two predefined accounts: Admin and Guest.
Admin account
The Admin account is assigned the Full Access privilege set, which permits access to everything
in a file. The Admin account is not assigned a password. In files for which privileges are not set
up, the file options are set up to automatically log in to the file using the Admin account.
The Admin account is fully editable. You can rename it, assign it a password, or make the account
inactive. You can even delete the Admin account; however, you must assign the Full Access
privilege set to at least one other active account.
Important Don’t forget the account name and password that is assigned to the Full Access
privilege set. If necessary, write it down and store it in a secure place. If you lose or forget this
account name and password, you may not be able to access the file.
Keyword Extended privilege Determines if a privilege permits
fmwebdirect Access via
FileMaker
WebDirect
Accessing a database file from a web browser via
FileMaker
WebDirect.
fmxdbc Access via ODBC/JDBC Accessing a database as an ODBC or JDBC data source.
fmapp Access via FileMaker Network,
server-side scripting, or
FileMaker
Go
Opening a shared file (either a file shared by FileMaker Pro
or hosted and shared by FileMaker Server).
fmreauthenticate10 Require re-authentication after
the specified minutes in
sleep/background
Accessing a file in FileMaker Pro or FileMaker Go without
having to re-login after file hibernation or after using a
different app. The default time is 10 minutes.
fmxml Access via XML Web
Publishing - FMS only
Accessing a database file from a web browser or other
application via XML web publishing (FileMaker Server only).
fmphp Access via PHP Web
Publishing - FMS only
Accessing a database file from a web browser or other
application via PHP web publishing (FileMaker Server only).
Chapter 6 | Protecting files 113
Guest account
The Guest account permits users to open a file without specifying any account information. The
Guest account is not assigned a password. By default, the Guest account is assigned the Read-
Only Access privilege set, but you can assign any privilege set to the Guest account.
Initially, the Guest account is inactive, which disables the guest option in the Open <filename>
dialog box and prohibits users from opening files as a guest. You can enable the Guest account
to permit guest access.
The Guest account is not fully editable. You cannot delete the Guest account, change the Guest
account name, or assign it a password.
About the predefined privilege sets
Every new database file contains three predefined privilege sets.
1 Full Access: permits accessing and changing everything in the file
1 Data Entry Only: permits viewing and entering of data only
1 Read-Only Access: permits viewing but not changing data
Note The Read-Only Access privilege set permits write access to all global fields. To create a
privilege set in which global fields and all record data are view-only, you can duplicate the Read-
Only Access privilege set and change Records from Custom privileges to View only in all
tables.
You cannot change or delete these predefined privilege sets, except to enable or disable extended
privileges for them. You can either use them as is, or duplicate them and then modify the duplicate
copies.

Chapter 6 | Protecting files 114
The following table summarizes the properties of these privilege sets.
You must have Allow Printing privileges to save records as a PDF file. You must have Allow
Exporting privileges to export records as a Microsoft Excel worksheet. See
“Saving and sending
data in other formats” on page 109.
Note The Full Access privilege set is the only one that permits access to the Manage Database
and Manage External Data Sources dialog boxes in order to modify fields, tables, relationships,
and data sources. It is also the only privilege set that permits changing accounts and privileges.
Because you cannot enable these privileges in any other privilege set, any user who wants to
make database definition changes or privileges changes must open the file with an account that
is assigned the Full Access privilege set.
At least one active, FileMaker authenticated account in each file must be assigned the Full Access
privilege set.
Planning security for a file
A new FileMaker Pro file is initially unprotected. Whenever the file opens, it automatically logs in
the user with the Admin account, which is assigned the Full Access privilege set.
1 If you simply want to keep someone else from opening a database file on your computer, you
can password-protect the file. For more information, see
“Password-protecting a file” on
page 116.
Privilege
Full Access
privilege set
Data Entry Only
privilege set
Read-Only
Access
privilege set
Records (in all tables) create, edit, delete create, edit, delete view only
Layouts all modifiable view only view only
Value lists all modifiable view only view only
Scripts all modifiable and
executable
all executable only all executable only
Extended Privileges all off, except
fmreauthenticate10
all off, except
fmreauthenticate10
all off, except
fmreauthenticate10
Allow printing on on on
Allow exporting on on on
Manage extended privileges on off off
Override data validation warnings on off off
Disconnect user from FileMaker Server
when idle
off on on
Allow password modification on on on
Password change number of days off off off
Minimum password length off off off
Available menu commands All All All

Chapter 6 | Protecting files 115
1 If you need to share a database file with others and provide varying levels of file access to
different users, you need to plan the security for the file. Consider listing the types of users and
their privileges:
* You can provide limited access to some features, for example deleting records, by using record-
by-record privileges.
You can additionally protect a file by requiring authorization of any file that attempts to access its
tables, layouts, value lists, and scripts. See
“Authorizing access to files” on page 120.
To plan the security for a shared file:
1. Determine the privilege sets that you need for the file.
Make a list of the areas of the file to protect, such as particular tables, fields, records, layouts,
value lists, and scripts. Plan the number of privilege sets you need to enforce the varying levels
of file access that you require.
2. Determine whether you need individual accounts for each user, or group accounts that multiple
users can share.
3. Decide if you want to enable the Guest account, which permits users to open the file without
specifying account information.
4. Create the privilege sets that you need in the file.
5. Determine if you need to enable any extended privileges for specific privilege sets.
Don’t enable extended privileges unless they’re needed.
6. Create the accounts you need in the file, and assign the appropriate privilege set to each account.
For information, see the next section. If you’re using the Guest account, assign a privilege set
to it. Otherwise, disable the Guest account.
7. Open the file using different accounts and test each privilege set that you created. Make sure
the restrictions work the way you want, and make any needed corrections to your privilege sets.
8. Optionally, limit other files from accessing the solution’s schema. For more information, see
“Authorizing access to files” on page 120.
Managers Marketing Sales HR Legal Guests
View records
Yes Yes Yes Yes Yes Yes
Create records
Yes Yes Yes Yes No No
Edit records
Yes Yes Yes Yes No No
Delete records
Yes Limited* Limited* Yes No No
Modify scripts
Yes Limited* No Yes No No
Execute scripts
Yes Yes Yes Yes Yes No
Modify value lists
Yes No No No No No
Menus
All Editing only Editing only All Minimum Minimum
Chapter 6 | Protecting files 116
Password-protecting a file
After password-protecting a file, you will be prompted to enter an account name and password
every time you open the file. Anyone who does not know this account information will not be able
to open the file.
To password-protect a file:
1. Make the following changes to the accounts in the file:
1 Edit the Admin account so that it has a different account name, a password, and uses the
Full Access privilege set.
1 Make sure the Guest account is inactive.
1 Delete any other accounts in the file or make them inactive.
2. If necessary, edit the Full Access privilege set to allow yourself any extended privileges you may
want for yourself.
Don’t enable extended privileges unless they’re needed.
Suggestions for creating secure passwords
1 Secure passwords are typically eight or more characters in length, and include at least one
numeric character.
1 Passwords are case-sensitive. For example, if you specify a password as zFootBallz2,
FileMaker Pro will not accept zfootballz2. When you’re entering a password for an account,
make sure the Caps Lock key on your keyboard is not inadvertently enabled.
1 If the file is shared via web publishing, account names and passwords can only use characters
included in the ISO Latin-1 character set (except colons). To avoid characters that may be
interpreted incorrectly over the web, limit account names and passwords to alphabetic and
numeric characters only.
Creating accounts and privilege sets
Accounts specify account names and (usually) passwords for a file. When a user opens a file that
contains accounts, a dialog box prompts the user to enter account information. When a user opens
a file with a correct account name and password, the privilege set assigned to that account
determines what the user can do in that file.
Privilege sets specify levels of access to a database, such as which layouts are viewable, which
menus are available, and whether printing is permitted.
To create and manage accounts and privilege sets for a file, you need to open the file with an
account that is assigned the Full Access privilege set. In addition, to make changes to an account
that’s assigned the Full Access privilege set (for example, deleting the account or assigning Full
Access privileges to it), you need to use a local account that’s assigned Full Access privileges.
You can create and modify accounts and privilege sets in a shared file while clients are using it.
The account changes you make take effect immediately. However, the changes do not disrupt any
current clients. For example, if you change the password for an account that is in use by one or
more clients, their FileMaker
Pro usage is not interrupted. However, they will need to enter the new
password the next time they open the file.
You can create as many accounts as you need. You can create individual accounts for each user,
or a smaller number of accounts that users can share.

Chapter 6 | Protecting files 117
Viewing accounts
1. With the file open, choose File menu > Manage > Security.
The Manage Security dialog box appears. If the detailed security settings are displayed, click
Use Basic Setup.
2. You see the accounts defined for this file on the left.
3. Click OK.
Creating and editing accounts
You can create accounts for every individual who accesses a file, or create fewer accounts that
are shared among many individuals, such as a “Marketing” account and a “Sales” account. You
must assign a privilege set to each new account.
To create or edit an account:
1. With the file open, choose File menu > Manage > Security.
2. If the Manage Security dialog box displays the detailed settings, click Use Basic Setup.
3. To create a new account, click New Account. To change an existing account, select the
account.
4. For Authenticate via, choose Local FileMaker File.
To authenticate the account via an external server, choose External Server.
Accounts defined
for the file
Select to make
the account
active
Choose how to
authenticate the
account
Add, duplicate, or
delete an account
Enter account
and password
information
Change
privileges for the
account

Chapter 6 | Protecting files 118
5. For Account Name, enter or change the account name.
Account names are not case-sensitive.
6. To define or change the password, for Password, click Change. Then, enter and confirm the
new password, and click Set Password.
7. To force the account user to create a new password during the next login, select Require
password change on next login.
8. For Privilege Set, do one of the following:
1 Choose a privilege set.
1 Choose New Privilege Set, then create a new one.
1 Chose a privilege set, then click Edit and change the privilege set.
9. To make the account active, select its checkbox.
To make an account inactive (for example, until you set up its privilege set), clear the checkbox.
10. Click OK.
To duplicate or delete an existing account:
1. Follow steps 1 and 2 in “Creating and editing accounts,” above.
2. In the Manage Security dialog box, select an account, then:
1 To duplicate the account, click .
1 To delete the account, click .
3. Click OK.
Creating accounts that authenticate via an external server
If you’re hosting FileMaker Pro database files with FileMaker Server and your organization uses
centrally managed authentication for users and groups such as Apple Open Directory or a
Windows domain, you can set up accounts that authenticate users based on your authentication
server. This allows you to use your existing authentication server to control access to databases
without having to manage an independent list of accounts in each FileMaker
Pro database file.
Note Only database files hosted by FileMaker Server can authenticate users against an
authentication server. Database files shared by FileMaker
Pro won’t authenticate against an
authentication server.
Important When a database file contains one or more External Server accounts, make sure you
use operating system security settings to limit direct access to the file. Otherwise, it might be
possible for an unauthorized user to move the file to another system that replicates your
authentication server environment and gain access to the file. For more information, see
FileMaker
Server Help.
Creating and editing privilege sets
You can assign each privilege set to one or more accounts.

Chapter 6 | Protecting files 119
To create a privilege set:
1. With the file open, choose File menu > Manage > Security.
If the Manage Security dialog box displays the basic security settings, click Use Detailed
Setup.
2. Click the Privilege Sets tab.
By default, each privilege set option is set to its most restrictive setting.
3. To create a new privilege set, click New. To edit an existing privilege set, select the privilege
set to edit, then click Edit.
4. Enter or change the name and optional description for the privilege set.
5. Define the privileges for the privilege set.
Privilege sets that you can’t change are dimmed.
6. Click OK.
After you create the privilege sets, create or edit accounts so that they use the appropriate
privilege sets. See
“Creating and editing accounts” on page 117.
About enabling record-level access
You can set individual record access for each table. For example, the privilege set can limit the
ability to:
1 View, edit, create, or delete all or certain records within each table.
1 Access or modify certain fields within each table.
You can only set record access privileges for tables defined in the current file. If the file contains
relationships to tables in other files that you want to protect, you need to create accounts and
privilege sets in the other files to protect those tables.
Click to create a new
privilege set
Chapter 6 | Protecting files 120
Viewing extended privileges
Extended privileges determine the data sharing options that are permitted by a privilege set for a
file. For example, if the file is shared, the Access via FileMaker Network extended privilege
determines if the privilege set allows opening the shared file as a client. The Access via
FileMaker
WebDirect extended privilege determines whether the privilege set allows accessing
the database from a web browser.
There are six default extended privileges. For more information about them, see “Accounts,
privilege sets, and extended privileges” on page 111.
You can view extended privileges in the Manage Security dialog box, as well as enable each
extended privilege for selected privilege sets. All extended privileges except fmreauthenticate10
are disabled by default, even in the Full Access privilege set.
It may be necessary to delete an extended privilege that is no longer required.
To view the extended privileges:
1. With the file open, choose File menu > Manage > Security.
If the Manage Security dialog box displays the basic security settings, click Use Detailed
Setup.
2. In the Manage Security dialog box, click the Extended Privileges tab.
Authorizing access to files
As part of your overall security plan, you can control whether other FileMaker Pro files are
permitted to access the schema in a file (including its tables, layouts, scripts, and value lists) in
your secured solution. When protection is enabled, any use of the protected file through a
FileMaker data source will require authorization. Therefore, in a multi-file solution, you will need
to authorize the other files.
For example, enabling protection prevents someone with an account in your file from creating
another file that uses tables in your file but does not implement the same business logic (such as
the same script triggers). The use of this alternative file can bypass your intended business logic
(although record-level access would still be enforced). Turning on this option also prevents files
that are not authorized from opening a protected file using the Open File script step.
Note You must have the Full Access privilege set for any file that you want to protect and any file
that you want to authorize.
To authorize access to a file:
1. With the file open, choose File menu > Manage > Security.
If the Manage Security dialog box displays the basic security settings, click Use Detailed
Setup.
2. Click the File Access tab.
3. To protect this file against unwanted access from other files, select Require full access
privileges to create references to this file.
4. If any files that reference the protected file are currently open. When you see an alert, click Yes.
Chapter 6 | Protecting files 121
5. To authorize additional files that are not currently open, click Authorize. In the Open File dialog
box, choose a local or remote file to authorize, and click Open.
You may be asked to enter the name and password of an account with Full Access privileges.
6. Click OK.
Security measures
Be sure that your database files, host computers, workstations, and the networks that access
them are safe from theft and corruption. To protect your data and equipment, you should
implement the following five important security measures:
1 Enhance physical security
1 Enhance operating system security
1 Establish network security
1 Back up databases and other important files
1 Install, run, and upgrade antivirus software
Enhancing physical security
Evaluate your computers to make sure they are physically secure:
1 The host computer should be a dedicated machine, anchored to a desk or immovable object
with a lock. Secure the computer so that its hard drive cannot be removed. Restrict access to
the computer by storing it in a locked room.
1 Secure the client workstations that access a database. Lock the computers down and restrict
access by using a screensaver that requires a password.
1 Protect the physical security of the computers, hard drives, and backup storage media where
the files reside.
Enhancing operating system security
Use the security features of your operating system to restrict access to important data. The
network administrator should provide access only to individuals authorized to administer and
maintain the system or the FileMaker files. In addition, they should:
1 Track system user IDs and passwords.
1 Restrict access to the FileMaker Pro application and file directories, servers, and web pages.
1 Review remote access settings for file sharing and FTP.
1 Restrict file upload or download access.
1 Make sure all users have the latest, most secure versions of operating system software.
1 To streamline processes, you can enable external authentication, which uses accounts that
have been configured in the Windows Domain Authentication or in Apple Open Directory.
1 Do not put FileMaker Pro files on file servers to share them. Use the built-in networking feature
in FileMaker
Pro and FileMaker Server. This prevents the files from being inappropriately
copied or from introducing record locking and potential corruption issues when files are shared
with inappropriate methods.
Chapter 6 | Protecting files 122
Establishing network security
Databases shared on an intranet or the Internet use the TCP/IP protocol. You may also use the
TCP/IP protocol when you share databases peer-to-peer, or with FileMaker
Server. Though
TCP/IP is good for moving data and allowing clients to connect to your data, it was not designed
with security as a primary objective. Unless you take precautions, it can provide uninvited access
to your host computer, server software, databases, and perhaps to other client machines on your
internal network. TCP/IP doesn't provide very much protection for data, so it is important to place
barricades such as firewalls and SSL data encryption in the path of uninvited visitors.
1 The most common barricade method used is the firewall, which separates your network into two
distinct environments: a public environment that is “outside the firewall,” and a private
environment that is “behind the firewall.” Users outside of the firewall will only have access to
those TCP/IP or hardware addresses that you expose. You can concentrate your security on
those server machines that are exposed, while allowing machines behind the firewall to operate
with fewer safeguards.
1 Using wireless networking devices, like the Apple AirPort Extreme and other 802.11n networking
cards and base stations, can pose security challenges. These devices can broadcast your
network traffic beyond the walls of your building, so it is extremely important to encrypt your
wireless networking signals. Always use the maximum level of signal encryption available.
Backing up databases and other important files
Develop plans for restoring data, including alternate sites and systems to run business-critical
information services. A current backup can help you recover from a situation where someone
loses the administrator account information for a file, or from a situation where user error (and
sometimes bad database design) causes data to be deleted or modified inappropriately.
Keep the following points in mind:
1 Host databases with FileMaker Server and create regularly-scheduled, automated backups.
Don’t use third-party backup software on hosted FileMaker Pro databases. First, use
FileMaker
Server to make a backup copy of your database, then run your third-party backup
software on the copy. Backup software can damage open, hosted databases.
For example, make local backups of files at 6:00 am, 9:00 am, 12:00 noon, 3:00 pm, 6:00 pm,
and 11:30 pm weekdays. At midnight, make an incremental backup of the entire system to the
enterprise backup system. Finally, Friday night at midnight, perform a full system backup. Copy
and store the backup tapes at a remote location. This way, if the server goes down for some
reason other than catastrophic failure of multiple drives, the more recent backup of the data files
can be used, meaning a maximum of 3 hours of lost data. If there is a catastrophic drive failure,
then the previous evening’s tape can be used, minimizing the loss to one day’s data. Of course,
these procedures can be tailored to your situation and data value.
1 Make sure backup copies aren’t damaged or inaccessible. Verify that they are functioning properly
before you need them. Run diagnostic tools on your hard drive and your backup files regularly.
1 Ensure that you can restore an entire set of files from backup copies.
1 Regularly export the data to protect against file corruption.
1 Protect the backup media itself. Store backups in a separate and fire-proof location.
1 Assign backup administrators who can retrieve files, in case the network administrator is
unavailable.
Chapter 6 | Protecting files 123
1 Plan for redundancy. If the power goes off, a universal power supply (UPS) should sustain
power for at least 15 minutes, enabling you to safely close all files. If the power can’t be restored
in a timely fashion, consider using a generator to supply power to servers. Also consider power
sources for routers and firewalls. Will communication be a problem if your Internet access is
interrupted for 48 hours or longer?
1 Consider how you will continue to provide services if an intruder takes down your database
server and that server can’t be restored to its previous condition.
1 Evaluate additional scenarios that could occur, and create a plan to respond to each one.
Also, network administrators should assess risks to data systems and business-critical functions.
For example, consider:
1 Theft of data or theft of proprietary intellectual property.
1 Disruption, theft, or damage to network infrastructure such as servers, networks, data storage,
or data backup storage. Damage can be caused by password crackers or by other types of
malicious sabotage and destruction. Most incidents originate from within the organization.
1 Disruption or damage to the organization infrastructure such as building fires, environmental or
biological hazards, floods, and so on.
1 Disruption or damage to the public infrastructure, including electrical power,
telecommunications (voice and data), transportation grids (roadways, buses, trains) caused by
environmental conditions, or severe weather such as tornadoes or floods.
FileMaker Pro provides two mechanisms for handling databases that might be damaged:
consistency checks and file recovery. Consistency checks occur automatically, if needed, when
the file is opened. You can also choose to verify the consistency of a file that you suspect is
damaged. You can also have FileMaker
Pro attempt to recover a damaged file.
Important In the event of a server failure, such as an unexpected loss of power, hard drive
failure, or software failure, use the backup files. Any system failure causing FileMaker
Server to
shut down inappropriately can result in corrupted files if cached data was not written to disk and
the files were not closed properly. Even if the files reopen and go through a consistency check or
recovery (initiated by either FileMaker
Pro or you), corruption might be buried in the file. File
recovery cannot guarantee that problems have been fixed.
Installing, running, and upgrading antivirus software
Because most computers have Internet access, they are vulnerable to harm, such as from viruses
being transmitted through email attachments. Make sure all employees run antivirus checking
software regularly, and that they are aware of typical virus warning signs. Employees should scan
all files before copying or downloading them to their computers, and they should never open
unsolicited attachments, even if they’re from someone they know.
While antivirus software is essential in protecting your systems and data, some caution should be
observed in how they are used on computers that host FileMaker
Pro databases.
Antivirus programs sometimes lock bytes within a file when they scan for viruses. These locks can
cause the operating system to return an error when FileMaker
Pro or FileMaker Server try to write
data to the file, which sometimes causes the file to be flagged as damaged and closed.
Chapter 6 | Protecting files 124
This situation also applies to files that FileMaker Server uses as backup targets. If the backup file is
being scanned by antivirus software when a scheduled backup occurs, the destination file might be
locked. This causes the backup process to fail, which may result in data loss. This same data loss
issue applies when an open, non-shared FileMaker
Pro database file is scanned by antivirus software.
When running antivirus software on computers that host FileMaker Pro databases, follow these
recommendations:
1 Do not run virus protection software on open or hosted databases. First, close the databases,
then run the virus protection software.
1 When you scan your computer for viruses, do not scan the Databases folder and subfolders or
any folder that contains files that actively hosts files through FileMaker
Server or FileMaker Pro.
Instead, set your antivirus software to scan your database backup destination folder and make
sure your antivirus scan schedule does not coincide with your FileMaker
Server backup
schedule. Wait until databases are completely backed up before scanning them.
Chapter 7
Using FileMaker Pro Advanced
FileMaker
®
Pro Advanced includes advanced development and customization tools designed
especially for solution developers. You can use either FileMaker
Pro or FileMaker Pro Advanced
to create and test your solutions.
FileMaker Pro Advanced features
In addition to all the features that are available with FileMaker Pro, FileMaker Pro Advanced
includes:
1 Developer Utilities—for creating, customizing, and deploying runtime solutions
1 Custom Functions—for creating custom functions for use anywhere within the solution
1 Custom Menus—for creating customized menus for the solution
1 Script Debugger—for systematic testing and debugging of FileMaker scripts
1 Data Viewer—for monitoring fields, variables, and calculations
1 Database Design Report—for publishing detailed documentation on structures or schemas of
databases
See Help for detailed, comprehensive information and step-by-step procedures about using
FileMaker
Pro Advanced.
Developer Utilities
The Developer Utilities let you:
1 produce a stand-alone runtime solution that users can access without running FileMaker Pro or
FileMaker
Pro Advanced
1 rename a set of files and automatically update the internal links to related files and scripts
1 remove administrative access from all accounts and prevent users from modifying most design
or structural elements of your files
1 display your files in Kiosk mode
1 add the FileMaker Pro filename extension to a set of non-runtime files
1 create an error log for processing errors
1 encrypt files to protect them from unauthorized access while they are being stored on disk
Runtime solutions
The Developer Utilities create a copy of your files, and bind the database file or files to a runtime
application with a name that you specify.
To create a runtime solution:
1. Close the files you want to customize.
Chapter 7 | Using FileMaker Pro Advanced 126
2. Choose Tools menu > Developer Utilities.
3. Click Add to locate the files you want to customize.
4. Choose a location for the runtime solution.
5. Select options for the runtime solution.
6. Click Create.
Binding the solution
To bind database files into a runtime database solution:
1. In the Specify Solution Options dialog box, select Create Runtime Solution application(s).
2. Name your runtime solution.
3. Create a bindkey.
The bindkey links the runtime application to the database files and ensures that the bound files
will only open in the appropriate runtime application. The binding key is case-sensitive.
4. Add a company logo or other custom image to the closing splash screen.
5. Click Create.
See Help for information about the differences between the runtime application and
FileMaker
Pro.
Converting and upgrading previous solutions
If you have developed a FileMaker Pro runtime solution using the Solutions Development Kit
(SDK) for FileMaker
Pro 3.0 or earlier, the Binder utility in the FileMaker Pro 4.0 Developer Edition,
or the Developer Tool in FileMaker Developer 5.x and 6.0, you can upgrade your solution and
provide your users with the converted files. Files bound to a runtime application using the earlier
tools must be rebound using the Developer Utilities.
After you have converted the files, you can upgrade them to take advantage of newer
FileMaker
Pro and FileMaker Pro Advanced features. If necessary, create scripts to import users’
existing data from the old runtime solution into the new, upgraded solution. Use the Developer
Utilities to bind the solution files into a new, upgraded runtime solution.
Distribute the new upgraded runtime solution and provide instructions for how users can upgrade
their files by converting the old files in the new runtime application and importing their data.
Distributing runtime solutions
The final steps in developing your runtime solution are to bundle all the necessary files together,
choose how you will distribute your solution—for example, on media or over a network—and
provide your users with documentation for installing your solution. In addition, your documentation
should include instructions for starting the runtime application and what to do if a file is damaged.

Chapter 7 | Using FileMaker Pro Advanced 127
Organizing solution components
When you bind your files into a runtime solution, the Developer Utilities create a new solution
folder and place the runtime application, the bound primary and auxiliary database files, and an
Extensions folder inside it. For Windows runtime solutions, there are also required Dynamic Link
Library (DLL) files.
Note When you move multiple files into one folder to create a runtime solution, be aware that
your internal links are affected. For this reason, every data source must include a path that is just
the filename of the file being referenced. Although the runtime application will check other data
sources, it will then be able to find the file in the same folder in which it resides. You can still keep
any absolute or relative paths in the same data source reference in case the files are also used in
FileMaker
Pro or FileMaker Pro Advanced.
Important These files and folders must not be renamed.
If your runtime solution requires custom files, you should provide the files with the runtime files.
The location of plug-in files depends on whether plug-ins need to be available to multiple versions
of FileMaker
Pro.
If a developer uses a font not found on a user’s system, the runtime application will make a font
substitution. If a font is included with the runtime, provision should be made for its installation
through the installer program.
Testing before and after creating your solution
You should verify the functionality of your solution by testing it thoroughly before and after you
customize it with the Developer Utilities.
To ensure the quality of your custom solution:
1 Verify every function and option in your solution. If you’re developing a solution for both
platforms, test it in both Windows and OS X.
1 Make sure your runtime solution does not use a standard FileMaker Pro feature that is hidden
or disabled in the runtime application.
Windows solution folder OS X solution folder
Runtime application
Runtime application
package
Bound primary and
auxiliary solution files
Bound primary and
auxiliary solution files
Extensions
Dictionaries
DLLs generated during
binding
Example of Windows and OS X solution contents for distribution
Extensions
Dictionaries
Language
resource folders
Chapter 7 | Using FileMaker Pro Advanced 128
1 Verify that all scripts and buttons work as expected. This is especially important if you’re
displaying your solution in Kiosk mode.
1 Verify your installation procedures and test other instructions in the documentation.
1 Verify that your layouts display well on monitors with different color capabilities and resolutions
and on the smallest size monitor your users may be using.
1 Test your runtime solution with actual data. This is especially important if users are upgrading
from earlier versions of the runtime application and need to import data into new solution files.
1 Make sure all the auxiliary files and DLLs (Windows) are present.
1 Show your solution to intended users to uncover any usability issues.
1 Install your bundled files on a completely different computer to verify that all the files associated
with the primary file can be found.
1 If you’re assigning passwords or permanently removing full access privileges, test all access
levels.
1 Make sure your solution contains an About layout that notifies users of the level of access
you’re providing.
Important You should keep an unbound version of any runtime solution files, especially if you’ve
permanently removed full access privileges.
Distributing updates to runtime solutions
If you make feature enhancements or modifications to the primary bound file of your runtime
solution, you can distribute the updated file to your users without rebinding it. If you change the
filename of the primary file, however, you’ll need to rebind the file and distribute a new version of
the runtime application along with the updated file.
To distribute new or updated auxiliary files for your runtime solution, bind them first using the
original binding key. If you are distributing a new auxiliary file that requires new data sources in the
main file or that requires other files to interact with it, you must update all files that have been
modified.
If you forget the original binding key for your runtime solution and want to update or add a file,
you’ll need to rebind all the files with a new binding key and redistribute the entire solution.
To distribute an updated primary file:
1. Open the original primary file from your copy of the runtime solution in FileMaker Pro Advanced.
2. Make the changes to the primary file.
3. If necessary, create an Import script so users can import their existing data into the new primary
file.
4. Send your users a copy of the new primary file with instructions to replace the old primary file
in the runtime solution folder.
Chapter 7 | Using FileMaker Pro Advanced 129
To distribute a new or updated auxiliary file:
1. In FileMaker Pro Advanced, create the new auxiliary file or open the original auxiliary file
(before it was bound), and make changes as required.
2. If necessary, create an Import script so users can import their existing data into the new file.
For more information about importing data into upgraded runtime solutions, see Help.
3. Use the Developer Utilities to rebind all the files in the runtime solution and include the new or
updated auxiliary file.
Use the same binding key that you used for the primary file.
4. Send your users a copy of the new or updated auxiliary file along with instructions to place it in
the runtime solution folder, replacing the old file if appropriate.
As long as the binding key has not changed, you don’t need to redistribute the runtime
application or other solution files.
Kiosk mode
Kiosk mode is a way of displaying your solution or runtime solution on a full screen, without any
toolbars or menus. As the name suggests, Kiosk mode can be used to present your solution to
users as an information kiosk. You can design your solution to run through a touch screen.
When you create a solution to run in Kiosk mode, you need to provide navigation for your solution
and the ability for users to quit your solution.
Custom functions
Use the Custom Functions feature to create functions that can be reused anywhere in a file and
copied or imported to other FileMaker
Pro files. Once formulas are written for the function, they
don’t have to be rewritten to be applied to other fields or used in other scripts.
You can maintain and edit custom functions and the formulas they contain in one central location.
Any change made to the custom function will be copied to all instances where that custom function
has been used.

Chapter 7 | Using FileMaker Pro Advanced 130
To create a custom function:
1. Choose File menu > Manage > Custom Functions.
2. Click New.
3. In the Edit Custom Function dialog box, type a name for the function and build a formula.
Custom menus, menu items, and menu sets
With FileMaker Pro Advanced, you can create custom menus, menu items, and menu sets for
your solutions. You can:
1 create a menu or edit an existing menu
1 duplicate or delete a menu
1 add, duplicate, or delete menu items
1 specify menu item properties, such as display title, shortcut, and action
Functions
list
Formula box
Parameters list
Your custom
parameters appear in
this space

Chapter 7 | Using FileMaker Pro Advanced 131
About custom menus
You can customize menus by:
1 editing a copy of a standard FileMaker menu. Use this method to make minor changes to
existing menus—for example, to modify the properties of a few menu items.
1 starting with an empty menu. Use this method to make significant changes to menus—for
example, to add menus and change menu item properties.
About custom menu items
After you create a menu, you can create menu items. You can also create or edit menu items that
are copies of the Standard FileMaker menus. Menu items can be commands, submenus, or
separators. You can create a menu item that is based on a standard FileMaker command or you
can create a menu item that initially does not have an assigned command.
When you base a menu item on a FileMaker command, the menu item inherits all the properties
of that command. You can override properties (menu item name, keyboard shortcut, or action) to
customize the menu item.
When you create a menu item that does not have an assigned command, an <unknown> menu
item appears in the Menu Items list in the Edit Custom Menu dialog box. You can then customize
this menu item’s properties.
Menu
Menu bar
Menu set for this layout
Menu item
Separator
Submenu
Menu display title
Custom menu terminology

Chapter 7 | Using FileMaker Pro Advanced 132
About custom menu sets
Custom menu sets are collections of menus that appear in the FileMaker Pro application menu
bar. You can create custom menu sets to include only the menus you require. After you create
menu sets, you can:
1 specify menu sets for individual layouts
1 create scripts that change menu sets
1 change the default menu set in a solution file’s menu bar
1 switch menu sets temporarily using the FileMaker Pro Advanced Tools menu
Debugging scripts
Use the Script Debugger to systematically test and debug FileMaker scripts.
To run scripts in debug mode:
1. Select Tools menu > Script Debugger.
The Script Debugger opens.
2. Run your script.
You can view sub-scripts when you step through scripts in the Script Debugger. For example, if
Script A calls Script B, which then calls Script C, you can view the steps in all three scripts.
To set or clear a breakpoint, click the line number to the left of the script step. Breakpoints allow
the Script Debugger to execute large sections of a script, pausing only to inspect the section
marked with a breakpoint.
The steps of the script you ran
appear here
Double-click a paused script in the
Call Stack list to edit the script
Select if you want scripts to pause
when errors are encountered

Chapter 7 | Using FileMaker Pro Advanced 133
Monitoring expressions
Use the Data Viewer to monitor expressions like field values, local and global variables, and
calculations. You can monitor these expressions while running scripts or while testing them in the
Script
Debugger.
To monitor the currently running script:
1. Choose Tools menu > Data Viewer, or click in the Script Debugger.
2. Click the Current tab.
To monitor expressions:
1. In the Data Viewer, click the Watch tab.
Click to view
restricted-access
expressions
Click a column
heading to sort
Drag an arrow up
or down to change
the order

Chapter 7 | Using FileMaker Pro Advanced 134
2. Perform the following tasks:
1 To add an expression, click . In the Edit Expression dialog box, build an expression, then
click Monitor to add the expression to the Data Viewer.
1 To edit an expression, double-click the expression in the Watch tab or select an expression
and click
. Define or edit the expression. Then, click Evaluate Now to display the result
of the expression or click Monitor to add the expression to the Watch list.
Documenting database schemas
With the Database Design Report (DDR) feature you can:
1 examine a textual representation of your database schema
1 gather statistics on the structure of your database
1 produce reports in HTML or XML for any databases that are currently open, either locally or on
a network
1 use the information in the report to re-create the structure of your database if you lose the
original database files
1 troubleshoot missing references, broken relationships, calculations, and more
Select mathematical and
text operators
Choose field
references
Formula
Select comparison and
logical operators
Choose the way
functions are listed in
this dialog box
Click to evaluate the
expression
Click to add the
expression to the
Data Viewer
Result of the
expression
Table name
Select
functions to
use in the
expression

Chapter 7 | Using FileMaker Pro Advanced 135
To create a database design report:
1. Choose Tools menu > Database Design Report.
2. Set options for the report.
3. Click Create.
Select the files and
tables to include
Select the elements to
include
Choose the format of
the published report
Choose whether to
open the report when
it’s completed
Index
Symbols
– 43
^ 43
_ 43
, 43
; 43
: 43
:: 43
" 43
, 48
" " 28
( 43
, 48
) 43
, 48
[ 43
] 43
} 43
* 43
/ 43
& 43
+ 43
< 43
= 43
> 43
$ 43
≤ 43
… 43
≥ 43
A
Access privileges. See Accounts; Privilege sets
Access via FileMaker Network 99
, 120
Accounts
creating and editing 117
described 111
External Server account 111
, 118
for hosted files 111
passwords 116
predefined 112
viewing 117
Active record 21
Adding
See also Defining
fields 43
records 22
related records 23
, 95
tables 53
Admin account 114
Aligning
objects 68
text 77
Antivirus software, and database management 123
Apple Open Directory 118
Application preferences 36
Area charts 82
Asian text, formatting fields for 77
Attributes, text 76
Authentication
Apple Open Directory 118
described 111
via external server 118
Windows domain 118
Auto-complete 74
Automating tasks (scripts) 11
Auxiliary files, updating 129
B
Backups
and antivirus software 123
guidelines for 122
, 128
scripts for files 36
Badges in fields, for quick finds 29
Bar charts 81
Baseline offset 77
Baselines, text 77
Binding key
described 126
updating runtime solutions 128
Blank layouts 56
Body part 80
Boolean values
described 44
setting 51
Bottom navigation part 80
Break fields 80
Browse mode
creating charts in 82
described 18
finding data in 28
Browsers, working with published solutions in 109
Browsing records 19
Bubble charts 82
Buttons
including in tab order 24
popover 67
C
Calculation fields
creating 48
described 44
formulas 48
stored and unstored results 51
, 52
Calculations
See also Calculation fields
field references to related fields 48
formatting 76
troubleshooting 133
137
Calendars, displaying in fields 74
Characters
maximum in fields 25
not allowed in field names 43
Charting data
creating charts 82
described 81
editing charts in Layout mode 83
quick charts 82
Checkbox sets, displaying fields as 74
Clients
described 99
performing tasks 102
saving files 99
Closing windows and files 16
Color, changing for text 77
Column charts 81
Columns
changing width 65
printing records in 63
resizing in tables 26
Comma-separated text format 103
Comparison operators 48
Constant values 48
Container fields
See also Fields
described 10
, 44
formatting 76
inserting files into 25
storage options for 51
Context menus, choosing from 13
Control styles for fields 74
Copying
files 17
records 22
related records 23
Creating. See Adding; Defining
Currency, formatting 76
Current record 21
Custom functions, creating 130
Custom menus 131
, 132
D
Data
charting 81
described 13
entering automatically 22
, 51
entering in fields 25
formatting 68
importing and exporting 103
privileges for sharing 111
viewing in forms, lists, or tables 19
Data entry 25
Data Entry Only privilege set 113
Data sources
described 108
updating 128
Data types
See also Field types
and calculation results 49
Data Viewer 133
Database Design Reports (DDR) 134
Database schemas, in Database Design Reports 134
Database statistics 134
Database structure, re-creating 134
Databases
See also Files; Solutions
described 8
, 13
planning 37
printing 35
protecting 110
Databases, relational. See Relational databases
Date fields
described 44
entering and editing values in 25
formatting 76
four-digit years 25
, 51
Dates
See also Date fields
displaying calendars 74
entering data 25
four-digit years 51
typing in 25
DDR (Database Design Reports) 134
Defining
See also Adding
accounts 117
calculation fields 48
databases 43
fields 43
lookups 96
passwords 116
privilege sets 119
summary fields 49
tables 53
value lists 74
Defining fields
described 43
in Field Picker dialog box 46
in Table View 47
Deleting
data 25
fields from a layout 74
find requests 32
related records 24
, 95
Developer Utilities
creating runtime solutions 125
described 125
Displaying shortcut and context menus 13
Distributing runtime solutions
described 126
distributing updates 128
Document preferences 36
Dragging fields to a layout 73
Drop-down calendars, displaying fields as 74
Drop-down lists, displaying fields as 74
138
Duplicating
records 22, 27
related records 23
tables in the relationships graph 93
Dynamic guides, for designing layouts 70
Dynamic Link Libraries (DLLs) 127
Dynamic reports, creating in Table View 27
, 49
E
Edit boxes, displaying fields as 74
Elements. See Objects
Email, sending from FileMaker Pro or through SMTP 109
Encrypted connection (SSL) to host 101
Entering data
automatically 51
typing in fields 25
Envelopes layouts 58
Envelopes, printing 58
Excel format
importing and exporting to 103
saving data as 109
Exchanging files
importing and exporting 103
relational databases 84
with other applications 103
Exporting
described 103
file formats supported 103
formatting 108
Expressions, monitoring 133
Extended privileges
described 111
viewing 120
External data sources 108
External Server account 111
, 118
F
False result 44, 51
Favorite files, opening 15
Field behavior 24
, 78
Field labels, placing on a layout 73
Field names, guidelines 43
Field Picker dialog box, for defining fields 46
Field tool 73
Field types
and calculation results 49
described 44
Field values
deleting 25
described 15
entering and editing 25
entering automatically 51
Field/Control tool 73
Fields
adding to a layout 72
creating and changing 43
defining 43
, 46, 47
deleting from a layout 74
described 14
displaying 9
, 54
dragging to a layout 73
entry options 50
, 74
formatting data 76
Furigana 51
global 53
indexing 51
, 52
merge fields 75
monitoring 133
naming 46
options for 51
placing on a layout 72
placing related on a layout 75
removing from a layout 74
restricting data entry 78
selecting 24
, 71
stored and unstored results 51, 52
text baselines 77
types 44
typing in 25
validation options 51
File formats supported for importing and exporting 103
File options 36
File references. See Data sources
File sharing, enabling 99
FileMaker Developer. See FileMaker Pro Advanced
FileMaker documentation 7
FileMaker Go
and sharing files 98
designing layouts for 70
extended privileges for 112
layout themes for 61
privileges for 119
FileMaker Pro
documentation information 7
file format 103
product overview 8
FileMaker Pro Advanced
described 125
upgrading from earlier versions 126
FileMaker Pro format 103
FileMaker Server
described 118
privileges for 112
, 120
recommended use 98
uploading files to 103
FileMaker WebDirect
described 109
extended privileges for 112
privileges for 119
139
Files
See also Databases; Solutions
accounts 111
authorizing access to protected files 120
backing up 36
closing 16
copying 17
creating 42
described 8
, 14
encrypted connection (SSL) to host 101
exporting to 107
hosted 101
naming 42
opening 15
, 101
planning 37
privilege sets 111
protecting 110
publishing on the web 109
saving 17
shared
on web 109
planning security for 115
Find mode 18
Find requests
See also Finding records
described 29
editing 32
operators in 30
repeating 31
Finding records
all records 31
described 28
omitting records 30
quick finds 28
related fields and records 31
saving and sending as snapshot link 11
, 29
showing all records 31
Folder structure for runtime solutions 127
Fonts not on user’s system 127
Footer part 80
Form letters 75
Form View 19
, 20
Formatting
calculations 76
export data 108
fields 76
import data 103
layout objects 68
paragraphs 77
text 76
Formulas
calculation fields 48
for custom functions 130
monitoring 133
Found set
See also Finding records
described 18
, 29
omitting records from 30
saving and sending as snapshot link 11
, 29
switching with omitted set 32
Four-digit years
in date fields 25
, 51
in timestamp fields 25
Full Access privilege set 113
, 120
Functions
custom 129
described 48
monitoring in formulas 134
Furigana fields 51
G
Getting Started tour 8
Global storage options 53
Grand summaries 80
Grid, for designing layouts 69
Groups. See Accounts; Privilege sets
Guides, for designing layouts 69
, 70
H
Header part 80
Help, getting for FileMaker Pro 7
Hiding records 32
Highlighting text 77
Horizontal charts 81
Host
described 99
encrypted connection (SSL) 101
FileMaker Server 98
performing tasks 102
saving files 99
solutions on the web 109
HTML format for Database Design Reports 134
HTML table format 103
I
Importing
described 103
file formats supported 103
layout themes 60
recurring imports 12
terminology 104
Indexing fields 51
, 52
Inserting files into container fields 25
Inspector
described 66
opening 68
Intranet
See also Web publishing
files shared on 109
J
JDBC
field name considerations 43
privileges for 112
, 119
Join expressions. See Relationships
Join fields. See Match fields
140
K
Key fields. See Match fields
Kiosk solutions, creating 129
L
Labels
field 73
layouts for 57
mailing 58
part 78
printing 58
vertical 57
Labels layouts 57
Launch Center
creating solutions 41, 42
opening files 15
, 101
Layout background, setting styles for 61
Layout bar 17
, 18
Layout folders, managing 55
Layout mode
creating charts in 82
described 18
Layout objects. See Objects
Layout parts
described 80
grand summary 80
setting styles for 61
subsummary 80
Layout pop-up menu 17
, 54
Layout themes
changing 42
described 60
importing 60
Layouts 57
adding fields 72
changing theme 60
changing width 42
charting data 81
columns 64
, 65
creating 54
described 9
, 54
managing layouts and layout folders 55
panel controls on 66
popovers on 67
printing 35
testing 128
themes 60
tools 66
types 56
unit of measure 69
views of 19
Leader, setting character for paragraphs 77
Limits
characters in fields 25
field names 43
Line charts 81
List View 19, 20
List view layouts 58
Locked objects 71
Locking shared records 102
Lookups
creating or changing 96
described 84
terminology 87
M
Macros (scripts) 11
Mail merge, using merge fields 75
Mailing labels 57
Margins, displaying in Preview mode 34
Match fields
See also Fields
described 87
, 88
in import update 105
Matching records, updating 105
Mathematical operators 48
Maximum characters in fields 25
Menu sets, customizing 132
Merge fields
described 59
placing on a layout 75
Merge format 103
Microsoft Excel format
importing and exporting 103
saving data as 109
Mode pop-up menu 18
, 54
Modes 18
Moving
field to field 24
record to record 21
Multimedia files 44
N
Network security guidelines 122
Networks
cross-platform 12
, 98
FileMaker Server 98
New Layout/Report assistant 54
Non-shared files 116
Number fields
See also Fields
described 44
entering and editing values in 25
formatting 76
O
Objects, layout
aligning 68
, 69, 70
creating 66
described 66
formatting 68
locked 71
selecting 71
setting styles for 61
141
ODBC
overview 104
using FileMaker as client
described 108
supplemental fields 50
using FileMaker as data source
field name considerations 43
privileges for 112
, 119
Omitting
fields during printing 75
records from the found set 30
related records 31
Opening files 15
, 101
Operators
comparison 48
in find requests 30
mathematical 48
relational 87
, 91, 95
Options
field 50
file 36
OS X runtime application package 127
P
Page breaks
showing or hiding in Layout mode 69
showing or hiding in relationships graph 94
viewing in Preview mode 34
Page margins, viewing in Preview mode 34
Page numbers
in layout parts 58
viewing in Preview mode 34
Panel controls
described 66
including in tab order 24
Paragraphs, formatting 77
Parts. See Layout parts
Passwords
defining 116
protecting files with 116
related files, planning 41
when opening a file 15
PDFs, saving data as 109
Photos in container fields 44
Picture fields. See Container fields
Pie chart icon in status toolbar 28
Pie charts 81
Planning
file security 114
relational databases 37
solutions 37
Plug-ins, installing 127
Pointer tool (Selection tool) 71
Pointers to files. See Relationships
Popovers
described 67
including in tab order 24
Pop-up menus, displaying fields as 74
Portals
See also Relational databases
adding records 23
deleting records 24
described 9
, 87
placing related records 75
selecting 71
selecting records 21
Positive/negative column charts 81
Preferences
application 36
file 36
Preview mode
described 18
, 34
displaying page breaks, margins, and numbers 34
Previewing printing. See Printing
Previewing columns 63
Primary file, updating 128
Primary keys. See Match fields
Print area, viewing 34
Printing
Asian text 77
described 33
envelopes 58
information about tables and fields 35
labels 58
previewing 34
records 35
records in columns 63
Privilege sets
defining 119
described 111
predefined 113
Publishing solutions on the web 109
Q
Quick charts, creating 27, 82
Quick finds
See also Finding records
badges in fields 29
described 28
setting up 29
R
Radio button sets, displaying fields as 74
Read-Only privilege set 113
Recent files, opening 15
Record locking 102
142
Records
active 21
adding 22, 27, 104
browsing 19
, 27
copying 22, 27
deleting 27
described 15
duplicating 22
, 27
exporting 107
finding 28
hiding 32
locked 102
matching 105
moving through 21
printing in columns 63
selecting 21
sorting 27
, 33, 95
viewing as forms, lists, or tables 19
Recurring imports 12
Related fields
See also Fields; Relational databases
calculations 48
described 87
on layouts 73
planning 40
Related files, restricting access 41
Related records
See also Records; Relational databases
adding 23
, 95
copying 23
deleting 24
, 95
described 87
duplicating 23
finding and omitting 31
in portals 75
sorting 95
Related tables
described 87
planning 37
Relational databases
and portals 87
described 14
, 84
match fields 87, 88
planning 37
, 84
related tables 37
, 87
terminology 87
Relational operators 87
, 91, 95
Relationships
See also Relational databases
changing 94
comparative 91
creating 94
described 87
multi-criteria 90
planning 40
returning range of records 92
self-joining 93
single-criteria 89
Relationships graph
creating relationships 94
described 87
, 88
text notes in 94
Repeating find requests 31
Report layouts 58
Reports
See also Layouts; Subsummaries
creating 54
database 134
previewing 34
records in columns 63
with grouped data 35, 58
Retrieving data from other files. See Exchanging files
Reverting find requests 32
Rulers, showing and hiding 69
Runtime application, compared to FileMaker Pro 126
Runtime solutions
creating 125
documenting 126
preparing files 125
updating 128
upgrading 126
S
Saving
data automatically 17
files 17
found set as snapshot link 11
shared files 99
to Excel and PDF formats 109
Scatter charts 82
Schemas, database, documenting 134
Screen stencils 70
Script triggers 11
Scripts 11
Secondary files. See Relational databases
Security, file
network guidelines 122
operating system guidelines 121
planning 114
, 121
Selecting
fields 24, 71
files in Launch Center 15
objects 71
records 21
text 71
Selection tool 71
Self-joins 93
Server. See Host; FileMaker Server
Settings. See Preferences
143
Shared files
See also Networks
accounts 115
clients 99
host 99
limitations 98
on web 109
privilege sets 115
saving 99
setting up privileges for 111
Shortcut menus, choosing from 13
Simple Mail Transfer Protocol (SMTP), sending email
through 109
Single-page form layout. See Table View
Slide controls 66
Snapshot links, saving and sending found set as 11
, 29
Solutions
See also Databases; Files; Runtime solutions
creating from Starter Solution 41
creating new 42
described 8
opening in Launch Center 15
publishing on web 109
Sorting records
described 33
in Table View 27
related 95
Sound files 44
Source file (relationships) 87
Source table (relationships) 87
Stacked bar charts 81
Stacked column charts 81
Starter Solutions, designing solutions with 8
Statistics, database 134
Status toolbar 18
, 66
Storage options for container fields 51
Stored results 51
, 52
Structure, database 134
Styles, setting for objects, parts, layout background 61
Subforms. See Portals
Subsummaries
See also Reports; Summary fields
creating reports 58
parts, described 80
printing 34
, 35
Subtotals. See Subsummaries; Summary fields
Summary fields
creating 49
described 44
, 49
dynamic reports in Table View 49
on layouts 80
Summary parts. See Subsummaries
Supplemental fields 50
Symbols, and field names 43
T
Tab controls 66
Tab order 24
Tabbing into fields 24
Table View 19
adding records 27
changing column order and size 26
copying records 27
creating quick charts 27
defining fields in 47
defining summary fields 49
deleting records 27
described 20
duplicating records 27
dynamic reports in 27, 49
sending email messages based on record data 27
sorting records 27
working with data and records in 26
, 27
Tables
defining 53
described 14
importing data into new 104
naming 53
table occurrences 88
Tabs
inserting in fields 25
setting position and alignment 77
Tab-separated text format 103
Testing solutions 127
Text
See also Fields
aligning with checkboxes and radio buttons 77
attributes 76
changing color 77
fields 44
formatting 76
highlighting 77
rotating Asian text 77
selecting 71
Text baselines, specifying options for 77
Text fields
described 44
entering and editing values in 25
Text notes in relationships graph 94
Themes, layout
changing 42
, 60
described 60
importing 60
managing 61
Time fields
described 44
entering and editing values in 25
formatting 76
Timestamp fields
described 44
entering and editing values in 25
formatting 76
four-digit years 25
Title header and footer parts 80
144
Tools
Field tool 73
Field/Control tool 73
for designing layouts 66
Popover Button tool 67
Selection tool 71
Slide Control tool 67
status toolbar 18
Tab Control tool 66
Top navigation part 80
Touch screens, designing solutions for 129
Triggers, script 11
Troubleshooting
calculations 133
fields 133
schema, using Database Design Report 134
variables 133
True result 44
, 51
Type-ahead feature 74
U
Unit of measure, changing 69
Unstored results 51
, 52
Updates to runtime solutions 128
Updating existing data during import 104
Upgrading runtime solutions 126
Uploading files to FileMaker Server 103
V
Validating field values 51
Value lists
defining 50
described 74
sorting by 27
Variables
monitoring 133
symbols for 43
Vertical charts 81
Vertical Labels layouts 57
Vertical writing 77
Viewing
accounts 117
extended privileges 120
page breaks, margins, and numbers in Preview mode 34
print area 34
records as forms, lists, or tables 19
Views of layouts 19
, 20
Virtual results 52
W
Web publishing
and naming fields 43
described 109
Web viewer 10
Windows
closing 16
opening multiple 16
Windows domain 118
Windows runtime application package 127
X
XML
importing and exporting to 103
privileges for 112
, 119
XML format 103
described 134
for Database Design Reports 134
Y
Years
four-digit in date fields 25
, 51
four-digit in timestamp fields 25
